Introduction to Comodo Client Security
Overview
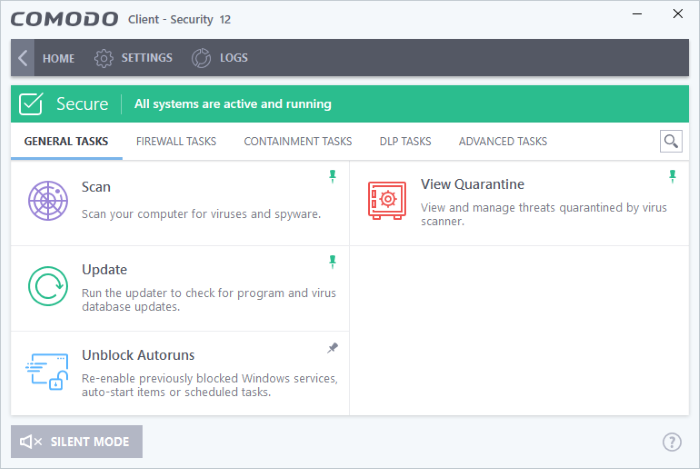
Comodo Client Security (CCS) offers complete protection against internal and external threats by combining a powerful antivirus, an enterprise class packet filtering firewall and an advanced host intrusion prevention system (HIPS).
When used individually, each of these modules delivers superior protection against their specific threat challenge. When used together they provide a complete 'prevention, detection and cure' security system for your computer. Once installed on a Windows endpoint, CCS can be remotely configured and monitored from the Endpoint Manager console.
The software is designed to be secure 'out of the box' - so even the most inexperienced users need not have to deal with complex configuration issues after installation.
Comodo Client Security - Key Features:
- Antivirus - Proactive antivirus engine that automatically detects and eliminates viruses, worms and other malware. Apart from the always-on virus monitor and scheduled scans, you can instantly check any file by right-clicking on it. The antivirus also scans any removable storage plugged-in to your computer.
- Firewall
- Highly configurable packet
filtering firewall that constantly defends your system from
inbound and outbound Internet attacks.
- Host Intrusion Protection (HIPS) - A rules-based intrusion prevention system that monitors the activities of all applications and processes on your computer. HIPS blocks the activities of malicious programs by halting any action that could cause damage to your operating system, system-memory, registry keys or personal data.
- Containment - Authenticates every executable and process running on your computer and prevents them from taking actions that could harm your computer. Unrecognized processes and applications will be auto-contained and run under a set of restrictions so they cannot harm your computer. This gives untrusted (but harmless) applications the freedom to operate whilst untrusted (and potentially malicious) applications are prevented from damaging your PC or data.
- Containment - Authenticates every executable and process running on your computer and prevents them from taking potentially damaging actions. Unrecognized processes and applications will be automatically run inside a security hardened environment known as a container. Once inside, they will be strictly monitored, will not be able to access other processes and will write to a virtual file system and registry. This gives untrusted (but harmless) applications the freedom to operate while untrusted (and potentially malicious) applications are prevented from damaging your PC or data.
- Virtual Desktop - A sandbox environment in which you can run programs and browse the internet without fear those activities will damage the host computer. Applications in the virtual desktop are isolated from the host operating system, write to a virtual file system, and cannot access user data.
- Data Loss Prevention (DLP) - A scanner which lets you identify documents on your computer which contain sensitive data, including credit card numbers and social security numbers. You can move detected documents to another location, quarantine them, ban them from being copied to USB devices, and more.
- Advanced Protection - A collection of prevention based security technologies designed to preserve the integrity, security and privacy of your operating system and user data.
- VirusScope - Monitors the activities of processes running on your computer and alerts you if they take actions that could potentially threaten your privacy and/or security. Using a system of behavior 'recognizers', Viruscope not only detects unauthorized actions but also allows you to completely undo them. Apart from representing another hi-tech layer of protection against malware, this also provides you with the granular power to reverse unwanted actions taken by legitimate software without blocking the software entirely.
- Rescue Disk - Built-in wizard that allows you to burn a boot-disk which will run antivirus scans in a pre-Windows / pre-boot environment.
- Additional
Utilities - The
advanced tasks section contains links that allow you to install
other, free, Comodo security products - Comodo Cleaning
Essentials and KillSwitch.
Guide Structure
This introduction is intended to
provide an overview of the basics of Comodo Client Security and
should be of interest to all users.
The remaining sections of the guide cover every aspect of the configuration of Comodo Client Security.



