Understand Security Alerts
Alerts Overview
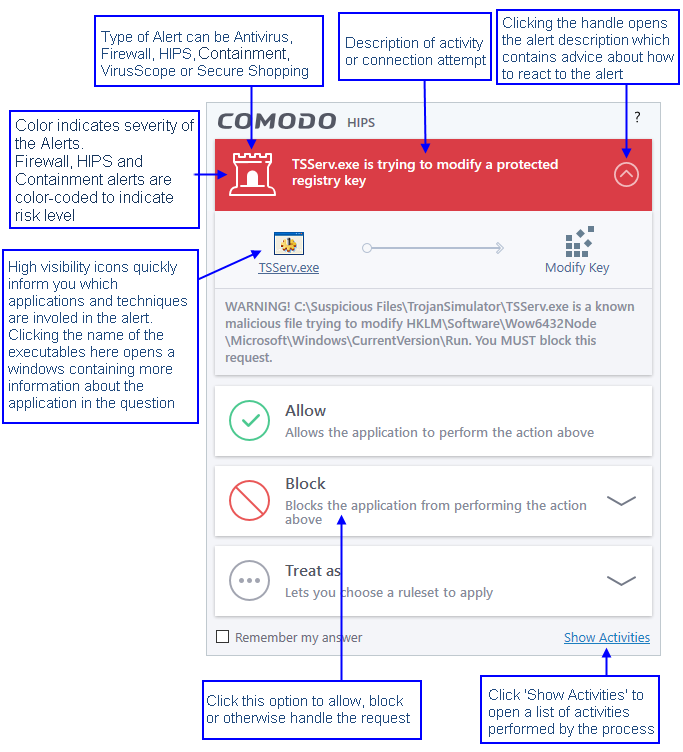
CIS alerts warn you about security related activities at the moment they occur. Each alert contains information about a particular issue so you can make an informed decision about whether to allow or block it. Alerts also let you specify how CIS should behave in future when it encounters activities of the same type. Some alerts also allow you to reverse the changes made to your computer by the applications that raised the security related event.
Comodo Internet Security alerts come in six main varieties. Click the name of the alert (at the start of the following bullets) if you want more help with a particular alert type.
- Antivirus Alerts - Shown whenever virus or virus-like activity is detected. AV alerts will be displayed only when Antivirus is enabled and the option 'Do not show antivirus alerts' is disabled in Real-time Scanner Settings.
-
Auto-Scan Alerts - Shown whenever an external storage device like a USB stick or an external hard disk drive is connected to your computer. Auto-scan alerts are shown only if 'Do not show auto-scan alerts' is disabled in Real-time Scanner Settings.
- Firewall Alerts - Shown whenever a process attempts unauthorized network activity. Firewall alerts will be displayed only when the Firewall is enabled and the option 'Do not show popup alerts' is disabled in Firewall Settings.
- HIPS Alerts - Shown whenever an application attempts an unauthorized action or tries to access protected areas. HIPS alerts will only be generated if HIPS is enabled and Do not show popup alerts is disabled.
- Containment Alerts (including Elevated Privilege Alerts) - Shown whenever an application tries to modify operating system or related files and when CIS automatically contains an unrecognized file. Containment alerts will be shown only if privilege elevation alerts are enabled in Containment Settings.
- VirusScope Alerts - Shown whenever a currently running process attempts to take suspicious actions. VirusScope alerts allow you to quarantine the process & reverse its changes or to let the process go ahead. Be especially wary if a VirusScope alert pops up 'out-of-the-blue' when you have not made any recent changes to your computer. VirusScope Alerts will be displayed only when VirusScope is enabled under Advanced Settings.
- Secure Shopping Alerts - Shown whenever a user opens a website that is configured to invoke an alert in the rules. Secure Shopping Alerts will be shown only when the protection setting is enabled.
In each case, the alert may contain very important security warnings or may simply occur because you are running a certain application for the first time. Your reaction should depend on the information that is presented at the alert.
|
Note: This section is concerned only with the security alerts and notifications generated by the Antivirus, Firewall, HIPS, ViruscSope, Auto-Containment and Secure Shopping components of CIS. For other types of alert, see Comodo Message Center notifications, Notification Messages and Information Messages for other types of alerts. |
The title bar at the top of each alert is color coded according to the risk level presented by the activity or request.
- Yellow bar - Low Severity - In most cases, you can safely approve these requests. The 'Remember my answer' option is automatically pre-selected for safe requests
- Orange bar - Medium Severity - Carefully read the information in the alert description area before making a decision. These alerts could be the result of a harmless process by a trusted program or indicative of a malware attack. If you know the application to be safe, then it is usually okay to allow the request. If you do not recognize the application performing the activity or connection request then you should block it.
