Containment Settings
Click 'Settings' > 'Containment' > 'Containment Settings'
- The settings area lets you configure how proactive the auto-containment feature should be, and which types of files it should check.
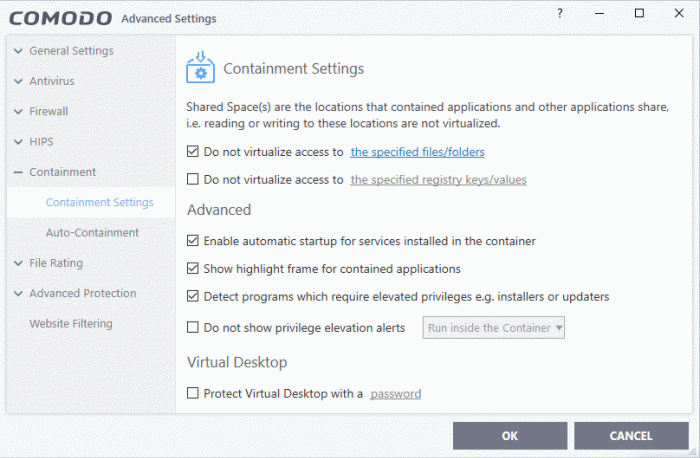
- By default, contained applications can access folders, files and registry keys on your local system, but cannot make changes to them
- The ‘Do not virtualize...’ settings let you create exceptions to these policies if required
- You
can also adjust settings for the clipboard, display mode, virtual
desktop, and more
Do not virtualize access to the specified files/folders - Specify files/folders on the host computer that contained applications are allowed to write to. By default, contained applications write to a virtual file system, and cannot access files/folders on the host system
- Enable the option then click 'the specified files/folders' link
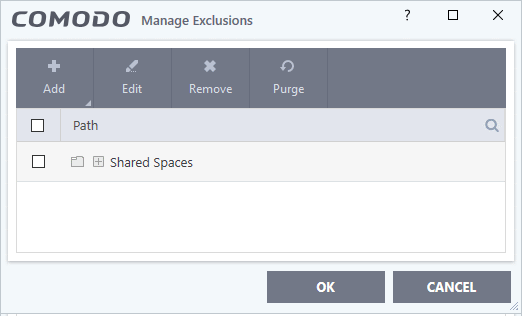
- The exclusions dialog shows files and folders that can be modified by contained applications. By default, 'Shared Space' is the only folder they can write to:
- Click
the 'Add' button then select the item you want to exclude:
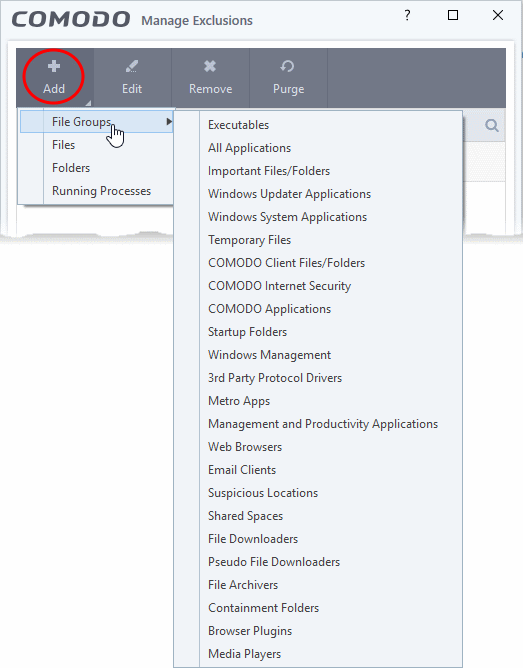
- File Groups - Choose a category of files or folders to which access should be granted
- For example, select 'Executables' to allow access to files with extensions .exe .dll .sys .ocx .bat .pif .scr .cpl, */cmd.exe *.bat, *.cmd
See File Groups if you want more help with file groups
Files - Pick specific files on the host that contained applications can access
- Folders - Specify folders that can be accessed by contained applications. Access is granted to all files in the folder
- Running Processes - Choose a process currently running on your computer. The parent application of the process is added to the exclusions
- Edit - Select an item and click 'Edit' to change the target file or folder
- Remove - Select an item and click 'Remove' to delete an exception
- Purge - Checks that all files and folders covered in exceptions are still present on your computer. Purge automatically removes any items it can no longer locate
- Click 'OK' to implement your settings
Do not virtualize access to the specified registry keys/values - Specify registry keys on the host computer that contained applications are allowed to write to. By default, contained applications write to a virtual registry, and cannot access the real registry on the host system.
