File Rating Settings
The file ratings 'Settings' panel allows you to configure the overall behavior of the feature.
- The File Rating Settings panel can be accessed by clicking Security Settings > File Rating > File Rating Settings tab from 'Advanced Settings' interface.
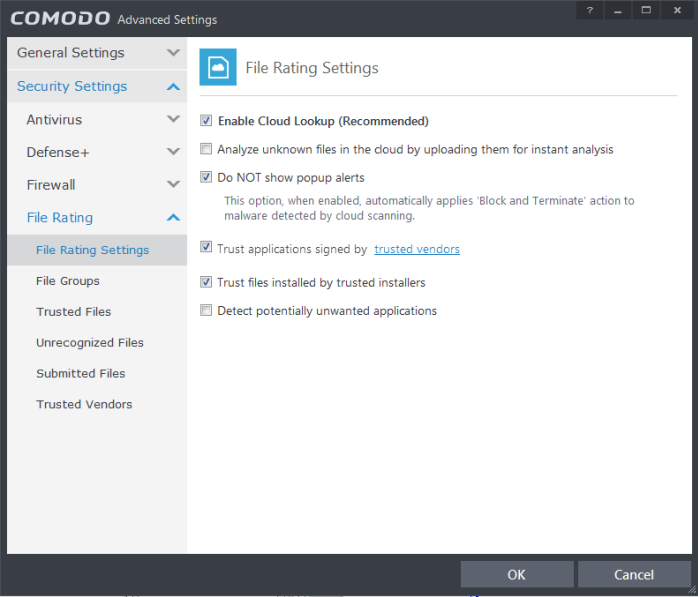
- Enable Cloud Lookup - Allows you to enable or disable File Rating. (Default and recommended =Enabled)
- Analyze unknown files in the cloud by uploading them for instant analysis – Instructs CIS to automatically submit to Comodo those files whose trustworthiness could not be assessed by cloud look-up. Comodo Technicians will analyze the file and add it to future blacklists if found to be malicious. (Default =Enabled)
- DO NOT show popup alerts - This option allows you to configure whether or not to show firewall alerts when malware is encountered. Choosing ‘Do not show popup alerts’ will minimize disturbances but at some loss of user awareness. If you choose not to show popup alerts then you have a choice of default responses that CIS should automatically take – either ‘Block Requests' or 'Allow Requests’. (Default =Enabled)
- Trust applications signed by trusted vendors - Trust applications signed by trusted vendors – If enabled, CIS will award trusted status to executables and files that are code-signed by vendors in the Trusted Vendors list. Click the words 'trusted vendors' to open the Trusted Vendors panel. (Default =Enabled)
- Trust files installed by trusted installers - If enabled, CIS will trust executables and files whose parent applications are listed under the 'Installer or Updater' rule in HIPS Rules or the applications. (Default =Enabled)
- Detect potentially unwanted applications - When this check box is selected, Antivirus scans also scans for applications that (i) a user may or may not be aware is installed on their computer and (ii) may functionality and objectives that are not clear to the user. Example PUA's include adware and browser toolbars. PUA's are often installed as an additional extra when the user is installing an unrelated piece of software. Unlike malware, many PUA's are 'legitimate' pieces of software with their own EULA agreements. However, the 'true' functionality of the software might not have been made clear to the end-user at the time of installation. For example, a browser toolbar may also contain code that tracks a user's activity on the Internet (Default =Enabled).



