Real-time Scanner Settings
The real-time scanner (aka 'On-Access Scan') is always ON and checks files in real time when they are created, opened or copied (as soon as you interact with a file, Comodo Antivirus checks it). This instant detection of viruses assures you, the user, that your system is perpetually monitored for malware and enjoys the highest level of protection.
The real-time scanner also scans system memory on start. If you launch a program or file which creates destructive anomalies, then the scanner blocks it and alerts you immediately. Should you wish, however, you can specify that CCS does not show you alerts if viruses are found but automatically deals with them (choice of auto-quarantine or auto-block/delete). It is highly recommended that leave the Real Time Scanner enabled to ensure your system remains continually free of infection.
To open the Real Time Scan settings panel
-
Click 'Tasks > Advanced Tasks > Open Advanced Settings > Security Settings > Antivirus > 'Realtime Scan'
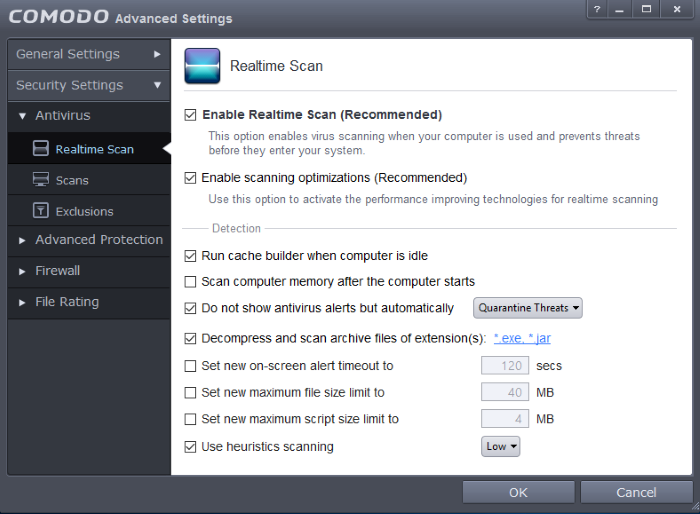
- Enable Realtime Scan – Allows you to enable or disable real-time scanning. Comodo recommends to leave this option selected. (Default=Enabled)
- Enable scanning optimizations – On selecting this option, the antivirus will employ various optimization techniques like running the scan in the background in order to reduce consumption of system resources and speed-up the scanning process (Default = Enabled)
Detection Settings
-
Run cache builder when computer is idle - CCS runs the Antivirus Cache Builder when the computer is idle, to boost the real-time scanning. If you do not want the Cache Builder to run, deselect this option (Default = Enabled).
-
Scan computer memory after the computer starts - When this check box is selected, the Antivirus scans the system memory during system start-up (Default = Disabled).
-
Do not show antivirus alerts but automatically - Allows you to configure whether or not to show antivirus alerts when malware is encountered. Choosing 'Do not show antivirus alerts but automatically' will minimize disturbances but at some loss of user awareness. If you choose not to show alerts then you have a choice of default responses that CCS should automatically take - either 'Block Threats' or 'Quarantine Threats'. (Default = Enabled)
- Quarantine Threats – Moves the detected threat(s) to quarantine for your later assessment and action. (Default)
- Block Threats – Stops the application or file from execution, if a threat is detected in it.
|
Note: If you deselect this option and thus enable alerts then your choice of quarantine/block is presented within the alert itself. |
- Decompress and scan archive files of extension(s) - Comodo Antivirus can scan all types of archive files such as .jar, RAR, WinRAR, ZIP, WinZIP ARJ, WinARJ and CAB if this option is left selected. You will be alerted to the presence of viruses in compressed files before you even open them. (Default = Enabled)
You can add the archive file types that should be decompressed and scanned by Comodo Antivirus.
Click link on the file type displayed at the right end. The 'Manage Extensions' dialog will open.
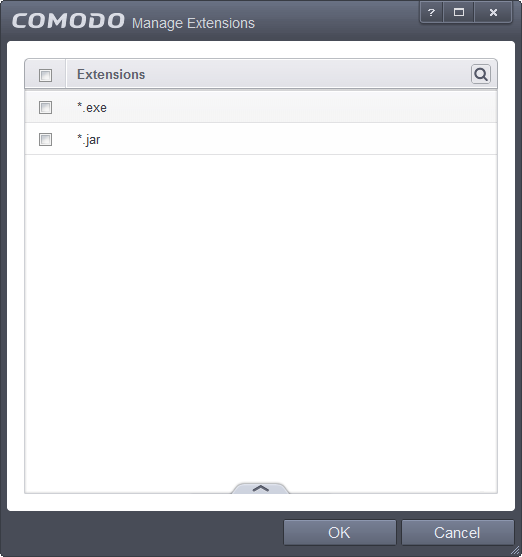
- To add a file type, click the handle at the bottom center and click 'Add'.
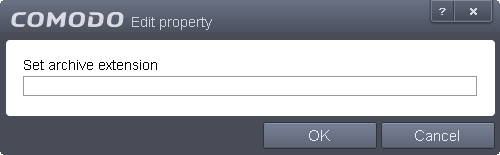
- Enter the extension (e.x.: rar, msi, zip, 7z, cab and so on) to be included in the Edit property dialog and click 'OK'
- Repeat the process to add more extensions
- Click 'OK' in the 'Manage Extensions' dialog
- Set new on-screen alert timeout to - This box allows you to set the time period (in seconds) for which the alert message should stay on the screen. (Default = 120 seconds)
-
Set new maximum file size limit to - This box allows you to set a maximum size (in MB) for the individual files to be scanned during on-access scanning. Files larger than the size specified here, will not be not scanned. (Default = 40 MB)
-
Set new maximum script size limit to - This box allows you to set a maximum size (in MB) for the script files to be scanned during on-access scanning. Files larger than the size specified here, are not scanned. (Default = 4 MB)
-
Use heuristics scanning - Allows you to enable or disable Heuristics scanning and define scanning level. (Default = Low)
Heuristic techniques identify previously unknown viruses and Trojans. 'Heuristics' describes the method of analyzing the code of a file to ascertain whether it contains code typical of a virus. If it is found to do so then the application deletes the file or recommends it for quarantine. Heuristics is about detecting virus-like behavior or attributes rather than looking for a precise virus signature that match a signature on the virus blacklist.
This is a quantum leap in the battle against malicious scripts and programs as it allows the engine to 'predict' the existence of new viruses - even if it is not contained in the current virus database.
Leave this option selected to keep Heuristics scanning enabled. Else, deselect this checkbox. If enabled, you can select the level of Heuristic scanning from the drop-down:
- Low - 'Lowest' sensitivity to detecting unknown threats but will also generate the fewest false positives. This setting combines an extremely high level of security and protection with a low rate of false positives. Comodo recommends this setting for most users. (Default)
- Medium - Detects unknown threats with greater sensitivity than the 'Low' setting but with a corresponding rise in the possibility of false positives.
- High- Highest sensitivity to detecting unknown threats but this also raises the possibility of more false positives too.