- Red bar - High Severity - These alerts indicate highly suspicious behavior that is consistent with the activity of a Trojan horse, virus or other malware program. Carefully read the information provided when deciding whether to allow it to proceed.
|
Note: Antivirus alerts are not ranked in this way. They always appear with a red bar. |
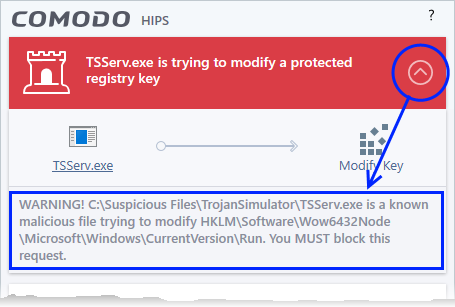
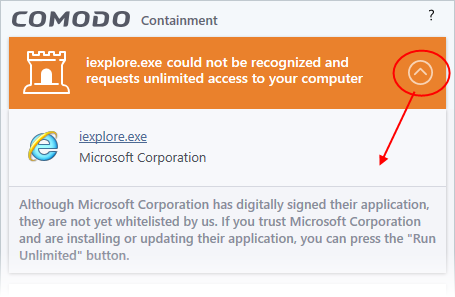
The description is a summary of the
nature of the alert and can be revealed by clicking the handle as
shown:
The description tells you the name of the software/executable that caused the alert; the action that it is attempting to perform and how that action could potentially affect your system. You can also find helpful advice about how you should respond.
Now that we've outlined the basic construction of an alert, let's look at how you should react to them.
Comodo Internet Security generates
an Antivirus alert whenever a virus or virus-like activity is
detected on your computer. The alert contains the name of the virus
detected and the location of the file or application infected by it.
Within the alert, you are also presented with response-options such
as 'Clean' or 'Ignore'.
|
Note: Antivirus alerts will be displayed only if the option 'Do not show antivirus alerts' is disabled. If this setting is enabled, antivirus notifications will be displayed. This option is found under 'Settings > Antivirus > Realtime Scan'. See Real-time Scan Settings for more details. |
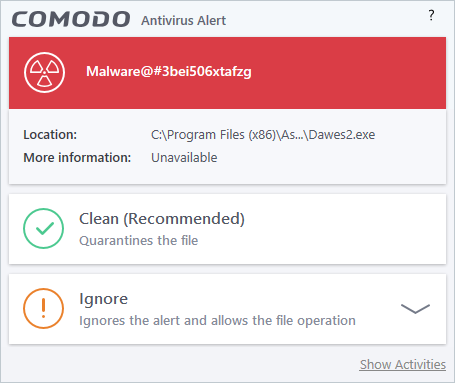
The following response-options are available:
- Clean - Disinfects the file if a disinfection routine exists. If no routine exists for the file then it will be moved to Quarantine. If desired, you can submit the file/application to Comodo for analysis from the Quarantine interface. See Manage Quarantined Items for more details on quarantined files.
- Ignore - Allows the process to run and does not attempt to clean the file or move it to quarantine. Only click 'Ignore' if you are absolutely sure the file is safe. Clicking 'Ignore' will open three further options:
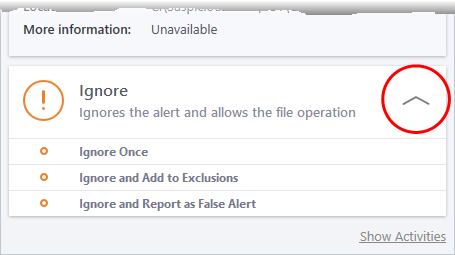
- Ignore Once - The file is allowed to run this time only. If the file attempts to execute on future occasions, another antivirus alert is displayed.
- Ignore and Add to Exclusions - The file is allowed to run and is moved to the 'Exclusions' list - effectively making this the 'Ignore Permanently' choice. No alert is generated if the same application runs again.
- Ignore
and Report as a False Alert - If you are sure that the file is
safe, select 'Ignore and Report as a False Alert'. CIS will then
submit this file to Comodo for analysis. If the false-positive is
verified (and the file is trustworthy), it will be added to the
Comodo safe list.
If you have chosen to not to show Antivirus Alerts through 'Settings' > 'Realtime Scanner Settings' by leaving the option 'Do not show antivirus alerts' enabled (default=enabled) and if CIS identifies a virus or other malware in real time, it will immediately block malware and provide you with instant on-screen notification:
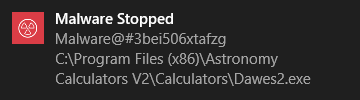
Please note that these antivirus notifications will be displayed only when 'Do not show antivirus alerts' check box in 'Antivirus' > 'Real-time Scan settings' screen is selected and 'Show notification messages' check box is enabled in 'Settings' > 'User Interface' screen.
Auto-scan alerts appear when you plug a removable device into your computer (USB stick, portable HDD,etc). The alert asks you whether you want to scan the device for viruses.
These alerts are only shown if 'Do not show auto-scan alerts' is disabled in 'Settings > Antivirus > Realtime Scan'. See Real-time Scan Settings if you want to read more.
