Filtering Trusted Vendors List Changes Logs
Comodo Client Security allows you to create custom views of all logged events according to user defined criteria. You can use the following types of filters:
Clicking on the handle at the bottom enables you to filter the log entries for a selected time period:
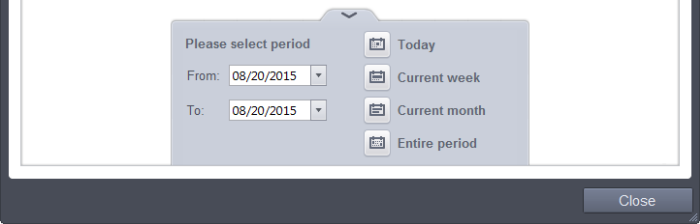
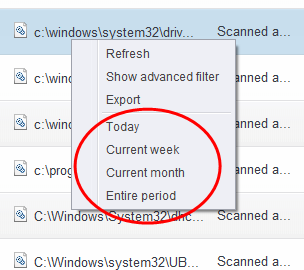
- Today - Displays all logged events for today.
- Current Week - Displays all logged events during the current week. (The current week is calculated from the Sunday to Saturday that holds the current date.)
- Current Month - Displays all logged events during the month that holds the current date.
- Entire Period - Displays every event logged since Comodo Client Security was installed. (If you have cleared the log history since installation, this option shows all logs created since that clearance).
- Custom Filter - Enables you to select a custom period by choosing the 'From' and 'To' dates under 'Please Select Period'
Alternatively, you can right click inside the log viewer module and choose the time period.
You can further refine the displayed events according to specific filters. The following filters are available for 'Trusted Vendors List Changes' logs:
- Vendors - Lists all trusted vendors that ships to all users with CCS
- Modifier - Indicates the user that has added the application to the trusted list and allowed to run
- Action - Indicates action taken by Trusted Vendors in response to the event
To
configure Advanced Filters for Trusted Vendors Logs
-
Click the funnel button
from the title bar. The Advanced Filter interface for 'Trusted Vendors List Changes' logs will open.
-
Select the filter from the 'Advanced Filter' drop-down and click 'Add' to apply the filter.
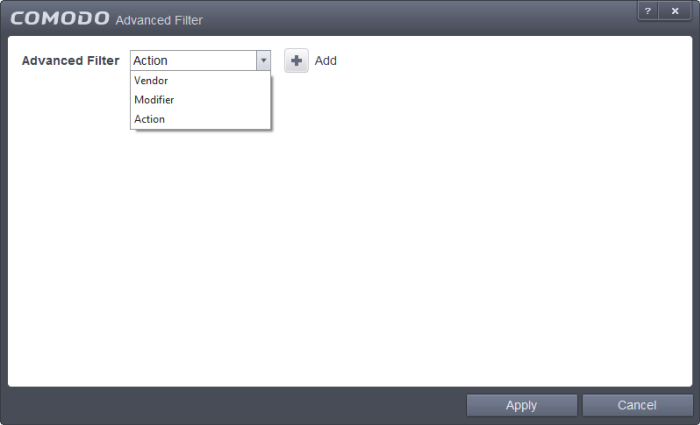
You have 3 categories of filters that you can add. Each of these categories can be further refined by either selecting or deselecting specific filter parameters or by the user typing a filter string in the field provided. You can add and configure any number of filters in the 'Advanced Filter' dialog.
Following are the options available in the 'Add' drop down menu:
i. Vendor: The 'Vendor' option enables you to filter the log entries related to a specific vendor. Selecting the 'Vendor' option displays a drop-down field and text entry field.
