CIS Premium – Installation
| Note - Before beginning installation, please ensure you have uninstalled any other antivirus and firewall products that are on your computer. Click here to read the full note. |
In order to install Comodo Internet Security - Premium, you need to download the setup file from http://www.comodo.com/home/download/download.php?prod=cis.
- Choose whether you want the 32 or 64 bit version of CIS then click 'download'
- If you are unsure which version you need, select the 32/64-bit Windows Installer. This executable contains BOTH 32 and 64 bit installers. The setup routine will automatically detect which version of Windows you have and install the appropriate version. Please note, the Universal Windows Installer is a much larger download than the individual 32 or 64 bit setup files.
After downloading the required
Comodo Internet Security setup file to your local hard drive, double
click on it ![]() to start the installation wizard.
to start the installation wizard.
Step 1 - Choosing the Interface Language
The installation wizard starts automatically and the 'Select the language' dialog is displayed. Comodo Internet Security is available in several languages.
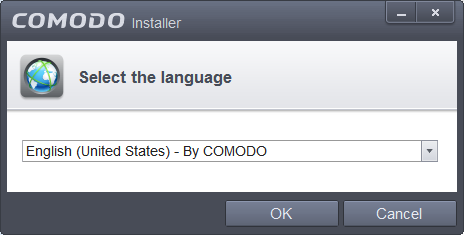
-
Select the language in which you want Comodo Internet Security to be installed from the drop-down menu and click 'OK'.
Step 2 - Installation Configuration
The installation configuration screen will be displayed.

- If you click 'Customize Installer' then you can choose advanced options. These include which CIS components you wish to install, the ability to choose CIS installation path and other advanced CIS configuration settings.
Receive Comodo News and Notifications
Comodo Internet Security Premium is activated free of cost for lifetime usage. If you wish to sign up for news about Comodo products then enter your email address in the space provided. This is optional.
Cloud Based Behavior Analysis
Any file that is identified as unrecognized is sent to the Comodo Instant Malware Analysis (CIMA) server for behavior analysis. Each file is executed in a virtual environment on Comodo servers and tested to determine whether it it behaves in a malicious manner. If yes, the file is then manually analyzed by Comodo technicians to confirm whether it is a malicious file or not. The results will be sent back to your computer in around 15 minutes. Comodo recommends users leave this setting enabled. Read the privacy policy by clicking the 'Privacy Policy' link.
Browser Homepage
Leaving this setting enabled will:
- Set your home page, search engine and browser's new tab to Yahoo (all supported browsers)
- Currently supported browsers are Mozilla Firefox, Google Chrome, Internet Explorer, Comodo Dragon, Comodo Ice Dragon, Chromodo and Opera.
- Make Yahoo your default search engine. This means:
- When you enter a search item into the address bar of a supported browser, the search will be carried out by Yahoo
- A ‘Search with Yahoo’ menu entry will be added to the right-click menu of supported browsers.
- Yahoo will be set as the default search engine in the ‘Search’ box of supported browsers
- The instant ‘search suggestions’ that you see when you start typing a search item will be provided by Yahoo.
Send Program Usage Data
If enabled, CIS will periodically send anonymous data to Comodo about the way you use the product over a secure and encrypted channel. This helps our team learn more about how our users interact with our products and so helps us implement improvements which meet with user requirements. Disable this option if you do not want usage details to be sent to Comodo. Comodo recommends users leave this setting enabled. You can change this setting from Advanced Settings > General Settings > Log Settings interface, at any time after installation.
- Please review and/or modify the settings in
the dialog.
End User License Agreements
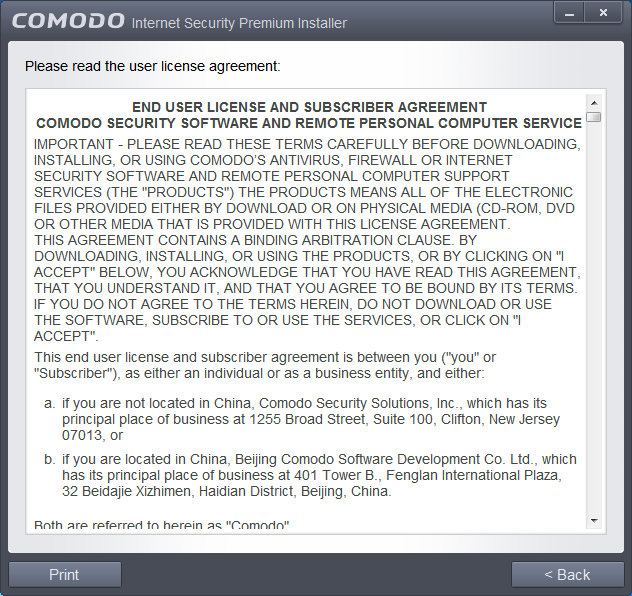
After reading the agreements, click the 'Back' button to return to the installation configuration screen.
Once back at the main installer screen, if you wish to configure advanced options, click 'Customize Installation'. Otherwise, click 'Agree and Install' to begin installation.