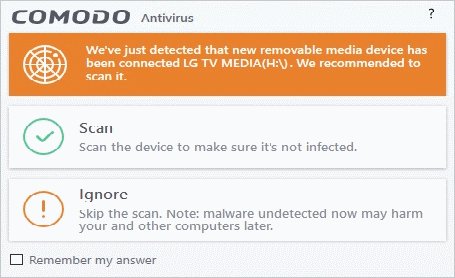
- Scan - CIS checks the device for viruses using the settings in the 'Manual Scan' profile. If this is not available then the scan uses the settings in the 'Full Scan' profile
- Ignore - The device is not scanned
- Remember my answer - CIS will automatically carry out your choice of scan or ignore when the device is connected in future. This only applies to the specific device. You will still see an alert if you connect a different device
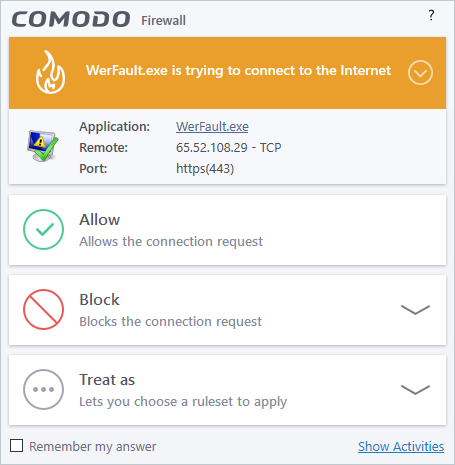
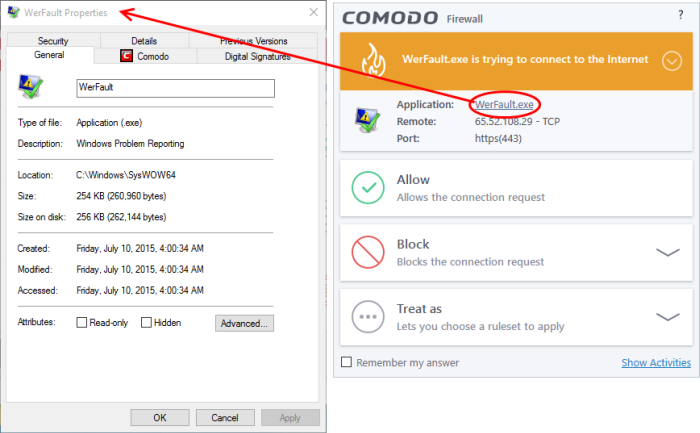
CIS generates a firewall alert when it detects unauthorized network connection attempts or when traffic runs contrary to one of your application or global rules. Each firewall alert allows you to set a default response that CIS should automatically implement if the same activity is detected in future. The followings steps will help you answer a Firewall alert:
|
Tip:
Clicking the 'Show Activities'
link at the bottom right will open the Process Activities List
dialog. The Process Activities dialog will display the list
activities of the processes run by the application. The 'Show Activities' link is available only if VirusScope is enabled under 'Settings' > 'VirusScope'. If none of the processes associated with the application that makes the connection attempt has started before the alert is generated, the 'Show Activities' link is disabled and will not open the Process Activities List dialog. |
-
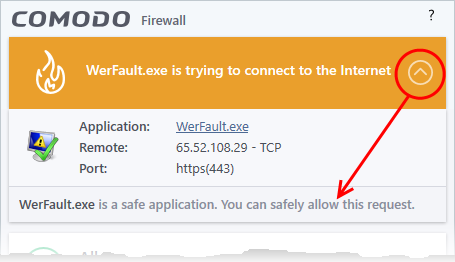
Carefully read the information displayed in clicking the down arrow in the alert description area. The Firewall can recognize thousands of safe applications. (For example, Internet Explorer and Outlook are safe applications). If the application is known to be safe - it is written directly in the security considerations section along with advice that it is safe to proceed. Similarly, if the application is unknown and cannot be recognized you are informed of this.
If it is one of your everyday applications and you want to allow it Internet access to then you should select Allow.
If you don't recognize the application then we recommend you Block the application. By clicking the handle to expand the alert, you can choose to 'Block' the connection (connection is not allowed to proceed), 'Block and Terminate' (connection is not allowed to proceed and the process/application that made the request is shut down) or 'Block, Terminate and Reverse' (connection is not allowed to proceed, the process/application that made the request is shut down and the changes made by the process/application to other files/processes in the system will be rolled back).
