Filter Antivirus Logs
You
can create custom views of all logged events according to the
following criteria:
- Action – Filter events according to the response (action) of the antivirus
- Location – Filter events by the path at which the malware was found
- Status – Filter events according to whether the attempted action was successful or not. Status options are 'Success' or 'Fail'
- Malware Name - Display only those events that reference a specific piece of malware
Configure Event Filters
- Open Xciitum Client Security
- Click 'More' > 'View Logs' > 'Antivirus Events'
- Right-click inside the log viewer module and choose 'Advanced Filter'
There are 4 types of filter. Each of these can be further refined by selecting or deselecting specific parameters.

Action: Filter logs by the action taken by XCS on the detected threat. You can then filter by a specific type of action. For example, to only show events where the threat was quarantined.

- Select 'Equal' or 'Not Equal' from
the drop down.
- Equal – Show only events which feature the action you select. You can select multiple actions.
- Not Equal - Inverts your choice. For example, select 'Not Equal' + 'Ignore' to view every event except those that were ignored.
- Select the specific actions you want to view from:
- Quarantine: Events where the threat was placed in quarantine
- Remove: Events where the user chose to delete a threat
- Ignore: Events where the user chose to ignore an item
- Detect: Events where the malware was first detected
- Ask: Events where the user was asked to provide a response to a discovered threat. The response from the user might be 'Quarantine', 'Remove', 'Ignore' or 'Restore'. Users are asked for their response at a threat alerts, and at the scan results screen.
- Restore: Events where the user removed the threat from quarantine and restored it to its original location.
Status: Filter logs by whether or not the action taken on the threat was successful. You choose to view only successful actions, or only failed actions.
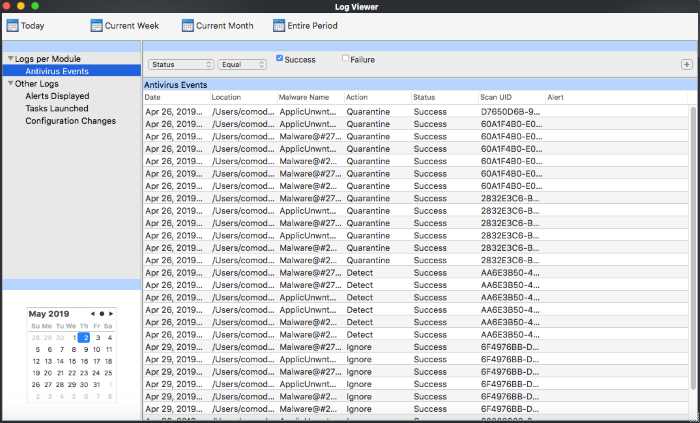
- Select 'Equal' or 'Not Equal' from the drop-down.
- Equal – Show only events which feature the result you select.
- Not Equal - Inverts your choice. For example, select 'Not Equal' + 'Success' to view every event except those that were successful.
- Select the specific results you want to view:
- Success: View events where the task in the 'Action' column was completed.
- Failure: View events where the task in the 'Action' column was not completed.
Location: View logs that concern files at a specific path. You need to enter the path in the field provided:
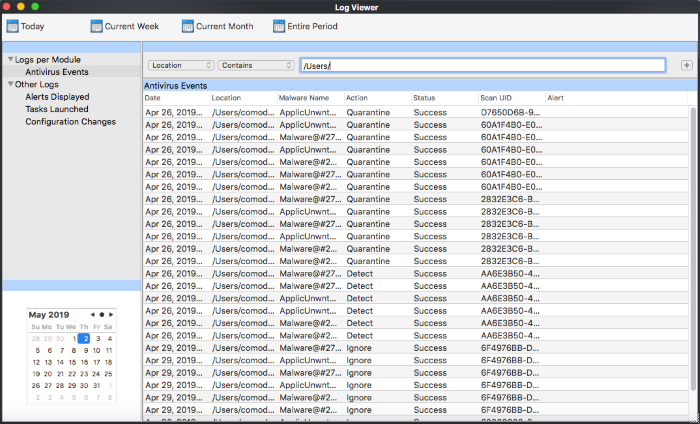
- Select 'Contains' or 'Does Not Contain' from the second drop-down:
- Contains – Show only those events which concern items at the location you specify. You can add multiple locations.
- Not Equal – Show events which did not concern files at the locations you specify.
Malware Name: Filter logs by the name of the malicious item. You need to enter the name of the malware in the field provided:
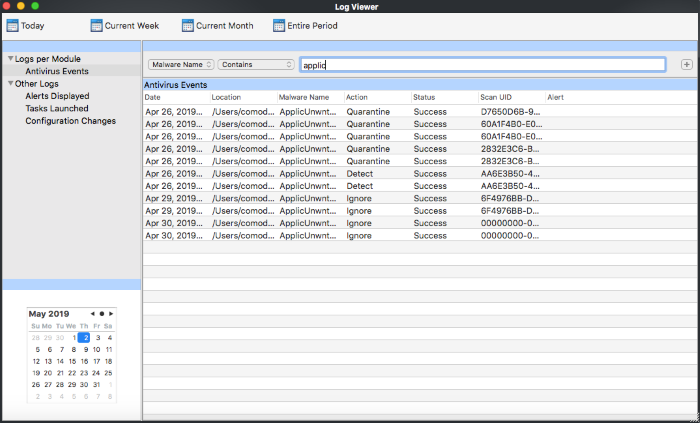
- Select 'Contains' or 'Does Not Contain' from the second drop-down:
- Contains – Show only those events which concern the malware named in the text field. You can add multiple malware names.
- Not Equal – Show only those events which did not involve the malware named in the text field.


