Global Rules
Unlike Application rules, which are applied to and triggered by traffic relating to a specific application, Global Rules are applied to all traffic traveling in and out of your computer.
Comodo Firewall analyzes every packet of data in and out of your PC using combination of Application and Global Rules.
- For Outgoing connection attempts, the application rules are consulted first and then the global rules second.
- For Incoming connection attempts, the global rules are consulted first and then the application rules second.
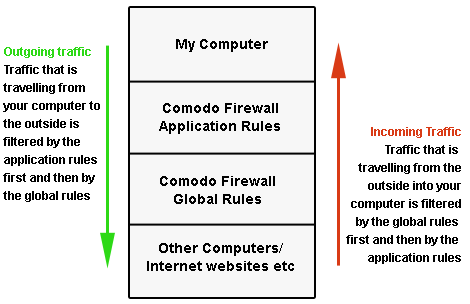
Therefore, outgoing traffic has to 'pass' both the application rule then any global rules before it is allowed out of your system. Similarly, incoming traffic has to 'pass' any global rules first then application specific rules that may apply to the packet.
Global Rules are mainly, but not exclusively, used to filter incoming traffic for protocols other than TCP or UDP.
-
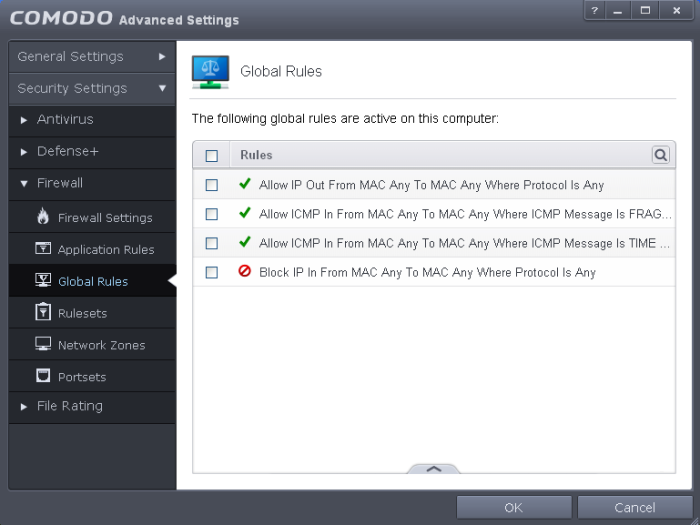
The Global Rules panel, accessible by clicking Security Settings > Firewall > Global rules tab from the Advanced tasks interface, allows you to view, add and manage the rules
You can use the search option to find a specific rule in the list.
To use the
search option, click the search icon at the far right in the column
header.
at the far right in the column
header.
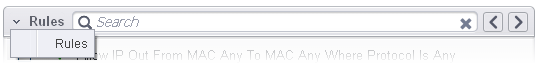
- Click the chevron on the left side of the column header and select the search criteria from the drop-down.
- Enter partly or fully the name of the item as per the selected criteria in the search field.
- Click the right or left arrow at the far right of the column header to begin the search.
- Click
the
 icon in the search field to close the search option.
icon in the search field to close the search option.
General Navigation:
Clicking the handle at the bottom center of the interface opens an option panel with the following options:
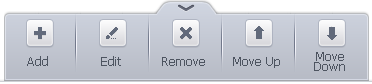
- Add - Allows you to add a new global rule. See the section 'Adding and Editing a Firewall Rule' for guidance on creating a new rule.
- Edit - Allows you to modify the selected global rule. See the section 'Adding and Editing a Firewall Rule' for guidance on editing a new rule.
- Remove - Deletes the selected rule.
- Purge - Runs a system check to verify that all the applications for which rules are listed are actually installed on the host machine at the path specified. If not, the rule is removed, or 'purged', from the list.
The configuration of Global Rules is identical to that for application rules. To add a global rule, click the 'Add...' button on the right. To edit an existing global rule, right click and select 'edit'.
- See Application Rules for an introduction to the rule setting interface.
- See Understanding Firewall Rules for an overview of the meaning, construction and importance of individual rules.
- See Adding and Editing a Firewall Rule for an explanation of individual rule configuration.



