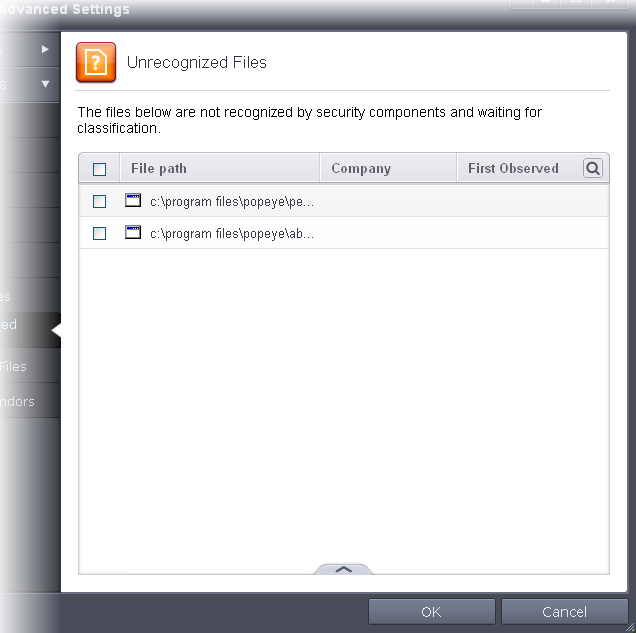
Unrecognized Files
Once installed, the HIPS watches all file system activity on your computer. Every new executable file introduced to the computer, is first scanned against the Comodo certified safe files database. If they are not safe, they are added to the 'Unrecognized Files' for users to review and possibly submit to Comodo. Apart from new executables, any executables that are modified are also moved to the 'Unrecognized Files' area.
'Unrecognized Files' is specifically important while HIPS is in 'Clean PC Mode'. In Clean PC Mode, the files in 'Unrecognized Files' are NOT considered clean. For more information, please check 'Clean PC Mode' on the HIPS settings page.
The files that are moved to Unrecognized Files list either automatically or manually, can be checked for their trustworthiness in two ways:
- Online Lookup - If you are uncertain with the reliability of a file or executable added to the unrecognized file, you can perform an online lookup for the same by contacting Comodo servers. Comodo's master safe list database will be checked for any information available about the executable/file in question and the results will be displayed. Based on the results, you can decide on
- Trusting the file and allowing it to run by adding it to the Trusted Files list,
or
- Block the file by moving it to Blocked Files list.
Refer to the section To perform an online lookup for unrecognized files for more details.
- Submitting file(s) for analysis at Comodo - You can also submit the files moved to Unrecognized File list or the files for which the Online File Look Up did not yield any results for analysis by experts at Comodo. Files submitted will be analyzed thoroughly by experienced technicians at Comodo and will be added to global safe list, if the file is found trustworthy or to global blacklist, if the file appears to be malicious and will be added to the next virus database update. This will benefit all the CIS users worldwide. Refer to the section To manually submit files to Comodo for more details on submitting suspicious files to Comodo.
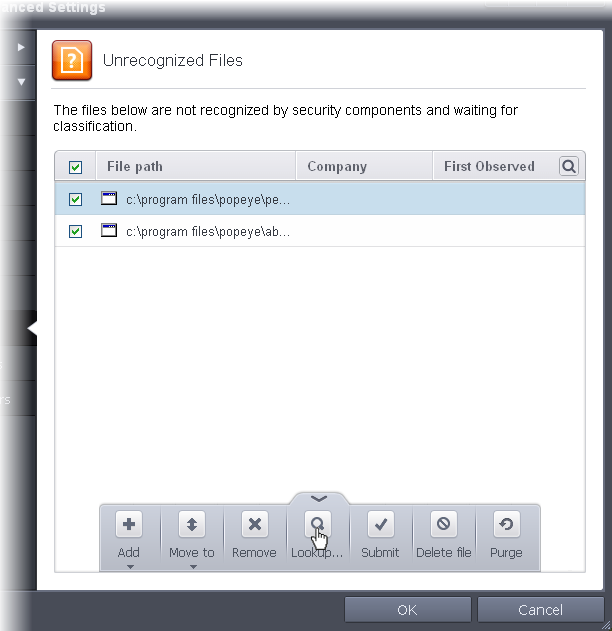
The 'Unrecognized Files' panel displays the list of files added as Unrecognized Files and allows you to assess the pending files to determine whether or not they are to be trusted. If they are trustworthy, they can be moved to 'Trusted Files' using the 'Move to' button. Similarly, files that are suspicious can be moved to the 'Blocked Files' area.
You can also add files upon which you are suspicious into 'Unrecognized Files' list to check whether the master Comodo safe list contains more information on them or to submit the files to Comodo for analysis. Experts at Comodo will analyze the files and add them to global white-list or black-list accordingly.
- The Unrecognized Files panel can be accessed by clicking Security Settings > File Rating > Unrecognized Files tab from the Advanced Tasks interface
You can use
the search option to find a specific item in the list by clicking the
search icon at the far right in the column
header.
at the far right in the column
header.
