Filtering Firewall Logs
Comodo Internet Security allows you to create custom views of all logged events according to user defined criteria. You can use the following types of filters:
Clicking on the handle at the bottom enables you to filter the logs for a selected time period:
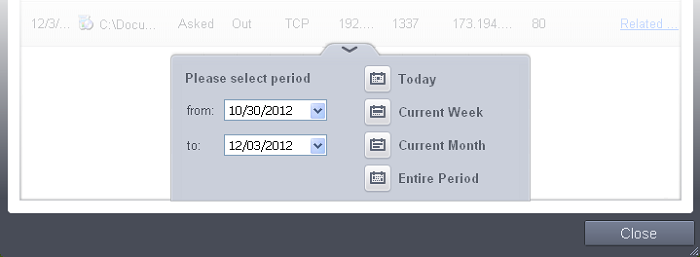
- Today - Displays all logged events for today.
- Current Week - Displays all logged events during the current week. (The current week is calculated from the Sunday to Saturday that holds the current date.)
- Current Month - Displays all logged events during the month that holds the current date.
- Entire Period - Displays every event logged since Comodo Internet Security was installed. (If you have cleared the log history since installation, this option shows all logs created since that clearance).
- Custom Filter – Enables you to select a custom period by
choosing the 'From' and 'To' dates under 'Please Select Period'
Having chosen a preset time filter you can further refine the displayed events according to specific filters. Following are available filters for Firewall logs and their meanings:
- Action - Displays events according to the response (or action taken) by the firewall
- Application - Displays only the events propagated by a specific application
- Destination IP - Displays only the events with a specific target IP address
- Destination Port - Displays only the events with a specific target port number
- Direction - Displays only the events of Inbound or Outbound nature
- Protocol - Displays only the events that involved a specific protocol
- Source IP address - Displays only the events that originated from a specific IP address
- Source Port - Displays only the events that originated from a specific port number
To configure Advanced Filters for Firewall events
-
Click the funnel button
 from
the title bar. The Advanced Filter interface for Firewall events
will open.
from
the title bar. The Advanced Filter interface for Firewall events
will open. -
Select the filter from the 'Advanced Filter' drop-down and click 'Add' to apply the filter.
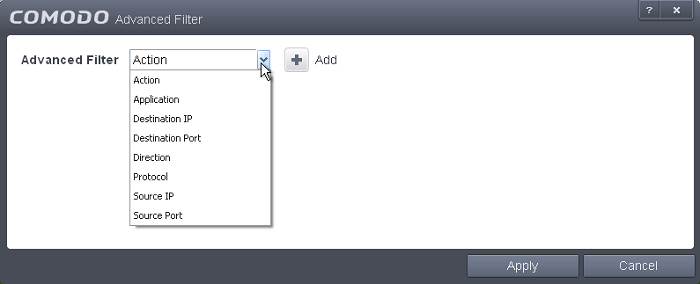
You have 8 categories of filters that you can add. Each of these categories can be further refined by either selecting or deselecting specific filter parameters or by the user typing a filter string in the field provided. You can add and configure any number of filters in the 'Advanced Filter' dialog.
Following are the options available in the 'Advanced Filter' drop-down:
-
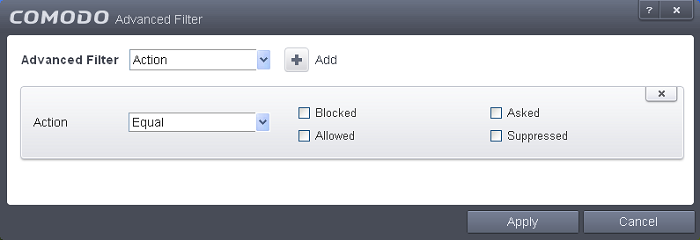
Action: Selecting the 'Action' option displays a drop-down box and a set of specific filter parameters that can be selected or deselected.
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Now select the checkboxes of the specific filter parameters to refine your search. The parameter available are:
- Blocked: Displays list of events that were blocked
- Allowed: Displays list of events that were allowed
- Asked: Displays list of events that were asked to the user
- Suppressed: Displays list of events that were suppressed by the user
-
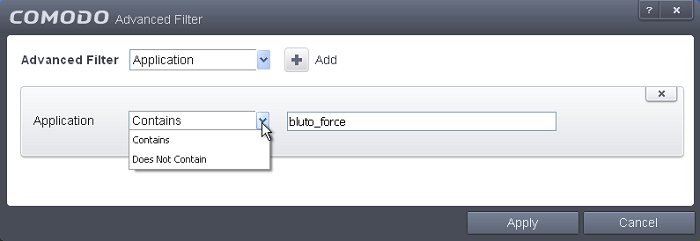
Application: Selecting the 'Application' option displays a drop-down box and text entry field.
-
Select 'Contains' or 'Does Not Contain' option from the drop-down box.
-
Enter the text or word that needs to be filtered.
For example, if you select 'Contains' option from the drop-down field and enter the phrase 'bluto-force' in the text field, then all events containing the entry 'bluto-force' in the 'Application' column will be displayed. If you select 'Does Not Contain' option from the drop-down field and enter the phrase 'bluto-force' in the text field, then all events that do not have the entry 'bluto-force' in the 'Application' column will be displayed.
-
Destination IP: Selecting the 'Destination IP' option displays two drop-down boxes and a text entry field.
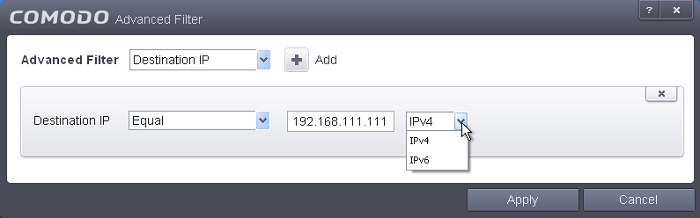
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Select 'IPv4' or 'IPv6' from the drop-down box.
