Set up the Firewall For Maximum Security and Usability
This page outlines the functions of Comodo's Firewall and helps you to set up a secure connection to the internet.
Stealth Ports Settings
Port stealthing is a security feature whereby ports on an internet connected PC are hidden from sight, sending no response to opportunistic port scans.
1. Click 'Tasks' > 'Firewall Tasks' tab
2. Click 'Stealth Ports'
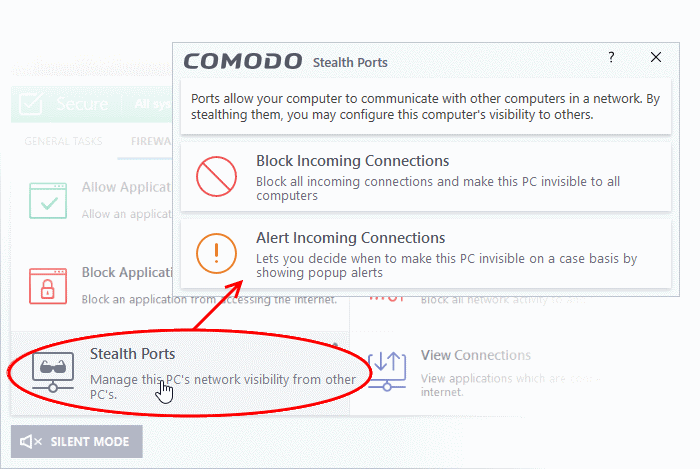
3. Select 'Block Incoming Connections' to make computer's ports are invisible to all networks
Click here for more information about port stealthing
Network Zones Settings
'Network Zones' settings allow you to configure the protection level for connection to a router/home network (this is usually done automatically for you).
View the configurations
1. Click 'Settings' at the top of the CCS home screen
2. Select 'Firewall' > 'Network Zones'
3. Click 'Network Zones' tab in the 'Network Zones' interface
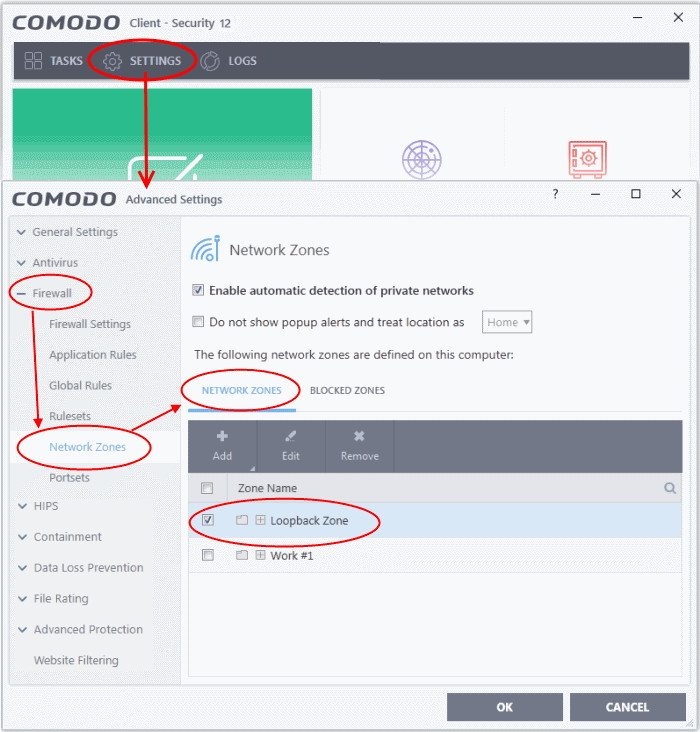
4. Inspect the 'Loopback zone' and 'Local Area Network #1' (exact name may vary) by clicking the '+' button beside the zone name
- In most cases, the loopback zone IP address should be 127.0.01/255.0.0.0
- In most cases, the IP address of the auto-detected Network zone should be 10.nnn.nnn.nnn/255.255.255.0
5. Click 'OK'.
Click here for more details on network zones settings
Firewall Settings
The firewall settings option lets you configure the protection level for your internet connection, and the frequency of alerts generated.