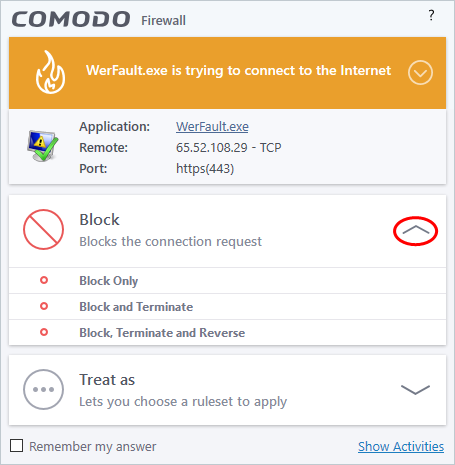
|
Note: 'Block, Terminate and Reverse' option will be available only if VirusScope is enabled under 'Settings' > 'VirusScope'. Also, if none of the processes associated with the application that makes the connection attempt has started before the alert is generated, the 'Block, Terminate and Reverse' option will not be available. |
-
If you are sure that it is one of your everyday application, try to use the 'Treat As' option as much as possible. This allows you to deploy a predefined firewall ruleset on the target application. For example, you may choose to apply the policy Web Browser to the known and trusted applications like Comodo Dragon, 'Firefox' and 'Opera'. Each predefined ruleset has been specifically designed by Comodo to optimize the security level of a certain type of application.
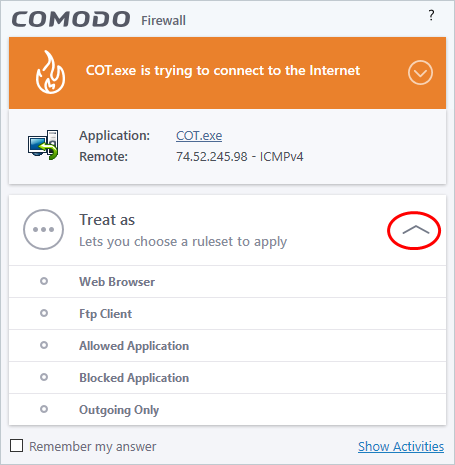
Remember to select 'Remember My Answer' for ruleset to be created for the application and applied in future.
-
If the Firewall alert reports a behavior, consistent with that of a malware in the security considerations section, then you should block the request AND select 'Remember My Answer' to make the setting permanent.
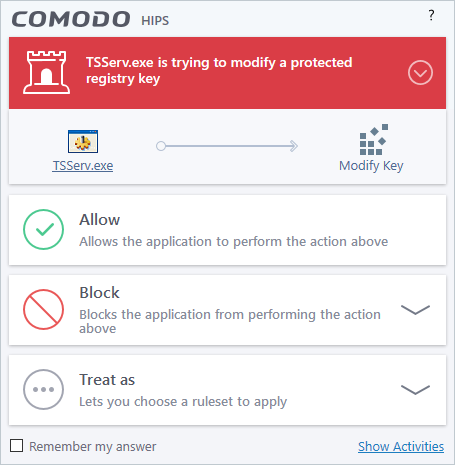
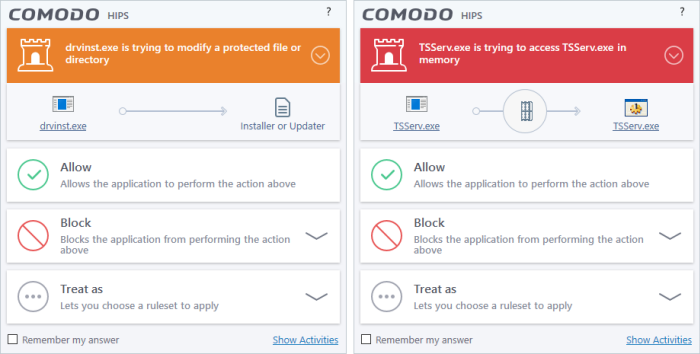
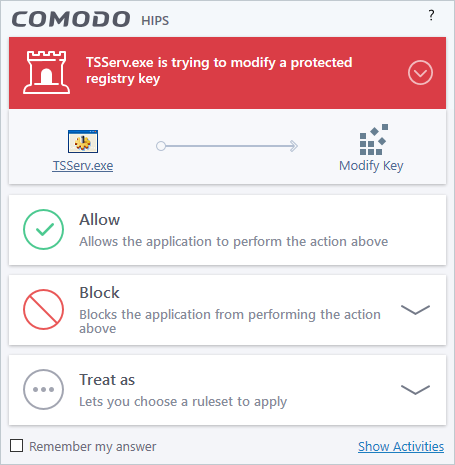
Comodo Internet Security generates a HIPS alert based on the behavior of applications and processes running on your system. Please read the following advice before answering a HIPS alert:
|
Tip:
Clicking the 'Show Activities'
link at the bottom right will open the 'Process
Activities List dialog'. The Process Activities dialog will
display the list activities of the processes run by the
application. The 'Show Activities' link is available only if VirusScope is enabled under 'Settings' > 'VirusScope'. If none of the processes associated with the application that makes the connection attempt has started before the alert is generated, the 'Show Activities' link is disabled and will not open the Process Activities List dialog. |
-
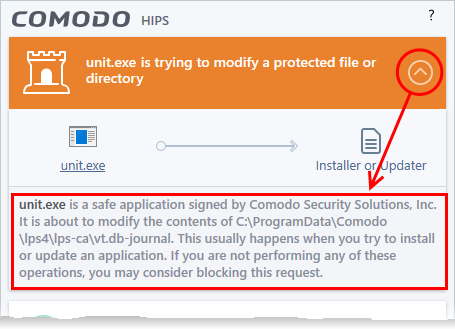
Carefully read the information displayed after clicking the handle under the alert description. Comodo Internet Security can recognize thousands of safe applications. If the application is known to be safe - it is written directly in the security considerations section along with advice that it is safe to proceed. Similarly, if the application is unknown and cannot be recognized, you are informed of this.