-
Enter the destination system's IP address that needs to be filtered.
For example, if you select 'Contains' option from the drop-down field, select IPv4 and enter 192.168.111.111 in the text fields, then all events containing the entry '192.168.111.111' in the 'Destination IP' column will be displayed.
-
Destination Port: Selecting the 'Destination Port' option displays a drop-down box and text entry field.
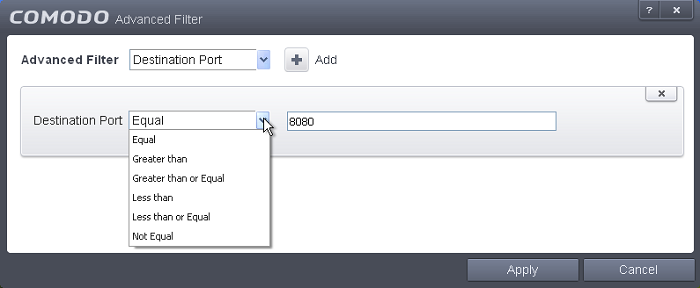
-
Select any one of the following option the drop-down box.
- Equal
- Greater than
- Greater than or Equal
- Less than
- Less than or Equal
- Not Equal
-
Now enter the destination port number in the text entry field.
For example, if you select 'Equal' option from the drop-down field and enter 8080 in the text field, then all events containing the entry '8080' in the 'Destination Port' column will be displayed.
-
Direction: Selecting the 'Direction' option displays a drop-down box and a set of specific filter parameters that can be selected or deselected.
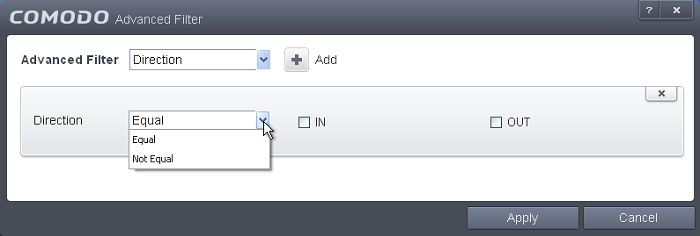
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Now select the check box of the specific filter parameters to refine your search. The parameter available are:
- In: Displays a list of events that were directed into the system
- Out: Displays a list of events that were directed out of the system
-
Protocol: Selecting the 'Protocol option displays a drop-down box and a set of specific filter parameters that can be selected or deselected.
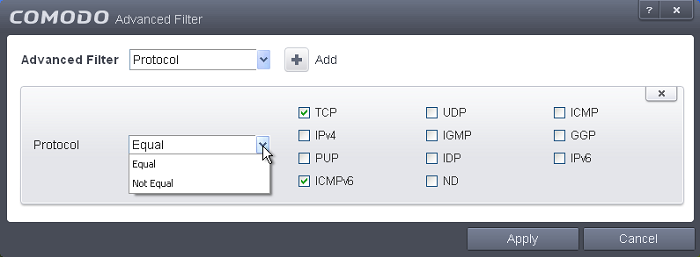
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Now select the checkboxes of the specific filter parameters to refine your search. The parameter available are:
- TCP
- UDP
- ICMP
- IPV4
- IGMP
- GGP
- PUP
- IDP
- IPV6
- ICMPV6
- ND
-
Source IP: Selecting the 'Source IP' option displays two drop-down boxes and a set specific filter parameters that can be selected or deselected.
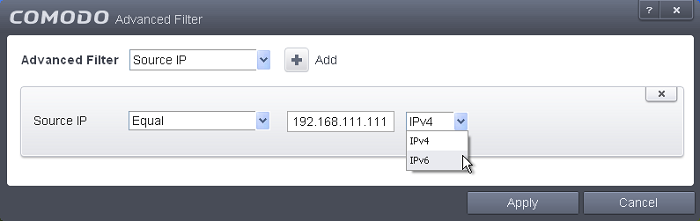
-
Select 'Equal' or 'Not Equal' option from the drop-down box. 'Not Equal' will invert your selected choice.
-
Select 'IPv4' or 'IPv6' from the drop-down box.
-
Enter the source system's IP address that needs to be filtered.
-
Source Port: Selecting the 'Status' option displays a drop-down box and a set specific filter parameters that can be selected or deselected.
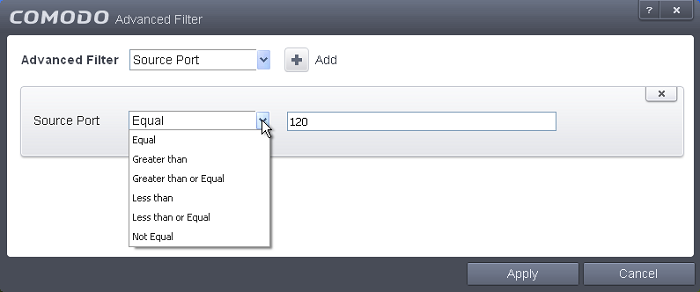
-
Select any one of the following option the drop-down box.
- Equal
- Greater than
- Greater than or Equal
- Less than
- Less than or Equal
- Not Equal
-
Now enter the source port number in the text entry field.
| Note: More than one filter can be added in the 'Advanced Filter' pane. After adding one filter type, select the next filter type and click 'Add'. You can also remove a filter type by clicking the 'X' button at the top right of the filter pane. |
- Click 'Apply' for the filters to be applied to the Firewall log viewer. Only those entries selected based on your set filter criteria will be displayed in the log viewer.



