Log Settings
By default, Comodo Internet Security maintains detailed logs of all Antivirus, Firewall and Defense+ events. Logs are also created for 'Alerts Displayed', 'Tasks Launched' and 'Configuration Changes'.
-
This 'Logging' interface allows you to specify whether you want to enable logging; the maximum size of the log file and how CIS should react if the maximum file size is exceeded.
-
Note: If you wish to actually view, manage and export logs, then you need to open the 'View Logs' interface under 'General Settings' (Tasks > General Settings > View Logs)
-
Enable Logging- CIS logs events only if this setting is enabled. (Default = Enabled)
-
If the log file's size exceeds (Mb(s)) - Enables you to specify behavior when the log file reaches a certain size. You can decide on whether to maintain log files of larger sizes or to discard them depending on your future reference needs and the storage capacity of your hard drive.
-
Specify the maximum limit for the log file size (in MB) in the text box beside 'If the log file's size exceeds (MB)' (Default = 20MB).
If you want to discard the log file if it reaches the maximum size, select 'Delete it and create a new one'. Once the log file reaches the specified maximum size, it will be automatically deleted from your system and a new log file will be created with the log of events occurring from that instant (Default = Enabled).
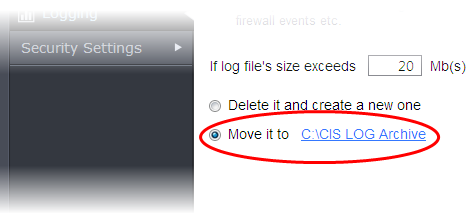
If you want to save the log file even if it reaches the maximum size, select 'Move it to' and select a destination folder for the log file (Default = Disabled).
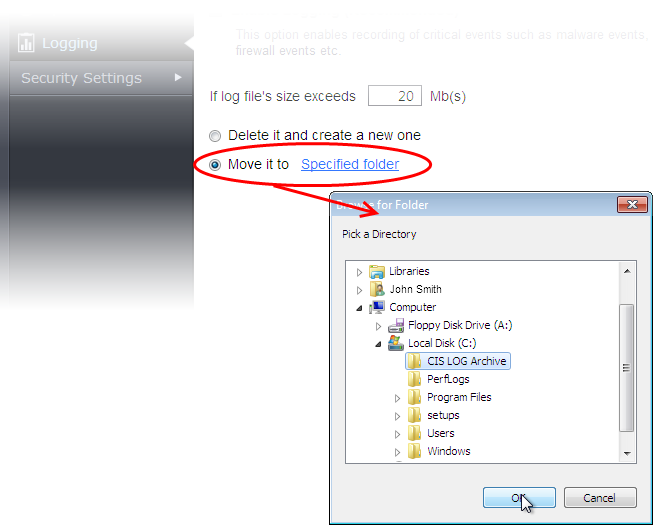
The selected folder path will appear beside 'Move it to'.
Once the log file reaches the maximum size, it will be automatically moved to the selected folder and a new log file will be created with the log of events occurring from that instant.