If it is one of your everyday applications and you simply want it to be allowed to continue then you should select Allow.
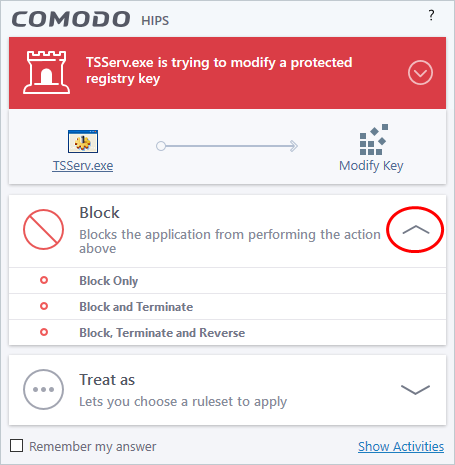
If you don't recognize the application then we recommend you select Block the application. By clicking the handle to expand the alert, you can choose to
- 'Block' - The application is not allowed to run
- 'Block and Terminate' - The application is not allowed to run and the processes generated by it are terminated thereby shutting down the application
- 'Block, Terminate and Reverse' - The application is not allowed to run, the processes generated by it are terminated and the changes made by the processes/application to other files/processes in the system will be rolled back.
|
Note: 'Block, Terminate and Reverse' option will be available only if VirusScope is enabled under 'Settings' > 'VirusScope'. |
-
If you are sure that it is one of your everyday applications and want to enforce a security policy (ruleset) to it, please use the 'Treat As' option. This applies a predefined HIPS ruleset to the target application and allows the application to run with access rights and protection settings as dictated by the chosen ruleset.
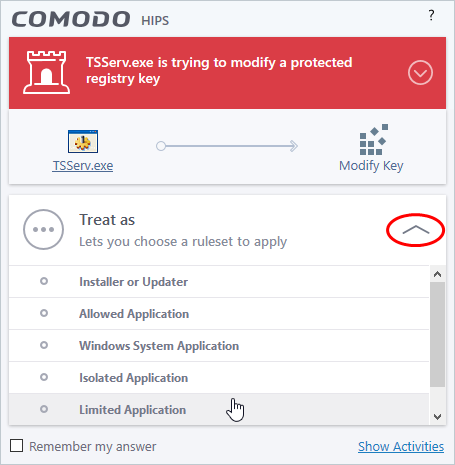
Avoid using the 'Installer or Updater' ruleset if you are not installing an application. This is because treating an application as an 'Installer or Updater' grants maximum possible privileges onto to an application - something that is not required by most 'already installed' applications. If you select 'Installer or Updater', you may consider using it temporarily with 'Remember My Answer' left unchecked.
-
Pay special attention to 'Device Driver Installation' and 'Physical Memory Access' alerts. Again, not many legitimate applications would cause such an alert and this is usually a good indicator of malware / rootkit like behavior. Unless you know for a fact that the application performing the activity is legitimate, then Comodo recommends blocking these requests.
4. 'Protected Registry Key' Alerts usually occur when you install a new application. If you haven't been installing a new program and do not recognize the application requesting the access, then a 'Protected Registry Key Alert' should be a cause for concern.
5. 'Protected File Alerts' usually occur when you try to download or copy files or when you update an already installed application.
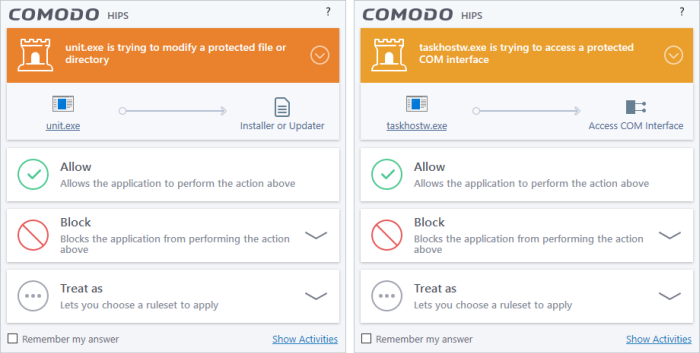
Were you installing new software or trying to download an application from the Internet? If you are downloading a file from the 'net, select 'Allow', without selecting 'Remember my answer' option to cut down on the creation of unnecessary rules within the firewall.
If an application is trying to create an executable file in the Windows directory (or any of its subdirectories) then pay special attention. The Windows directory is a favorite target of malware applications. If you are not installing any new applications or updating Windows then make sure you recognize the application in question. If you don't, then click 'Block' and choose 'Block Only' from the options, without selecting Remember My answer option.