Customizing Installation
Clicking the 'Customize Installation' link opens an advanced options interface that enables you to choose which elements you would like to install, configure security popup alerts and choose the installation path. In order to obtain maximum protection, Comodo recommends that you uninstall any third party personal Firewall and Antivirus in your system and select all the components to get the full benefit of the product.
Select Components to Install (Click to go back to Step 2)
Click the 'Installation Options' tab to select the components to be installed.
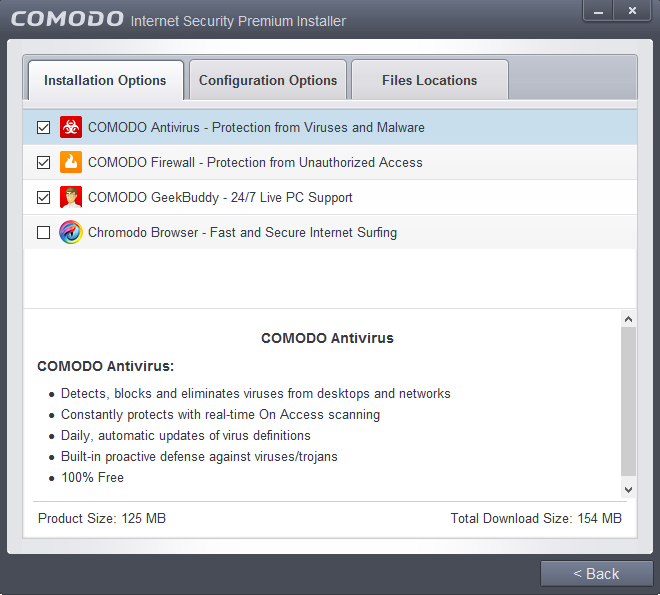
- Install COMODO Firewall - Selecting this option installs Comodo Firewall and Defense+ components. Deselect this option, if you already have third party Firewall protection activated in your computer system. Comodo Firewall installation is mandatory to qualify for the virus free guarantee.
- Install COMODO Antivirus - Selecting this option installs Comodo Antivirus and Defense+ components. Deselect this option, if you already have a third party virus protection activated in your computer system. Comodo Antivirus installation is mandatory to qualify for the virus free guarantee.
- Install COMODO GeekBuddy - Selecting this option installs GeekBuddy, a 24 x 7 remote support service in which Comodo experts can help you solve any computer related problems you may encounter. Refer to the section Comodo GeekBuddy for more details.
- Install Chromodo Web Browser - Selecting this option
installs Chromodo, a fast and versatile Internet browser based
on Chromium technology and infused with Comodo's unparalleled level
of security. Refer to the section Chromodo for more details.
Configuration Options
- Click the 'Configuration Options' tab to configure pop-up alert options.
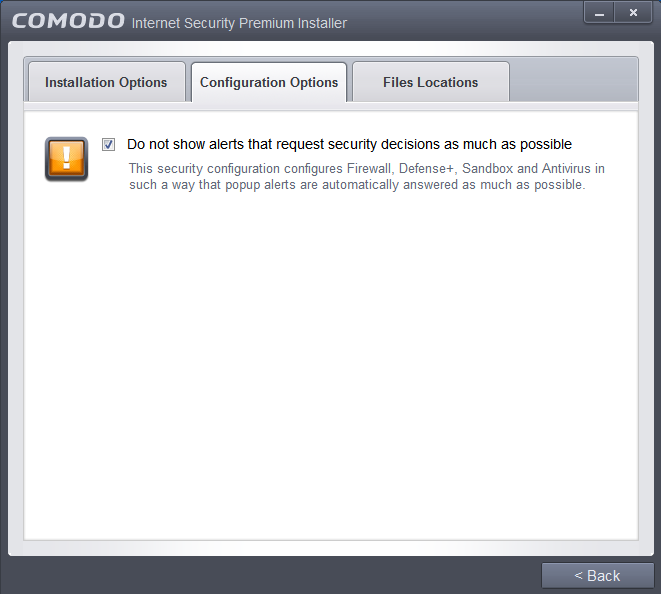
- Do Not show alerts that request security decisions as much as possible - When this option is selected, CIS is configured to automatically deal with most issues in a secure manner without raising a popup alert - thus minimizing user intervention. Most users should leave this option at the default state of enabled. Advanced users wishing to gain greater insight into CIS actions and/or to have more control over security decisions may wish to disable this option.
Choosing Installation Location
Click the 'Files Locations' tab to choose the installation path.
