Unrecognized Files
Once installed, Defense+ watches all file system activity on your computer. Every new executable file introduced to the computer, is first scanned against the Comodo certified safe files database. If they are not safe, they are added to the 'Unrecognized Files' for users to review and possibly submit to Comodo. Apart from new executables, any executables that are modified are also moved to the ' Unrecognized Files' area.
“Unrecognized Files” is specifically important while Defense+ is in 'Clean PC Mode'. In Clean PC Mode, the files in ' Unrecognized Files' are NOT considered clean. For more information, please check 'Clean PC Mode' on the Defense+ settings page.
The 'Unrecognized Files' Area allows the user to:
-
Assess the pending files to determine whether or not they are to be trusted. If they are trustworthy, they can be moved to 'Trusted Files' using the 'Move to' button. Similarly, files that are suspicious can be moved to the 'Blocked Files' area.
-
Use the 'Lookup...' feature to see if the master Comodo safe list contains more information.
-
Send the file to Comodo for analysis by clicking the 'Submit' button which automatically begins the file submission process.
-
Manually add files to the pending list for look-ups or submitting to Comodo.
-
Use the 'Purge' feature to scan the list for files that no longer exist on your system and remove them from the 'Unrecognized Files' list.
-
Delete a selected file from the system by clicking 'Delete File' button
To access Unrecognized Files interface Files
-
Navigate to: Defense+ Tasks > Unrecognized Files.
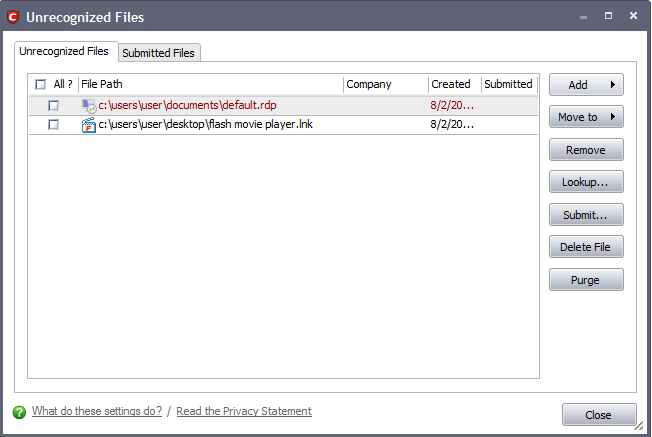
This area contains two tabs:
-
Unrecognized files – Displays a list of files identified as suspicious by Defense+ and the files added to this area manually.
-
Submitted Files - Displays a list of files that were submitted to Comodo for analysis.
Comodo Internet Security User Guide | © 2012 Comodo Security Solutions Inc. | All rights reserved