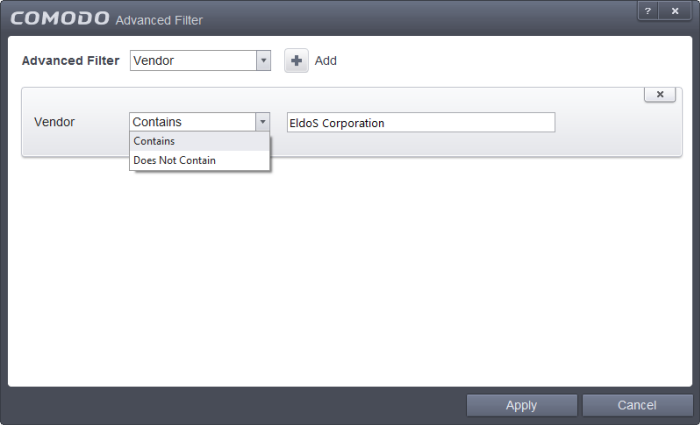
-
Select 'Contains' or 'Does Not Contain' option from the drop-down field.
-
Enter the text in the name of the vendor that needs to be filtered.
For example, if you select 'Contains' from the drop-down and enter 'EldoS Corporation', then all events containing the entry 'EldoS Corporation' in the 'Vendor' field will be displayed. If you select 'Does Not Contain' and enter the phrase 'EldoS Corporation', then all vendors that do not have the entry 'EldoS Corporation' in the 'Vendor' field will be displayed.
ii. Modifier: The 'Modifier' option allows you to filter log entries based on the entity that is responsible for the log. Selecting the 'Modifier' option displays a drop-down box and a set of specific filter parameters that can be selected or deselected.
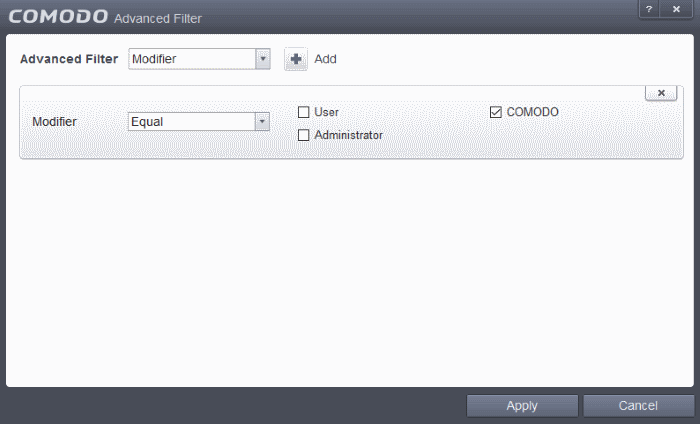
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Next, select the entities who made the change. The parameters available are:
- User
- COMODO
- Administrator
For example, if you chose Equal in the drop-down and selected the 'User ' checkbox, then only log entries generated by users will be displayed.
iii. Action: The 'Action' option allows you to filter log entries based on actions executed (objects added or removed).
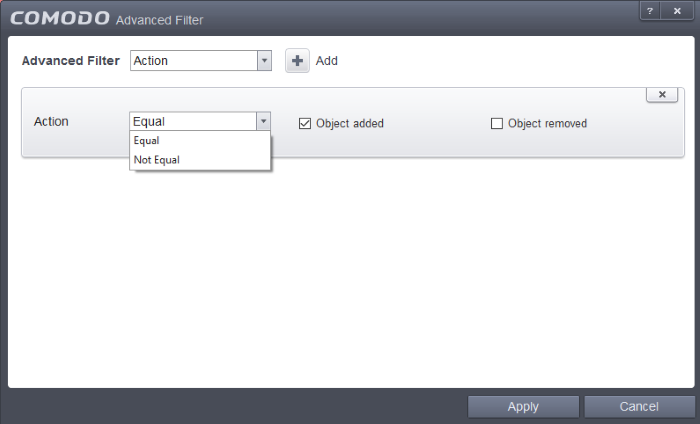
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Next, select the the type of action. The parameters available are:
- Object added
- Object removed
For example, if you choose Equal in the drop-down and select 'Object Added' checkbox, then only log entries with the value 'Object Added' in the 'Action' column will be displayed.
|
Note: More than one filter can be added in the 'Advanced Filter' pane. After adding one filter type, select the next filter type and click 'Add'. You can also remove a filter type by clicking the 'X' button at the top right of the filter pane. |
- Click 'Apply' for the filters to be applied to the 'Trusted Vendors List Changes' log viewer. Only those entries selected based on your set filter criteria will be displayed in the log viewer.