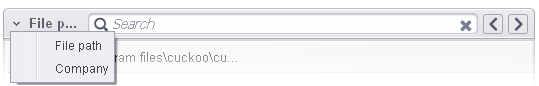
- Click the chevron on the left side of the column header and select the search criteria from the drop-down.
- Enter partly or fully the name of the item as per the selected criteria in the search field.
- Click the right or left arrow at the far right of the column header to begin the search.
- Click
the
 icon in the search field to close the search option.
icon in the search field to close the search option.
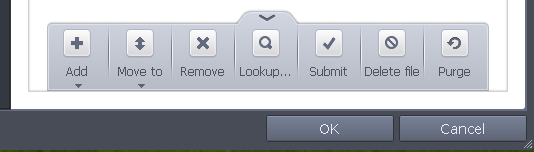
- Add - Allows you to add files to 'Unrecognized Files' list manually
- Move - Allows you to move files from 'Unrecognized Files' list to Trusted Files or Blocked Files list
- Remove - Allows you to remove files from 'Unrecognized Files' list
- Lookup - Starts the online lookup of selected file with the master Comodo safelist if any details are available
- Submit - Begins the file submission process.
- Delete file - Deletes the highlighted file from your computer
- Purge - Runs a system check to verify that all the files listed are actually installed on the host machine at the path specified. If not, the file is removed, or 'purged', from the list.
To manually add files to 'Unrecognized Files' list
-
Click the handle from the bottom center and choose 'Add'
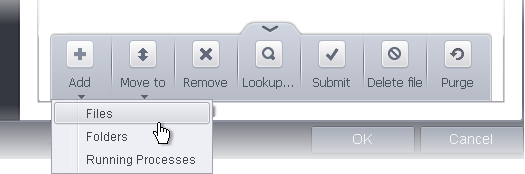
You can add files to the Unrecognized Files list by three ways:
- Files - Allows you to navigate to the file or executable of the program you wish to add.
- Folders - Allows you to navigate to the folder you wish to add. All the files in the folder will be added to the 'Unrecognized Files' list.
- Running Processes - Allows you to select a currently running process. On selecting a process, the parent application, which invoked the process will be added to 'Unrecognized Files' list.
- Click OK for your changes to take effect.
To move an included entry to Trusted Files or Blocked Files
- Select the entry to be transferred out of the 'Unrecognized Files' list into either Trusted Files or Blocked Files. You can select several entries to be moved at once by marking the check-boxes beside the entries.
- Click the handle from the bottom center and choose 'Move'
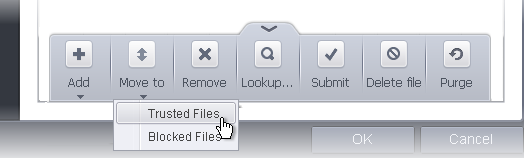
- Choose 'Trusted Files' or 'Blocked Files' from the drop-down.
- Click OK for your changes to take effect.
To remove an included entry from the Unrecognized Files list
- Select the entry to be removed from the 'Unrecognized Files' list. You can select several entries to be removed at once by marking the check-boxes beside the entries.
- Click the handle from the bottom center and choose 'Remove'. The file is only removed from the list and not deleted from your system.
- Click OK for your changes to take effect.
To perform an online lookup for unrecognized files
- Select the file to be checked from the 'Unrecognized Files' list. You can select several entries at once by marking the check-boxes beside the entries.
- Click the handle from the bottom center and choose 'Lookup...'.
Comodo servers will be contacted immediately to conduct a search of Comodo's master safe list database to check if any information is available about the files in question and the results will be displayed.
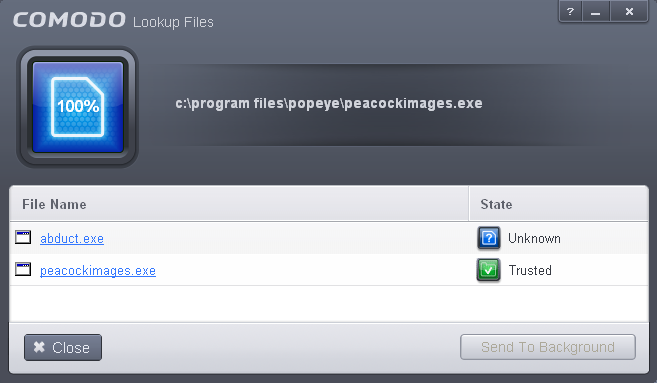
-
If a file is found to be malicious, it will be indicated as 'Bad' with a red icon. You can move it to Blocked Files.
-
If the file is found to be safe, it will be indicated as 'Trusted' with a green icon. You can move it to Trusted Files.
-
If no information is available, it will be indicated as 'Unknown' with a yellow icon. You can submit the file to Comodo for analysis.
To manually submit the files to Comodo
-
Select the entry to be submitted from the 'Unrecognized Files' list. You can select several entries to be sent at once by marking the check-boxes beside the entries.
-
Click the handle from the bottom center and choose 'Submit'. The file(s) will be immediately sent to Comodo.
You can view the list of files you submitted so far, from the Submitted Files panel.



