TrustConnect Overview
- Comodo TrustConnect is a secure Internet proxy service that creates an encrypted session when users are accessing the Internet over public wireless connections.
- Since these wireless sessions can be relatively easily intercepted, they present a significant data vulnerability gap for businesses and consumers alike.
- Whenever Comodo Internet Security detects unsecured wireless connections it will present you with the opportunity to use your TrustConnect account for the connection.
- TrustConnect is designed to eliminate these types of data hijacks by preventing criminals from attacking or scanning your system from the local network that you are using to connect to the Internet.
- It also encrypts all of your traffic destined for the Internet (including Web site addresses, instant messaging conversations, personal information, plain text usernames and passwords and other important information).
- After connecting to the service, the TrustConnect software indicates that traffic is being encrypted as it leaves your system.
- Data thieves and hackers cannot 'sniff' or intercept your data
- They can't determine where your information is coming from because, as you are connecting to the Internet through a SSL secured VPN connection to the TrustConnect servers, your requests appear to come from our IP address. Ordinarily, cyber criminals could easily intercept these broadcasts.
- Setting up Comodo TrustConnect is easy, as it works on most operating systems (Windows, Mac OS X) as well as with most firewall applications.
- Typical setup takes less than three minutes. TrustConnect clients are available for Windows, Mac OS, Linux and iPhone mobile devices and can be downloaded by logging into your account at https://accounts.comodo.com/account/login.
- Your Comodo Internet Security Complete confirmation email contains confirmation of your the username that you set up during initial sign up and a subscription ID for the service.
- Once logged in, click the TrustConnect tab to add subscriptions, change billing and contact information, and review the ongoing status of your service.
- Your Comodo Internet Security Complete TrustConnect account has a 10 GB/month data transfer limit.
- Comodo Internet Security - Complete customers also receive the $99 value 'Live, Expert Computer Support' Comodo GeekBuddy. Please visit http://www.geekbuddy.com/ for full product details.
- TrustConnect System Requirements
- Windows 10
- Windows 8
- Windows 7
- Windows Vista
- Windows XP
- Vac OS X
- Linux (containing kernel 2.4 or later)
- FreeBSD, OpenBSD
For users of Comodo Internet Security, TrustConnect is integrated with the application and need not install the TC client in their systems.
Comodo Internet Security Complete Users
CIS Complete product includes TrustConnect services and the application is installed automatically along with CIS. When a new wireless connection is established by your system, a Network Detected dialog is displayed.
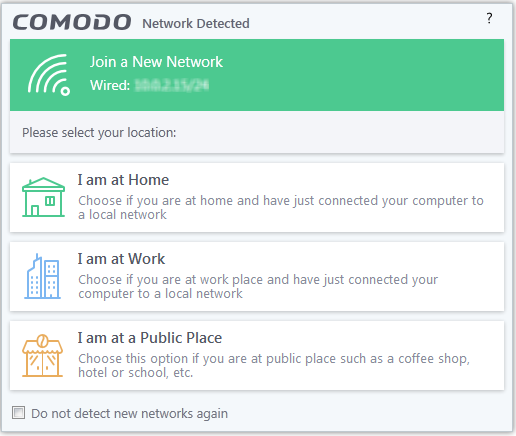
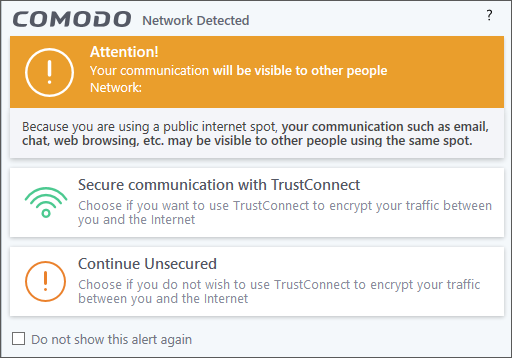
Select your location from the dialog. A TrustConnect alert is displayed depending on the settings configured in Firewall Settings interface.