1. Click 'Settings' at the top of the CCS home screen
2. Click 'Firewall' > 'Firewall Settings'
2. Select 'Enable Firewall' and choose 'Safe Mode' from the drop-down
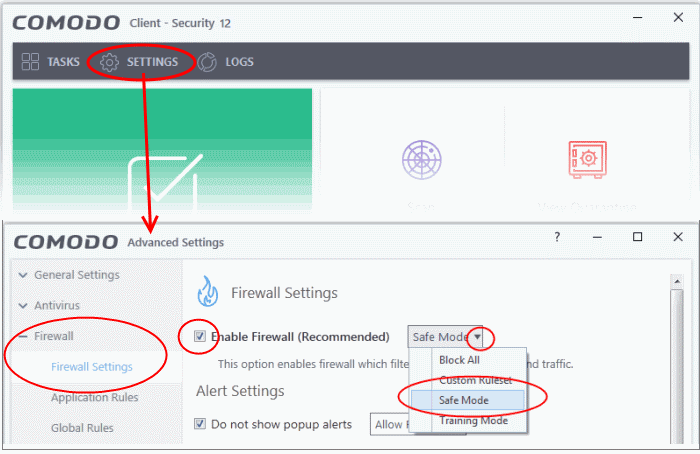
Safe Mode: While filtering network traffic, the firewall will automatically create rules which allow traffic for application components certified as 'Safe' by Comodo. For non-certified, new, applications, you will receive an alert whenever that application attempts to access the network. Should you choose, you can grant that application internet access by choosing 'Treat this application as a Trusted Application' at the alert. This will deploy the predefined firewall policy 'Trusted Application' onto the application.
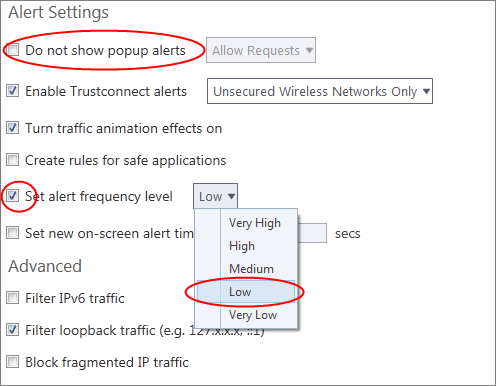
Alert Settings
Under 'Alert Settings' in the same interface:
-
Deselect 'Do not show pop-up alerts'
-
Select 'Set alert frequency level' option and choose 'Low' from the drop-down. At the 'Low' setting, the firewall shows alerts for outgoing and incoming connection requests for an application. This is the setting recommended by Comodo and is suitable for the majority of users.
Advanced Settings
When launching a denial of service or 'flood' attack, an attacker bombards a target machine with so many connection requests that your computer is unable to accept legitimate connections, effectively shutting down your web, email, FTP or VPN server. To protect from such attacks, make the following settings under 'Advanced' in the 'Firewall Settings' interface:
- Select 'Filter loopback traffic'
- Ensure that the 'Block fragmented IP traffic' is selected
- Block fragmented IP traffic - When a connection is opened between two computers, they must agree on a Maximum Transmission Unit (MTU). IP Datagram fragmentation occurs when data passes through a router with an MTU less than the MTU you are using i.e when a datagram is larger than the MTU of the network over which it must be sent, it is divided into smaller 'fragments' which are each sent separately. Fragmented IP packets can create threats similar to a DOS attack. Moreover, these fragmentations can double the amount of time it takes to send a single packet and slow down your download time.
- Select 'Do Protocol Analysis' checkbox to detect fake packets used in denial of service attacks
- Select 'Enable anti-ARP spoofing'
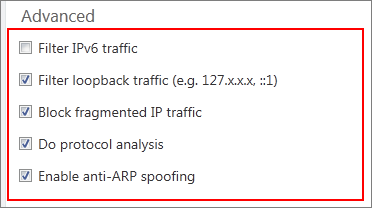
4. Click 'OK' for your settings to take effect.
Click here for more details on firewall settings
Set-up Application Rules, Global Rules and Predefined Firewall Rulesets
You can configure and deploy traffic filtering rules and policies on an application-specific and global basis.