- Select the option then click 'the specified registry keys/values' link
- The exclusions dialog shows keys on the host which contained applications are allowed to access
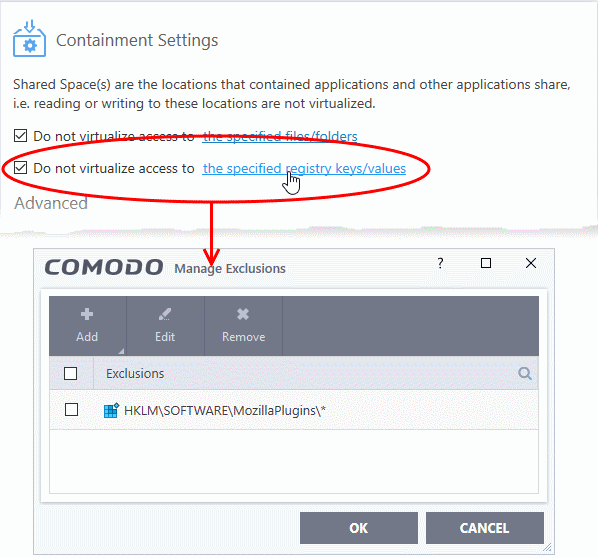
- Click the 'Add' button then select the keys you want to exclude:
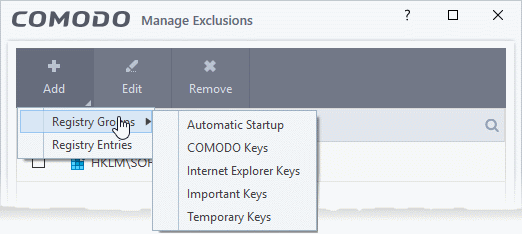
- Registry Groups - Exclude a predefined collection of registry keys. See 'Registry Groups' for an explanation of registry groups as defined in CIS
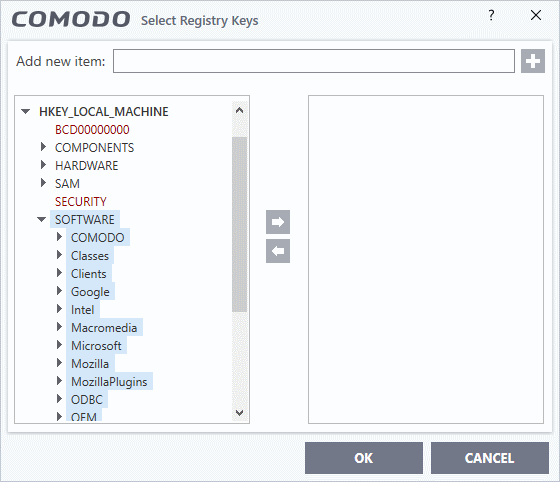
- Edit - Select an item and click 'Edit' to change the target path
- Remove - Select a key or group and click 'Remove' to delete the exception
- Click 'OK' to implement your settings
- Enable automatic startup for services installed in the container – CIS launches contained services at Windows startup if this option is enabled. (Default = Enabled)
- Clear this box if you do not want those services to run at startup
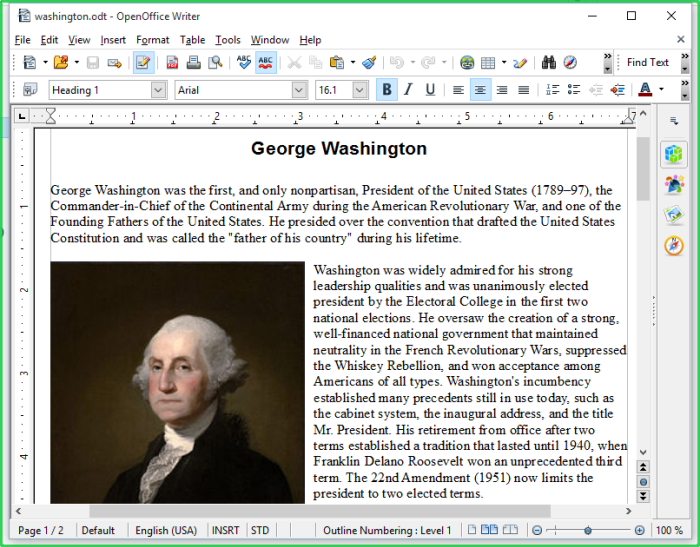
- Show highlight frame for contained applications - CIS displays a green border around the windows of programs that are running in the container. (Default = Enabled)
The following screenshot shows an Open Office document running in the container:
- Detect programs which require elevated privileges e.g. installer or updaters: CIS generates an alert when it detects an installer/updater that requires admin/elevated privileges to run. An installer that is allowed to run with elevated privileges can make changes to important areas of your computer such as the registry. (Default = Enabled)
- Example alert:
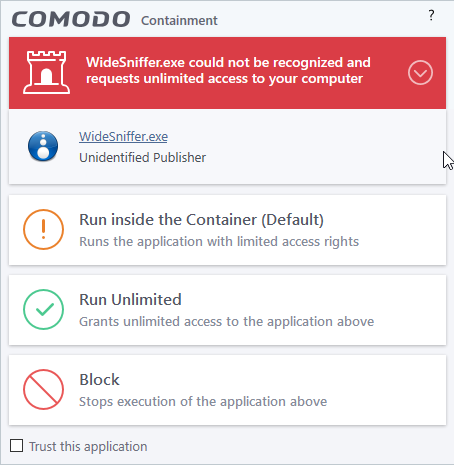
- Run Isolated - Runs the installer/updater in the container
- Run Unlimited - Runs the installer/updater on your local computer, outside the container
- Block - Terminates the installer/updater
- See 'Understand Security Alerts' for more details
- Disable this option if you want CIS not to monitor applications that request elevated privileges on your computer
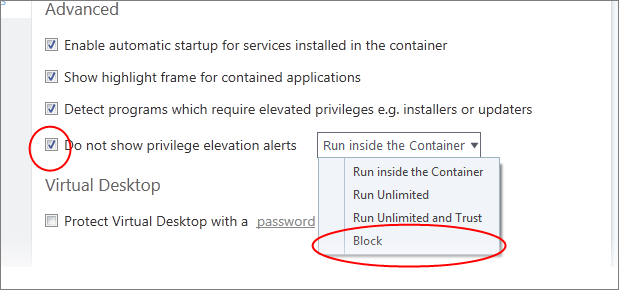
- Do not show privilege elevation alerts: Whether or not CIS shows alerts (as shown above) when a new or unrecognized application requires admin or elevated privileges to run.