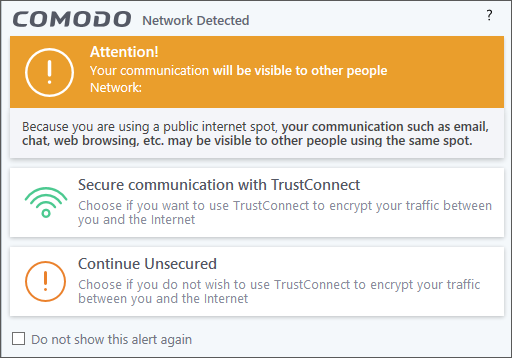
Select whether you want to connect to the Internet via TrustConnect thus encrypting the traffic between your system and the Internet or use the unsecured network.
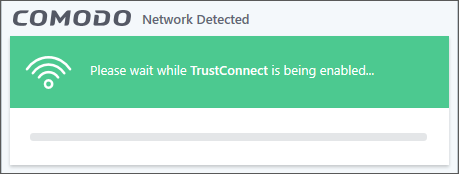
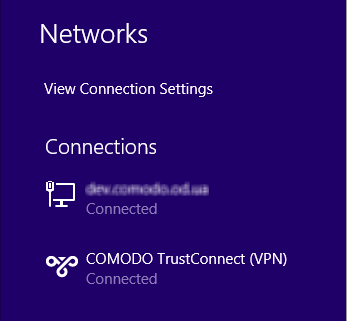
If you choose 'Secure communication with TrustConnect', CIS will establish the connection via TC.
..and
on successful connection, you can view the details in the system
tray.
Choose 'Continue Unsecured' option if you do not want to establish an encrypted connection.
Comodo Internet Security Pro / Premium Users
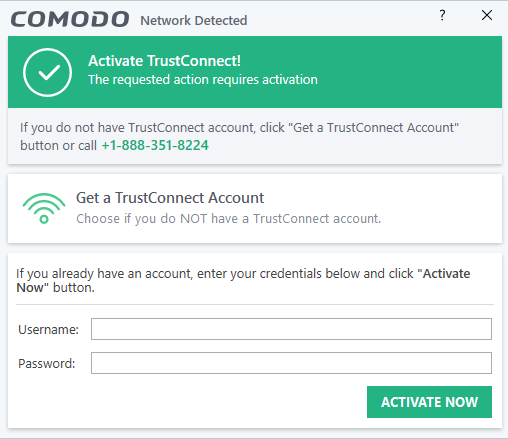
- You can purchase the TC service by clicking the 'Get a TrustConnect Account', enter the TC service credentials and activate the service.
- If you already have a TC account, enter the TC service credentials in the Username and Password fields and click the 'Activate Now' button.
Find your TC service credentials
- In the https://accounts.comodo.com/ page, login to your CAM account using the CAM username and password sent via email at the time of account creation.
- Click 'TrustConnect' in the menu bar or in the drop down from 'Services' tab.
The account details of your TC service is displayed.
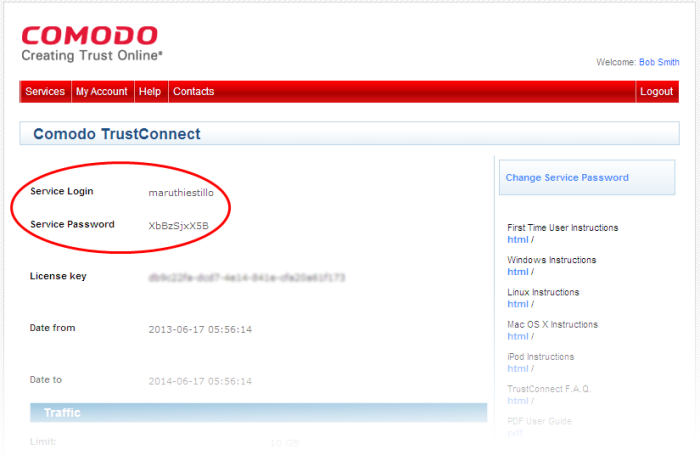
The TC service login and password for your account should be entered in the Username and Password fields respectively in the 'Activate TrustConnect' dialog.
Please note that this activation dialog will appear only for the first time you are trying to connect via TC. After the activation process is successfully completed, subsequent attempts to connect via TC to the internet is automatically established.