View the 'Application Rules'
2. Click 'Firewall > 'Application Rules'
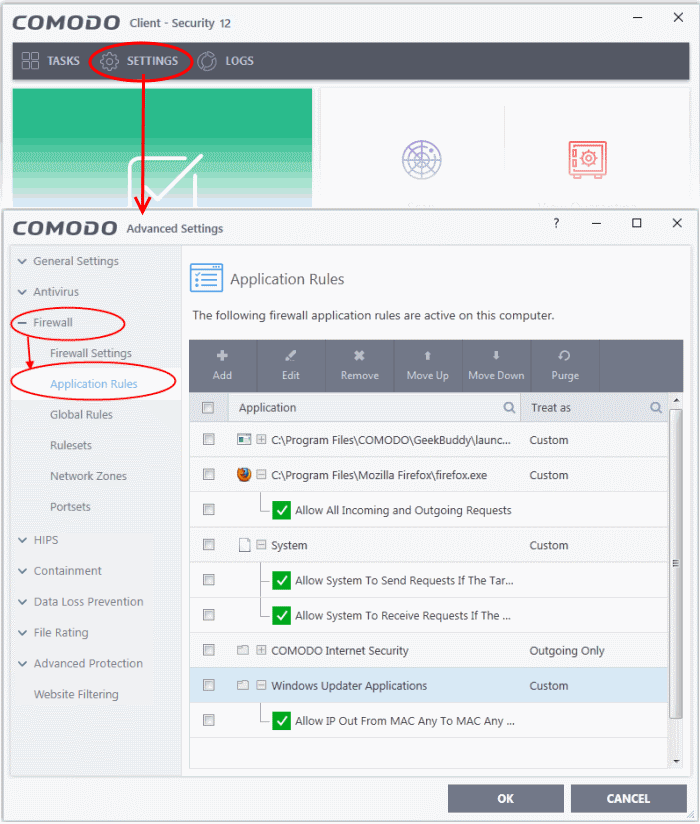
3. Click 'Add' to add a new application rule
4. Select a rule and click 'Edit' to edit the rules for a specific application manually or click 'Remove' to remove them
5. Click 'OK' for your settings to take effect
Click here for more details on application rules
View the Global Rules
2. Click 'Firewall' > 'Global Rules'
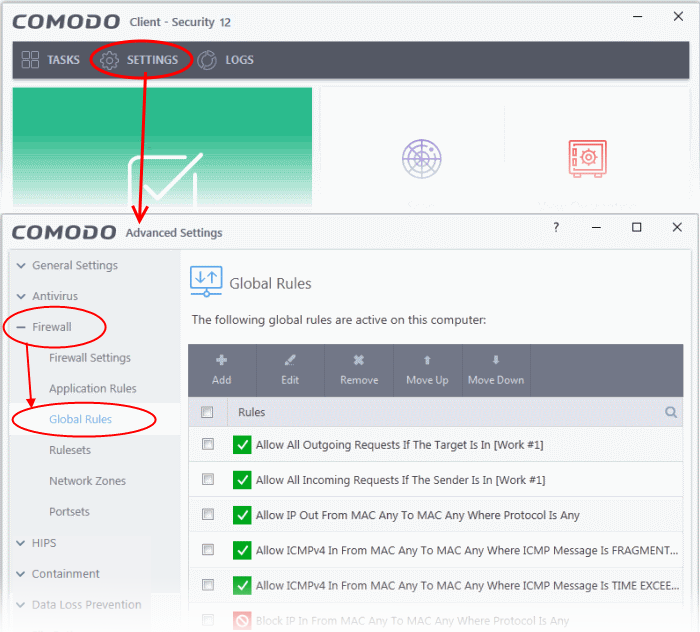
4. Select a rule and click 'Edit' to edit the a rule manually or click 'Remove' to remove them
5. Click 'OK' for your settings to take effect
Click here for more details on global rules
View Predefined Firewall rulesets
1. Click 'Settings' on the CCS home screen
2. Click 'Firewall' > 'Rulesets'
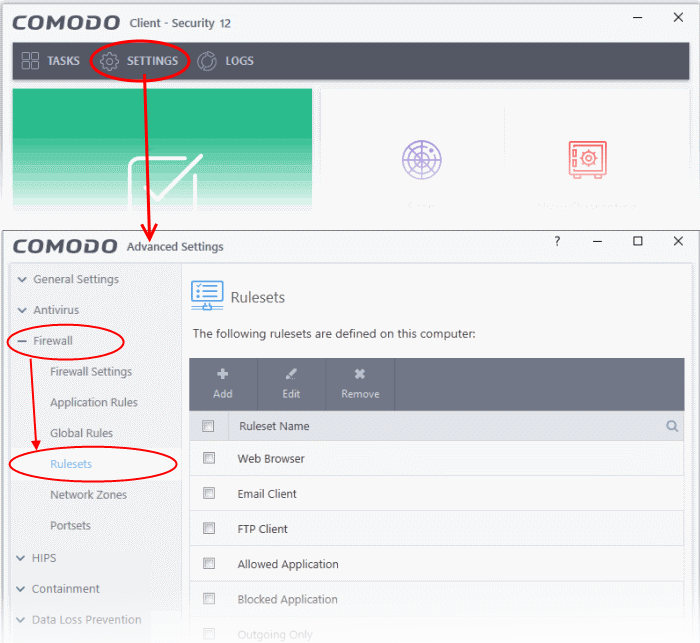
3. Click 'Add' to add a new ruleset
4. Select a ruleset and click 'Edit' to edit the rules manually or click 'Remove' to remove them
5. Click 'OK' for your settings to take effect
Note: You need not make your own rulesets, the defaults are usually enough.
Click here for more details on pre-defined firewall rulesets



