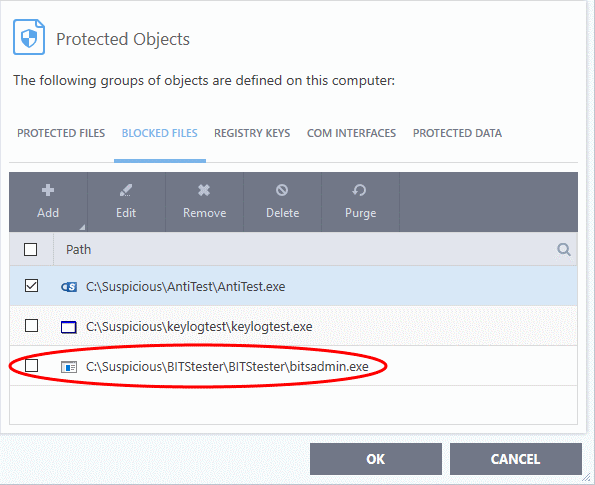
Blocked Files
- If you block a file or folder then you completely prevent access to it from other processes or users - effectively cutting it off from the rest of your system.
- If the file you block is an executable, then neither you nor anything else is able to run that program.
- Unlike files in 'Protected Files', you cannot selectively allow access a blocked file.
Open the 'Blocked Files' area
- Click 'Settings' at the top-left of the home screen
- Click 'HIPS' > 'Protected Objects' on the left
- Click the 'Blocked Files' tab
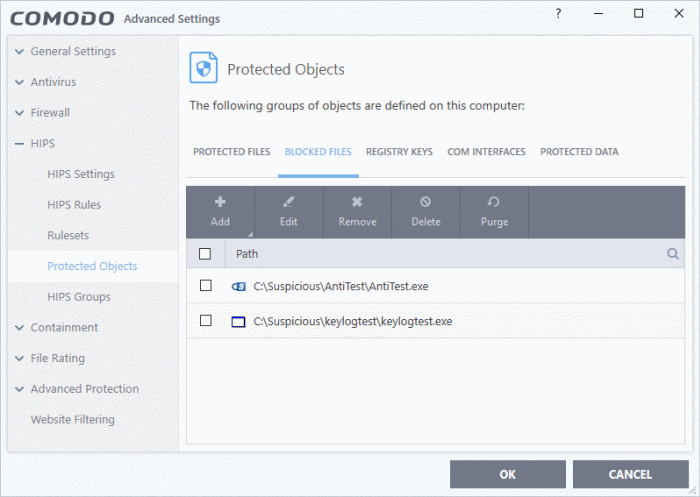
Search
Option:
- Click the search icon at upper-right and enter the name of a file in full or part.
The buttons at the top provide the following options:
- Add - Block a new file, file-group, folder or running process
- Edit - Modify the path/location of the target item
- Remove - Release a file from the blocked files list.
- Delete - Removes the highlighted file from your computer
- Purge - Runs a check to verify that all files in the list are actually installed at the path specified. If not, the item is removed from the list.
Right-click Options:
- Right-click on an item to add, edit, remove/delete, and purge files:
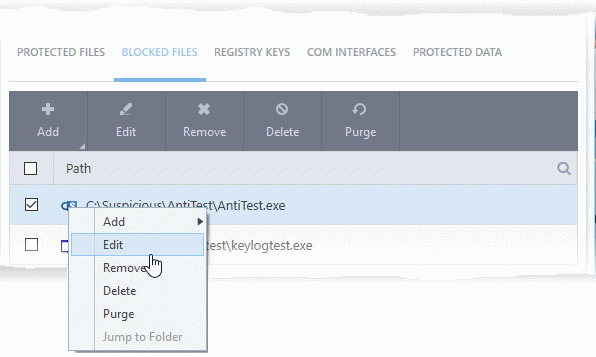
The options available are same as described above.
