Integrate your Windows Defender Account with MDR
You can integrate your Windows Defender account with MDR so any threats and behavioral anomalies are detected. Once integrated, our SOC team analyzes data logs from your Windows Defender account for malware activity and other anomalies.
You have to first register an application in Microsoft Entra ID and then configure MDR to collect data.
Configuration Steps
- Sign in to the Azure Portal.
- Open Microsoft Entra ID.
- Select App Registrations.
- Click New Registration.
- Provide a Name → Register.
After registration:
- Open your app.
- Copy the following:
- Application (Client) ID
- Directory (Tenant) ID
- Go to Certificates & Secrets.
- Under Client Secrets<>, click New Client Secret.
- Add description → choose expiry → Add.
- Copy the Secret Value (only shown once).
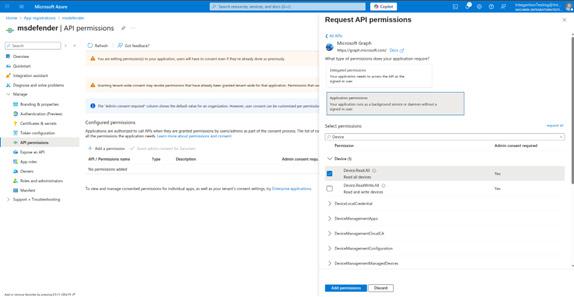
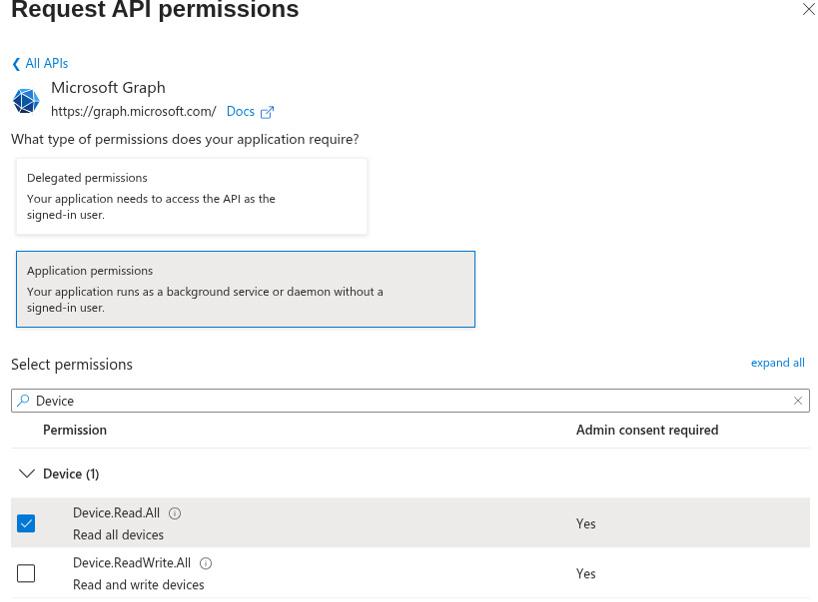
- Go to API Permissions → Add a Permission.
- Choose Microsoft Graph → Application Permissions and add the following:
- Device.Read.All — Allows the application to retrieve the list of all devices onboarded to Microsoft Defender.
- Directory.Read.All — Allows the application to read tenant and directory metadata required to resolve device and user context.
- SecurityAlert.Read.All — Allows the application to retrieve Microsoft Defender security alerts, including DLP-related alerts.
- SecurityIncident.Read.All — Allows the application to retrieve incidents associated with Microsoft Defender alerts.
- Log into your Xcitium account and open MDR.
- Click 'Managed Security' in the top navigation, then select the 'Integrations' tab.
- Scroll down to 'Integrate your Windows Defender account' and fill in the following fields:
- Tenant ID
- Client ID
- Secret Key
- Click 'Register Your Account'.
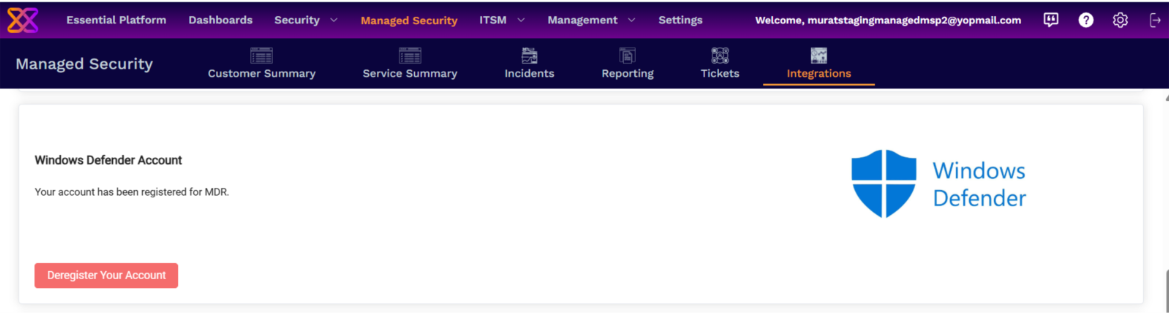
That's it, your Windows Defender account is integrated with MDR. Contact your Xcitium account manager for support if you have any trouble integrating your cloud account with MDR.