- If you disable alerts, you need to choose a default action that CIS should implement when it detects such an application:
- Allow contained application access to clipboard: By default, applications in the container cannot access data in your clipboard. This can sometimes cause inconvenience when trying to copy and paste
- Enable this option to grant contained applications access the clipboard. This change requires a system restart
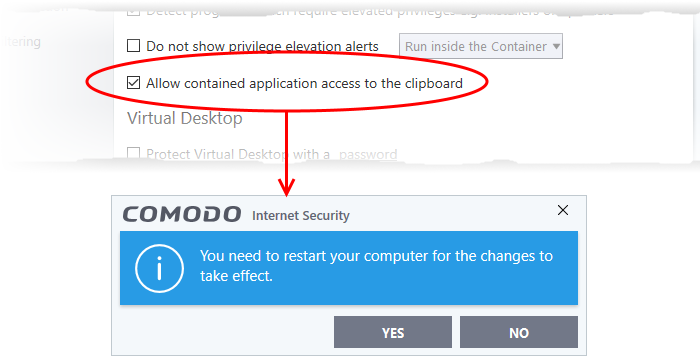
- Click 'Yes' to confirm your setting
- Contained apps can access your clipboard after the next restart of your computer
Virtual Desktop Settings
The 'Virtual Desktop' Settings area allows you to password protect your Virtual Desktop. Once set, the password has to be entered in order to close the Virtual Desktop:
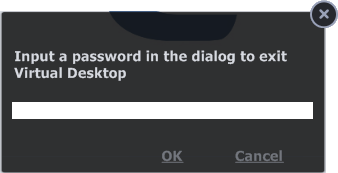
This is a security measure to prevent guests or younger users from closing the Virtual Desktop and accessing the host, potentially exposing your computer to danger.
Set an exit password for the Virtual Desktop:
- Check the 'Protect Virtual Desktop with a password' box then click the password link. The 'Create/change password' dialog will appear:
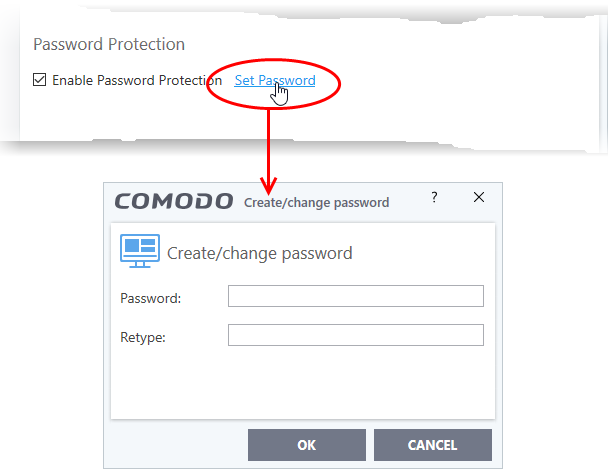
- Type a password that cannot easily be guessed. It should be at least 8 characters long and contain a combination of uppercase and lowercase letters, numbers and special characters
- Re-enter the password in the 'Retype' field then click 'OK'
You will now be asked for a password every time you exit the Virtual Desktop.
|
Note. You may see an error if an app on the host tries to update itself at the same time as that app is updating itself in the container. This is a classic Windows sharing violation which is shown when an app attempts to write to a file that is already in use. Please shut down the contained version of the app then run the update on the locally hosted version. The contained version will function correctly once the update to the local version is complete. |