If an application is trying to create a new file with a random file name e.g. "hughbasd.dll" then it is probably a virus and you should block it permanently by clicking 'Treat As' and choosing 'Isolated Application' from the options.
-
If a HIPS alert reports a malware behavior in the security considerations area then you should 'Block the request' permanently by selecting 'Remember My Answer' option. As this is probably a virus, you should also submit the application in question, to Comodo for analysis.
-
Unrecognized applications are not always bad. Your best loved applications may very well be safe but not yet included in the Comodo certified application database. If the security considerations section says "If xxx is one of your everyday applications, you can allow this request", you may allow the request permanently if you are sure it is not a virus. You may report it to Comodo for further analysis and inclusion in the certified application database.
-
If HIPS is in 'Paranoid' mode, you probably are seeing the alerts for any new applications introduced to the system - but not for the ones you have already installed. If required, you may review files with 'Unrecognized' rating in the 'File List' interface and remove them from the list.
-
Avoid using Trusted Application or Windows System Application policies for you email clients, web browsers, IM or P2P applications. These applications do not need such powerful access rights.
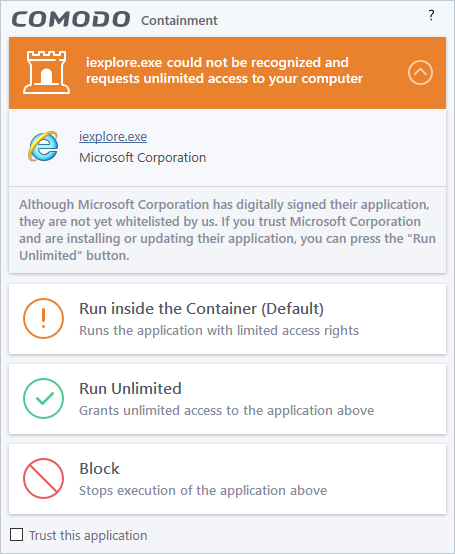
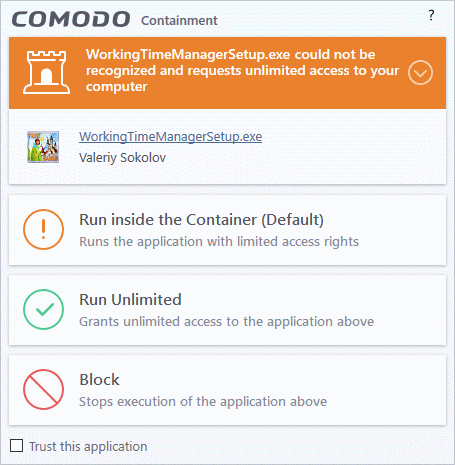
Comodo Internet Security generates
a Containment alert if an application or a process tries to perform
certain modifications to the operating system, its related files or
critical areas like Windows Registry and when it automatically
contained an unknown application.
Please read the following advice before answering a Containment alert:
-
Carefully read the information displayed after clicking the handle under the alert description. Comodo Internet Security can recognize thousands of safe applications. If the application is known to be safe - it is written directly in the security considerations section along with advice that it is safe to proceed. Similarly, if the application is unknown and cannot be recognized, you are informed of this.
-
If you are sure that the application is authentic and safe and you simply want it to be allowed to continue then you should select 'Run Unlimited'. If you want the application not to be monitored in future, select 'Trust this application' checkbox. The application will be added to Trusted Files list.
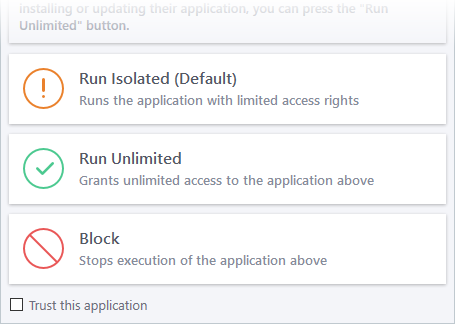
- If you are unsure of the safety of the software, then Comodo recommends that you run it with limited privileges and access to your system resources by clicking the 'Run Isolated' button. See 'Unknown Files: The Scanning process' for more explanations on applications run with limited privileges.
- If you don't recognize the application then we recommend you select to 'Block' the application.
Run with Elevated Privileges Alert
The container will display this kind of alert when the installer of an unknown application requires administrator, or elevated, privileges to run. An installer that is allowed to run with elevated privileges is permitted to make changes to important areas of your computer such as the registry.
- If you have good reason to trust the publisher of the software then you can click the 'Run Unlimited' button. This will grant the elevated privilege request and allow the installer to run.
- If you are unsure of the safety of the software, then Comodo recommends that you run it with restricted access to your system resources by clicking the 'Run Isolated' button.
- If this alert is unexpected then you should abort the installation by clicking the 'Block' button (for example, you have not proactively started to install an application and the executable does not belong to an updater program that you recognize).
