Miscellaneous Settings
Click 'Settings' > 'Advanced Protection' > 'Miscellaneous'
- The 'Miscellaneous' panel allows you to:
- Configure protection against shellcode injections (buffer overflow attacks)
- Show alerts if applications try to change your browser settings
- Skip automatic cleanup of suspicious certificates
- Specify what actions are taken if CIS detects unrecognized auto-start entries or scheduled tasks
Open the miscellaneous interface
- Click 'Settings' on the home screen to open the 'Advanced Settings' interface
- Click 'Advanced Protection' > 'Miscellaneous':
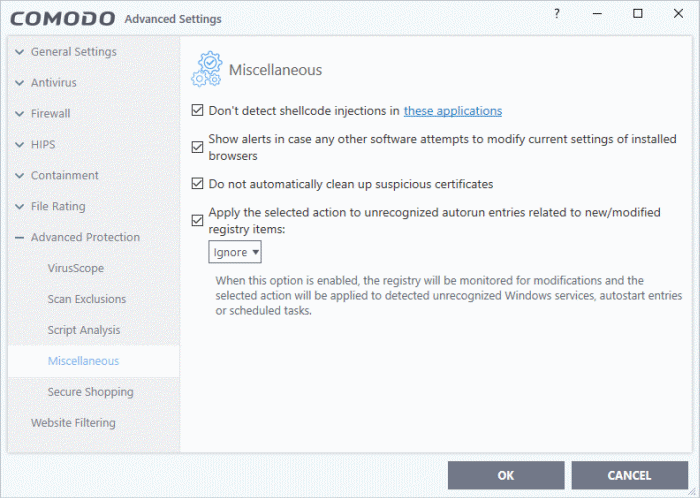
This interface allows you to:
Disable shellcode injection detection
By default, shellcode injection protection is enabled for all applications on your computer. Use this setting to define applications which you do not want to be monitored for shellcode injections.
|
Background:
|
- Make sure 'Don't detect shellcode injections in these applications' is enabled and click the 'these applications' link. The 'Manage Exclusions' dialog appears.
- Click the 'Add' button at the top
You can add items by selecting the required option from the drop-down:
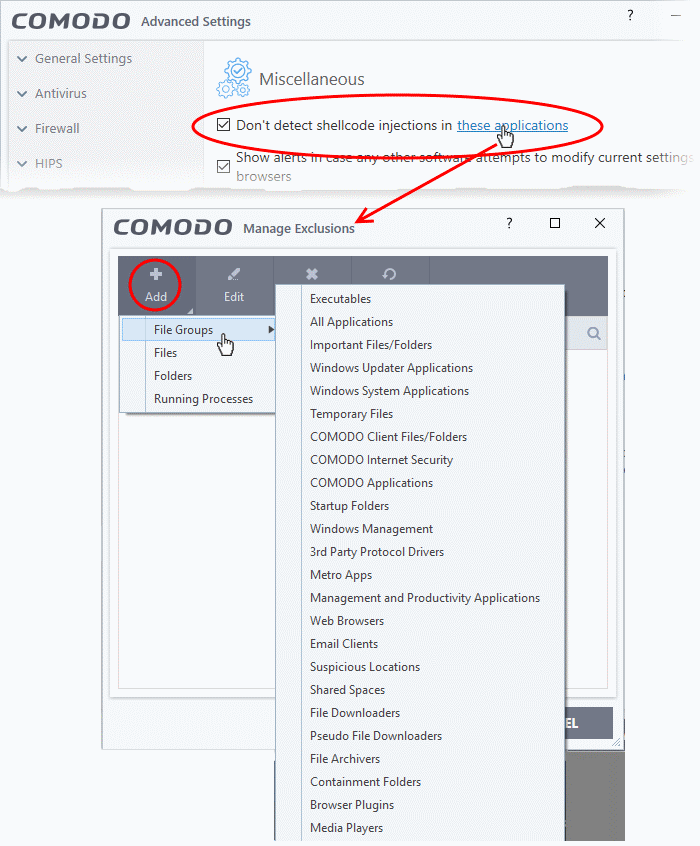
- File Groups - Select a category of pre-set files or folders. For example, 'Executables' lets you create a ruleset for all files with the extensions .exe .dll .sys .ocx .bat .pif .scr .cpl, *cmd.exe *.bat, *.cmd. Other categories available include 'Windows System Applications', 'Windows Updater Applications', 'Start Up Folders' etc. See File Groups for more details on file groups.
- Running Processes - As the name suggests, this option allows you to select an application or executable from the processes that are currently running on your PC.
- Folders - Opens the 'Browse for Folders' window and enables you to navigate to the folder you wish to add.
- Files - Opens the 'Open' window and enables you to navigate to the application or file you wish to add.
Click 'OK' to implement your settings.
Enable alerts if software tries to change your browser settings
- Show alerts in case any other software attempts to modify current settings of installed browsers - Improves online security by warning you each time a program tries to change your browser's settings without your consent. The browser settings include home page, default search engine and more. (Default = Enabled).
Do not automatically cleanup suspicious certificates
- Choose whether or not to delete any root certificates that were not signed by a trusted certificate authority.
- By default, CIS warns you if any fake root certificates are found in your browsers but does not delete them.
- Disable this option if you want CIS to delete those fake certificates whenever they are found
|
Background:
|
Define actions to be taken on unrecognized auto-start entries/scheduled tasks
- Apply the selected action to unrecognized autorun entries related to new / modified registry items - Specify what CIS should do if applications added to Script Analysis > Autoruns Scans try to create or modify one of the following registry items:
- Windows services
- Auto-start entries
- Scheduled tasks
The available options are:
- Ignore - CIS does not take any action (Default)
- Terminate - CIS stops the process / service
- Terminate and Disable - Auto-run processes are stopped and the corresponding auto-run entry removed. In the case of a service, CIS disables the service.
- Quarantine and Disable - Auto-start processes are quarantined and the corresponding auto-start entry removed. In the case of a service, CIS disables the service.
|
Background:
|
- Click
'OK' to save your settings.



