Port Sets
Port Sets are handy, predefined groupings of one or more ports that can be re-used and deployed across multiple Application Rules and Global Rules.
- The 'Port Sets' panel allows you to view and manage pre-defined port sets and to add new port sets
- The panel can be accessed by clicking Security Settings > Firewall > Portsets from the 'Advanced Tasks' interface
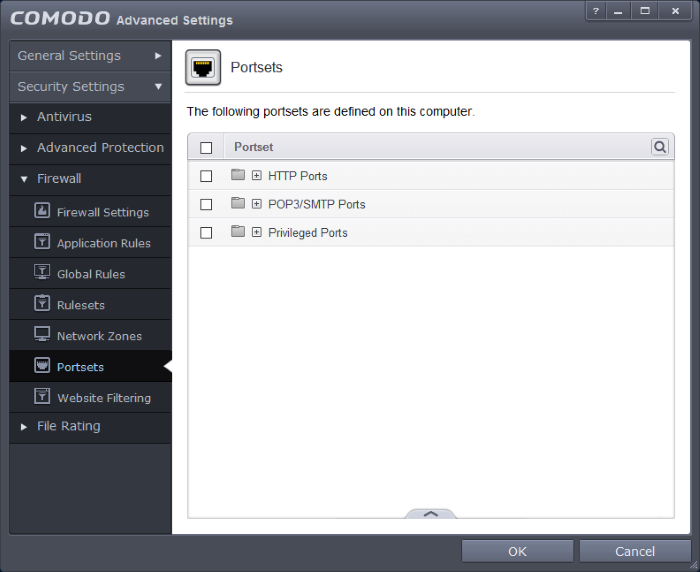
Port Sets are displayed in a tree structure. Click the + button beside a port set name to view ports contained in the set. The default port sets shipped with Comodo Client Security are:
- HTTP Ports: 80, 443 and 8080. These are the default ports for http traffic. Your internet browser uses these ports to connect to the internet and other networks.
- POP3/SMTP Ports: 110, 25, 143, 993, 995, 465 and 587. These are the ports that are typically used by mail clients like Outlook Express and WinMail for communication using the POP3, SMTP and IMAP protocols.
- Privileged Ports: 0-1023. This set can be deployed if you wish to create a rule that allows or blocks access to the privileged port range of 0-1023. Privileged ports are so called because it is usually desirable to prevent users from running services on these ports. Network admins usually reserve or prohibit the use of these ports.
You
can use the search option to find a specific port set in the list by
clicking the search icon  at the far right in the column header.
at the far right in the column header.
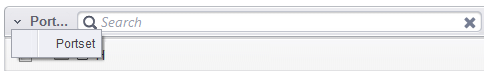
- Enter the name of the port set to be searched in full or part in the search field.
- Click the right or left arrow at the far right of the column header to begin the search.
- Click the
 icon in the search field to close the search option.
icon in the search field to close the search option.
Defining a new Port Set
You can create new portsets and allow applications to access them through the Application Rule interface. Refer to 'Creating or Modifying Firewall Rulesets' for more details.
-
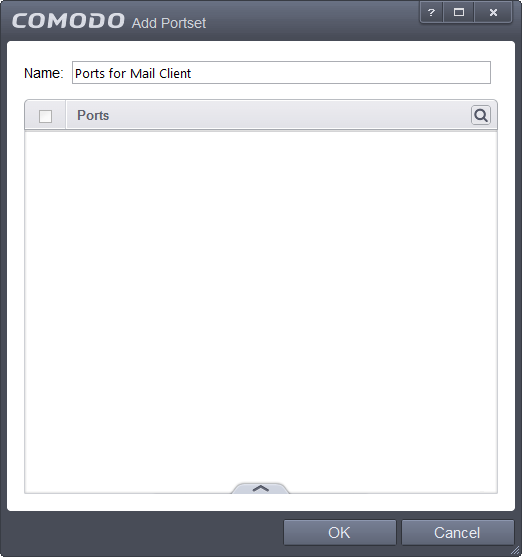
Click the handle at the bottom of the Portsets interface and select 'Add' from the options. The 'Add Portset' dialog will open.
-
Enter a name for the new portset in the Name field.
-
3. To add ports to the new portset, click the handle at the bottom and choose Add from the 'Add Portset' dialog.
-
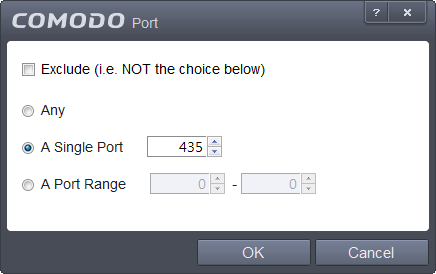
Specify the ports to be included in the new portset:
- Any - to choose all ports
- A single port - Define the port number in the combo box beside
- A port range - Enter the start and end port numbers in the respective combo boxes
- Exclude (i.e. NOT the choice below): The opposite of what you specify is applicable.
-
Click 'OK' in the 'Port' dialog. The ports will be added to the new portset in the 'Add Portset' interface.
-
Click 'OK' in the 'Add Portsets' interface to create the new portset.
Once created, a Portset can be:
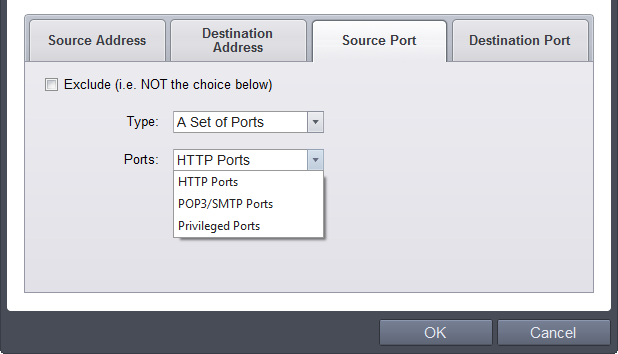
- Quickly called as 'A Set of Ports' when creating or modifying a Firewall Ruleset
To edit an existing port set
- Select the portset from the 'Portsets' interface, click the handle from the bottom center and select 'Edit' to bring up the 'Edit Portset' dialog.
- The editing procedure is similar to adding the portset explained above.