- If you select 'Trust this application' then CIS will include this to Trusted Files list and no future alerts will be generated when you run the same application.
|
Note: You will see this type of alert only if you have enabled 'Detect programs which require elevated privileges e.g. installers or updaters', and disabled 'Do not show privilege elevation alerts' in containment settings. See 'Containment
Settings' for more details. |
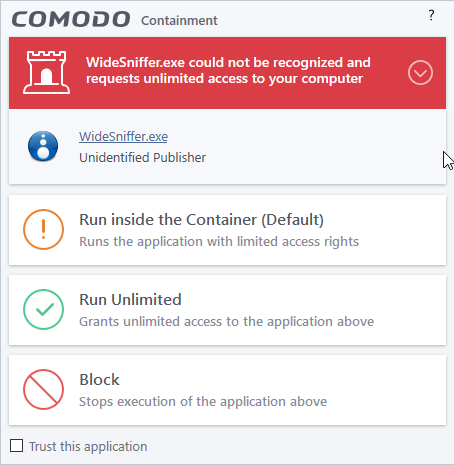
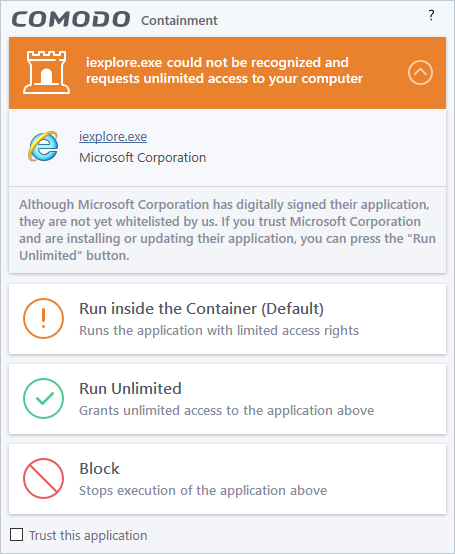
There are two versions of this alert - one for unknown installers that are not digitally signed and the second for unknown installers that are digitally signed but the publisher of the software has not yet been white-listed (they are not yet a 'Trusted Software Vendor').
Unknown and not digitally signed
Unknown and digitally signed but the publisher not yet whitelisted (Not yet a 'Trusted Vendor')
- Unknown and unsigned installers should be either isolated or blocked.
- Unknown but signed installers can be allowed to run if you trust the publisher, or may be isolated if you would like to evaluate the behavior of the application.
Also see:
- 'Unknown Files: The Scanning Processes' - to understand process behind how CIS scans files.
- 'Vendor List' - for an explanation of digitally signed files and trusted software vendors.
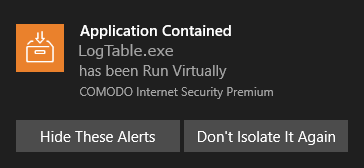
A notification will be shown when an application is automatically run inside the container by the auto-containment rules.
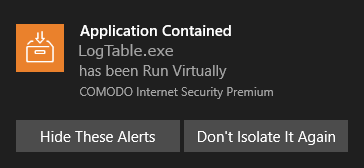
- Hide These Alerts – CIS will not show containment alerts if the same application is auto-contained in future.
- Don't
Isolate It Again – An 'Ignore' rule is added for the application in the
Auto-Containment rules. The application will not be auto-contained
in future. See Auto-Containment
Rules for more details.
CIS checks a
file's trust rating on our cloud severs as part of a real-time scan.
The software can generate alerts when it finds a file with an
'Unrecognized' or 'Malicious' rating.
You will
these alerts if you have disabled 'Do not show popup alerts'
in 'Settings' > 'File Rating' > 'File Rating Settings'.
- Unknown files - The following alert is shown:
You can choose from these actions:
- Run inside the Container - Executes the program inside the container with limited access rights.
- Run Unlimited - Lets the program run as normal on your computer, outside the container. The file is added to the file list as a 'Trusted' file. See File List for more details.
- Block - The program is terminated and not allowed to run.
- Malicious files - The program is automatically blocked and quarantined. You will see the following type of alert:
- Don't Isolate It Again - Select this option if you are sure you can trust the file.
- The file is marked as 'Trusted' in your local file list, and will be allowed to run without restriction in future. See File List for more details.
Comodo Internet Security generates a VirusScope alert if a running process performs an action that might represent a threat to your privacy and/or security. Please note that VirusScope alerts are not always definitive proof that malicious activity has taken place. Rather, they are an indication that a process has taken actions that you ought to review and confirm because they have the potential to be malicious. You can review all actions taken by clicking the 'Show Activities' link.
Please read the following advice before answering a VirusScope alert:
-
Carefully read the information displayed in the alert. The 'More Information' section provides you the nature of the suspicious action.
