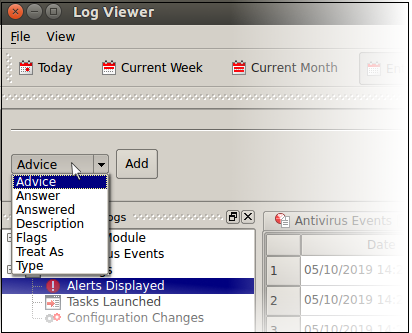
Filter 'Alerts Displayed' Logs
You can create custom views of all logged events according to the following criteria:
- Advice: Filter events by the path at which the malware was found
- Answer: Filter events according to the user's response. For example,'Skip once'.
- Answered: Filter events by specific dates
- Description: Filter events by malware name
- Flags: Not used
- Treat As: Not used
- Alert Type: Filter events by alert category. Currently, 'Antivirus' is the only category available.
Configure Event Filters
- Open Xcitium Client Security
- Click 'More' > 'View Antivirus Events'
- Click the 'More' button to open the log viewer module
- Right-click inside the log viewer module and select 'Advanced Filter'
OR
- Click 'View' on the menu bar and select 'Advanced Filter'
There are 5 types of filter. Each of these can be further refined by selecting or deselecting specific parameters.
- Select a filter criteria and click 'Add'
-
Advice: View logs that concern files at a specific path. You need to enter the path in the field provided:
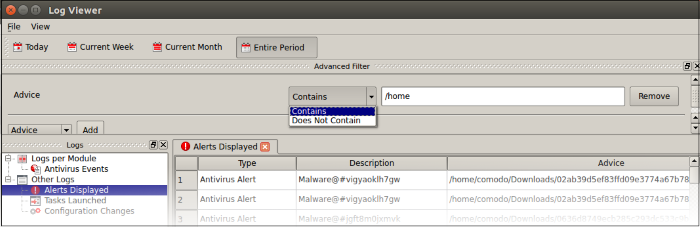
- Select 'Contains' or 'Does Not Contain' option from the drop-down.
- Contains - Show only events which concern items at the location you specify. You can add multiple locations.
- Does Not Contain - Inverts your choice. Show all alerts except those about items in the location you specify.
2. Answer: Filter logs by the action taken by the user at the alert. You can then filter by a specific type of action. For example, show events where the threat was quarantined.
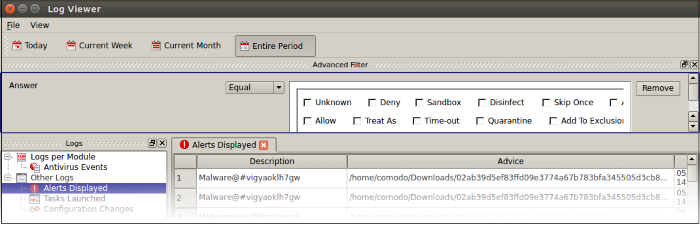
- Select 'Equal' or 'Not Equal' from the
drop-down.
- Equal - Show only events which feature the action you select. You can select multiple actions.
- Not Equal - Inverts your choice. For example, select 'Not Equal' + 'Quarantine' to view every alert except those that where the threat was quarantined.
- Select the action you want to view:
- Unknown - Events where the user did not respond to the alert.
- Quarantine - Events where the user chose to place the threat in quarantine
- Skip Once - Events where the user chose to allow the threat.
- Add to Exclusions - Events where the user created an exception for the threat at the alert.
- Note – Other actions shown in the screen are not applicable.
3. Answered: Filter logs by date of the response. You need to enter the date in the field provided. You can then refine your filter with other parameters:
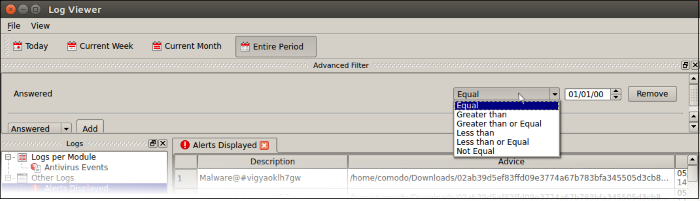
- Select any of the following options in the drop-down:
- Equal – Show only events that occurred on the specified date
- Greater than - Show only events that occurred later than the specified date
- Greater than or Equal – Show only events that occurred on, or after, the specified date
- Less than - Show only events that occurred before the specified date
- Less than or Equal – Show only events that occurred on, or before, the specified date
- Not Equal – Show events that occurred at any time except the specified date
4. Description: Filter logs by the name of the malicious item. You need to enter the name of the malware in the field provided:
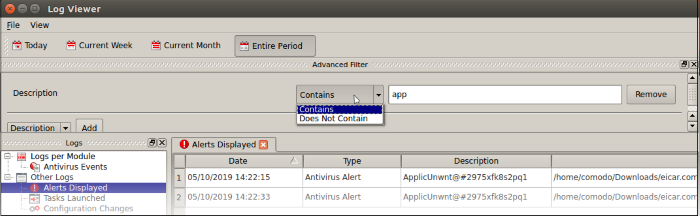
- Select 'Contains' or 'Does Not Contain' from the drop-down:
- Contains – Show only those events which concern the malware named in the text field. You can add multiple malware names.
- Does Not Contain - Show only those events which did not involve the malware named in the text field.
5. Type: Filter events by alert category. Currently, 'Antivirus' is the only category available.
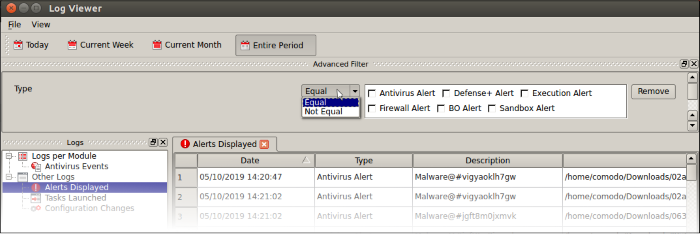
- Select 'Equal' or 'Not Equal' from the drop-down.
- Equal – Show only events which feature the alert type you select.
- Not Equal - Inverts your choice.