See the following sections if you need more help:
Manually add individual file or application to block
file list
- Click 'Settings' on the CIS home screen
- Click
'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Click the 'Add' button
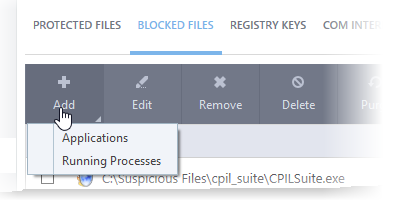
You can add applications to be blocked by following methods:
- Click 'Settings'on the CIS home screen
- Click
'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Click 'Add' > 'Applications'
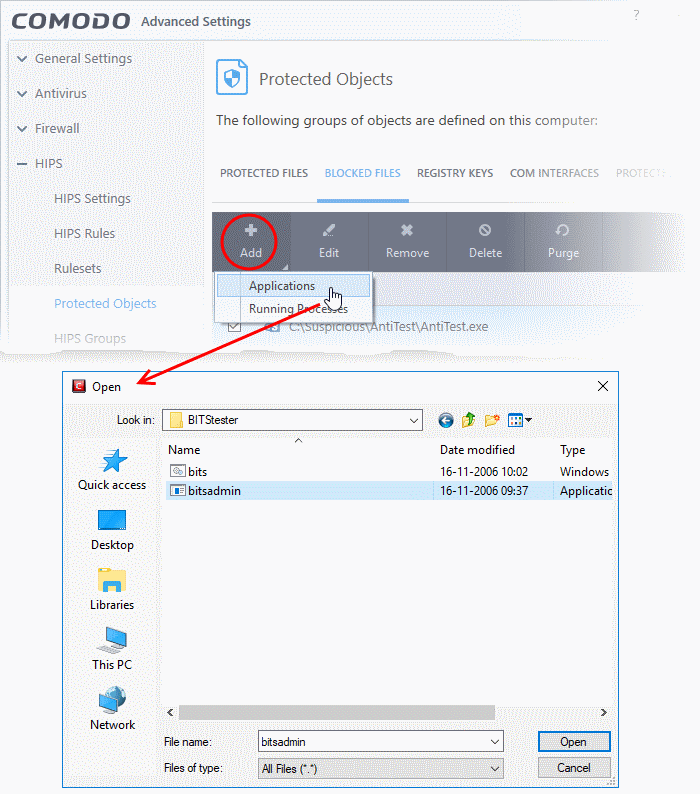
- Navigate to the file you want to add to 'Blocked Files' and click 'Open'.
The file will be added to 'Blocked Files' list:
- Repeat
the process to add more files
- Click 'OK' to save your changes
Add an application from a running process
- Click 'Settings' on the CIS home screen
- Click
'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Click 'Add' > 'Running Processes'
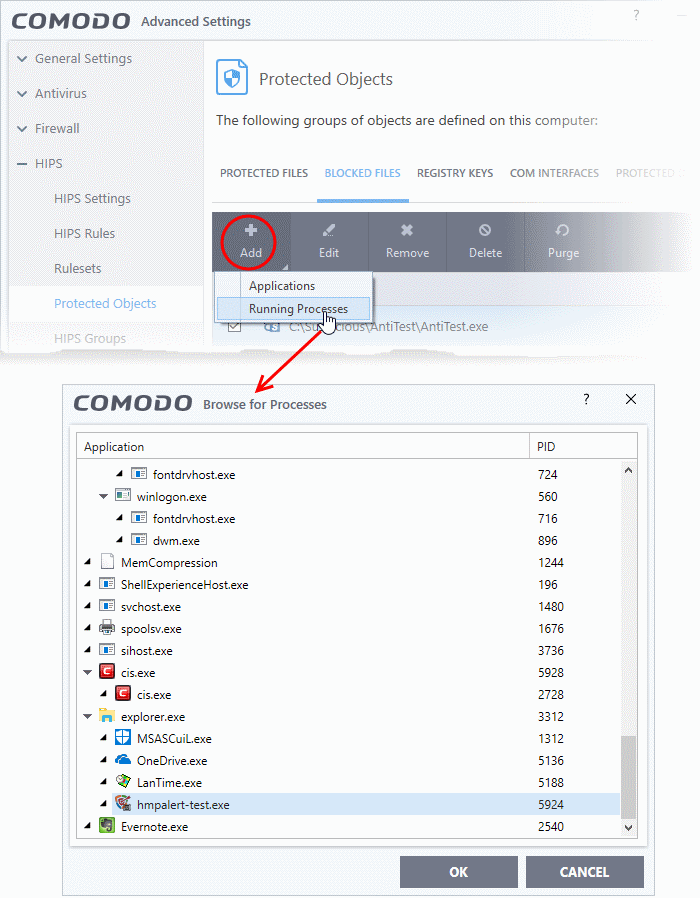
This shows a list of processes currently running on your computer.
- Select the process you want to block and click 'OK'. The parent application of the process is added to blocked files
- Repeat the process to add more applications
- Click 'OK' to save your changes
Change the file path of an item in the blocked files list
- Click 'Settings on the CIS home screen
- Click 'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Select an item and click the 'Edit' button or right-click on an item and choose 'Edit'
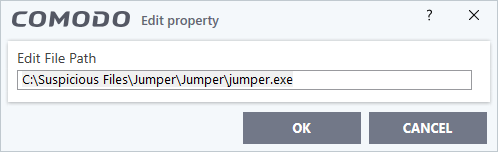
- Edit the file path, if you have relocated the file and click 'OK'
Release an item from blocked files list
- Click 'Settings' on the CIS home screen
- Click 'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Select
the item from the list and click the 'Remove' button or right-click
on an item and choose 'Remove'
The selected item will be removed from the 'Blocked Files' list. CIS will not stop the application from opening in the future
Permanently delete a
blocked file from your system
- Click 'Settings on the CIS home screen
- Click
'HIPS' > 'Protected Objects'
- Click the 'Blocked Files' tab
- Select
the item from the list and click the 'Delete' button
The selected item will be deleted from your computer immediately.
|
Warning: Deleting a file from from the 'Blocked Files' interface permanently deletes the file from your system, rendering it inaccessible in future and it cannot be undone. Ensure that you have selected the correct file to be deleted before clicking 'Delete'. |