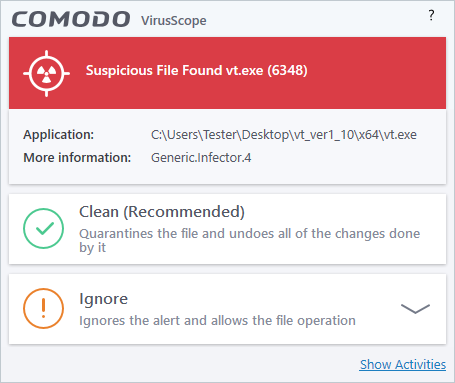
- If you are not sure on the authenticity of the parent application indicated in the 'Application' field, you can safely reverse the changes effected by the process and move the parent application to quarantine by clicking 'Clean'.
- If it is a trusted application, you can allow the process to run, by clicking 'Ignore' and selecting the option from the drop-down.
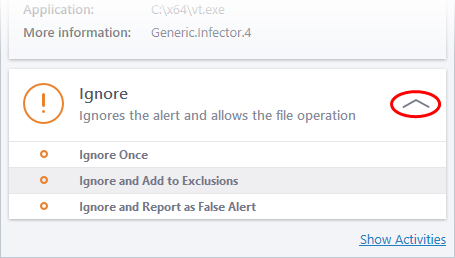
- Ignore Once - The process is allowed to run this time only. If the process attempts to execute on future occasions, another VirusScope alert is displayed.
- Ignore and Add to Exclusions - The file is allowed to run and will not be contained in the future. See 'Auto-Containment Rules' for help to configure which types of files should be auto-contained.
- Ignore and Report as False Alert - If you are sure that the file is safe, select 'Ignore and Report as a False Alert'. CIS will then submit this file to Comodo for analysis. If the false-positive is verified (and the file is trustworthy), it will be added to the Comodo safe list.
- To view the activities of the processes, click the 'Show Activities' link at the bottom right. The Process Activities List dialog will open with a list of activities exhibited by the process.
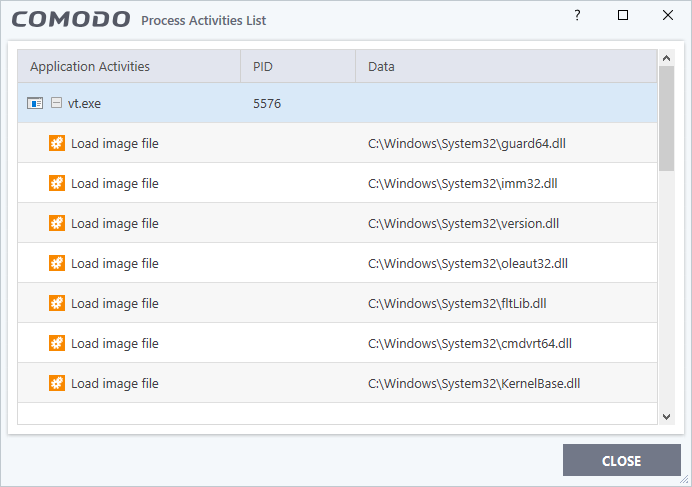
Column Descriptions
- Application Activities - Displays the activities of each of the processes run by the parent application.
- File actions: The process performed a file-system operation (createmodifyrenamedelete file) which you might not be aware of.
- Registry: The process performed a registry operation (created/modified a registry key) which might not be authorized.
- Process: The process created a child process which you may not have authorized or have been aware of.
- Network: The process attempted to establish a network connection that you may not have been aware of.
- If the process has been terminated, the activities will be indicated with gray text and will appear in the list until you view the 'Process Activities List' interface. If you close the interface and reopen the list within five minutes, the activities will appear in the list. Else, the terminated activities will not be displayed in the list.
- PID - Process Identification Number.
- Data - Displays the file affected by the action.
The 'Secure Shopping Alert' will be displayed whenever a user opens a website that is added to the list of websites added for Secure Shopping protection. The user can choose to open the website inside the Secure Shopping environment, with a secure browser window or continue with the current browser. See Comodo
Secure Shopping for more
details.
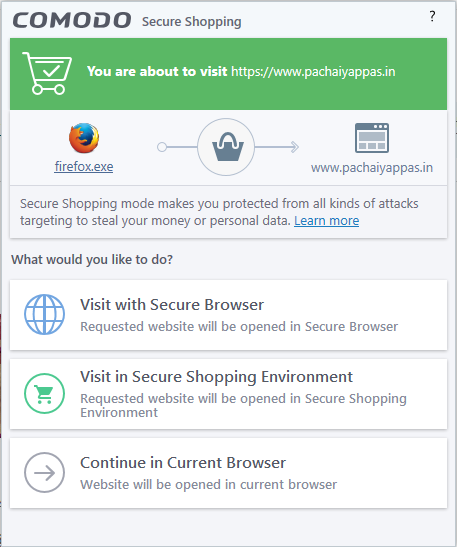
The options available in the alert are:
- Visit with Secure Browser - The website will open in secure mode (incognito mode) /private mode of the default browser.
- Visit in Secure Shopping Environment - The website will open using the web browser that is configured for the secure shopping mode.
- Continue in Current Browser - The website will open in normal mode using the default browser.



