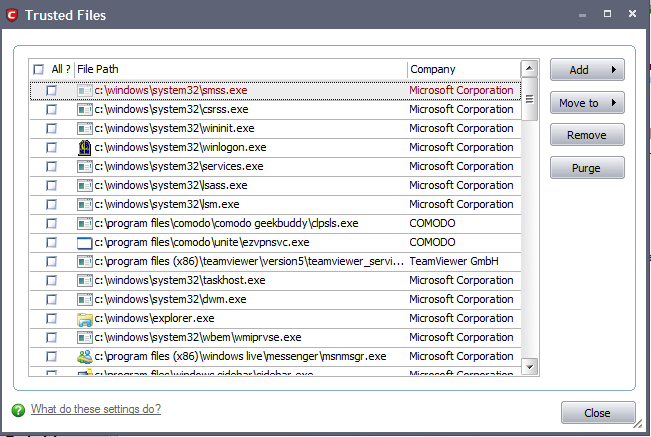
Trusted Files
Defense+ allows you to define a personal safe list of files to complement the default Comodo safe list.
Files added to the Trusted Files area are automatically given Defense+ trusted status. If an executable is unknown to the Defense+ safe list then, ordinarily, it and all its active components generate Defense+ alerts when they run. Of course, you could choose the 'Treat this as a Trusted Application' option at the alert but it is often more convenient to classify entire directories of files as 'Trusted Files'.
By adding executables to this list (including sub folders containing many components) you can reduce the amount of alerts that Defense+ generates whilst maintaining a higher level of Defense+ security. This is particularly useful for developers that are creating new applications that, by their nature, are as yet unknown to the Comodo safe list. Files can be transferred into this module by clicking the 'Move to' button in the 'Unrecognized Files' area.
Adding files to Trusted Files list
Defense+ allows you to add files and executables to the list of Trusted Files so that those files will be given Trusted status. For the files added manually, it generates a hash or a digest of the file using a pre-defined algorithm and saves in its database. On access to any file, its digest is created instantly and compared against the list of stored hashes to decide on whether the file has 'Trusted' status. By this way, even if the file name is changed later, it will retain its Trusted status as the hash remains same. However you can also add files by their file names, but if you happen to change the file name later, it looses its 'Trusted' status.
To add new file(s) to Trusted Files list
-
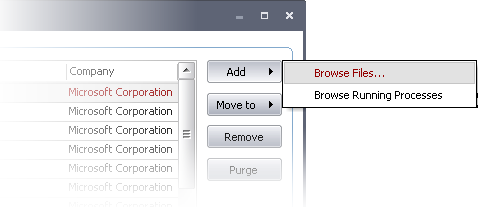
Click 'Add' from 'Trusted Files' interface.
-
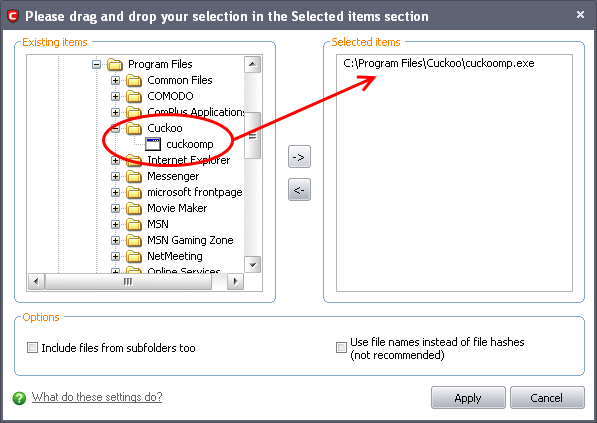
Browse Files - Opens a drag and drop dialog that enables you to select the files/folders from the left and side pane and move them to the right hand side pane by clicking the right arrow.
-
Include files from subfolders too - Select this option if you want all the files included in the subfolders to be added to Trusted files list in case you are selecting a folder from the left hand side pane.
-
Use file names instead of file hashes - On selecting this option, the selected files will be stored in the database with the file names instead of file hashes. Use this option only for the files which should not be trusted if their file names are changed.
-
Click 'Apply' for adding the files in the left hand side pane to the 'Trusted Files' list.
-
Browse Running Processes - Opens Choose a process dialog which allows you to select a currently running process. On selecting a process, the parent application, which invoked the process will be added to 'Trusted Files' list.
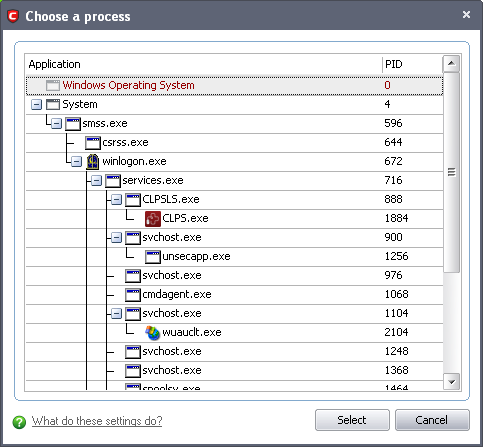
-
Select the process and click 'Select'. The parent application will be added to the 'Trusted Files' list.
To move an included entry to Unrecognized Files or Blocked Files
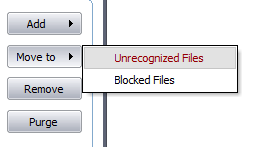
The 'Move to...' option allows you to transfer the selected files out of the 'Trusted Files' area into either the Unrecognized Files or Blocked Files areas of Defense+.
To remove an included entry from the Trusted Files list
-
Select the entry and click 'Remove' button. The file is only removed from the list and not deleted from your system.
To remove invalid entries (programs / files that are not present or uninstalled from your computer) automatically
-
Select the entry and click 'Purge' button.
Comodo Internet Security User Guide | © 2012 Comodo Security Solutions Inc. | All rights reserved