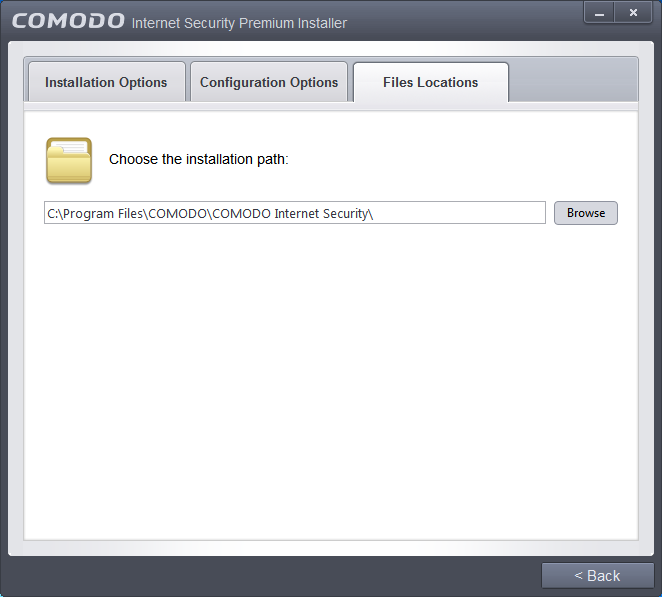
This screen allows you to select
the folder in your hard drive for installing Comodo Internet
Security. The default path is C:/Program Files/COMODO/COMODO Internet
Security. If you want to install the application in a location other
than the default location, click 'Browse' to choose a different
location.
After customizing your installation, click the 'Back' button to return to the installation configuration screen.
-
Once you are satisfied with your settings, click 'Agree and Install' to begin installation (Click to go back to Step 2).
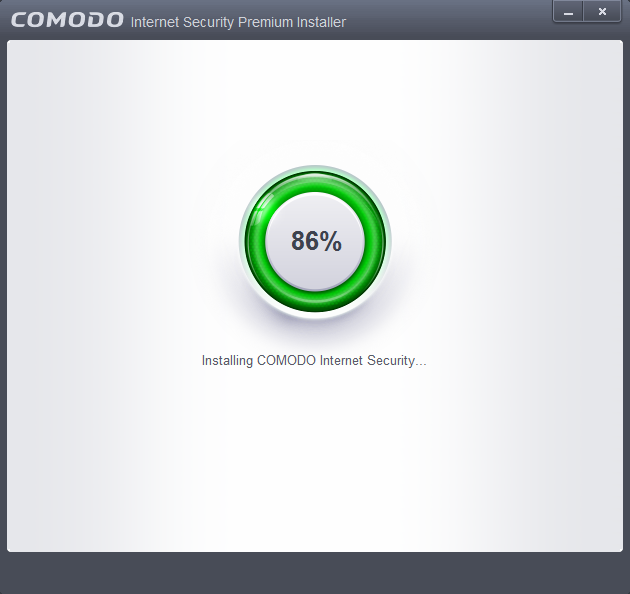
Step 3 - Installation Progress
The installation progress will be displayed...
...and on completion, the successfully completed dialog will be displayed.
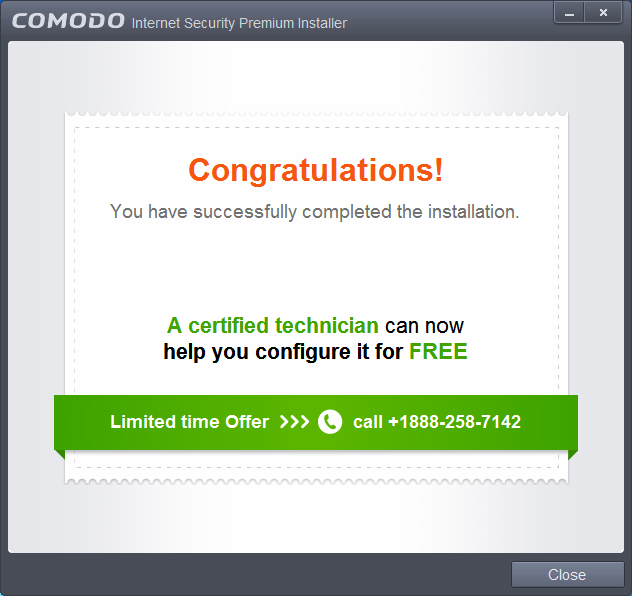
- Click the 'Close' button.
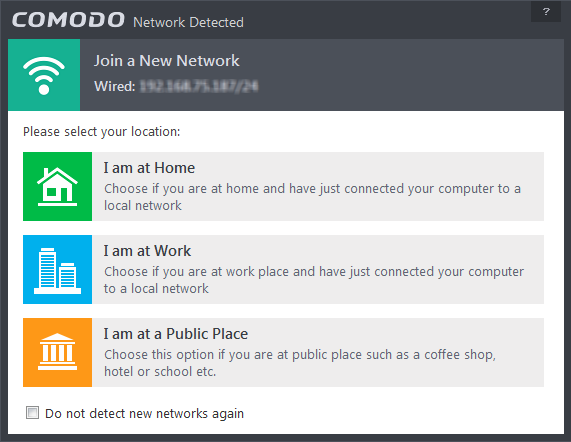
- Select your location from the three options above
- Select 'Do not automatically detect new networks' If you are an experienced user that wishes to manually set-up their own trusted networks (this can be done in 'Network Zones' and through the 'Stealth Ports Wizard')
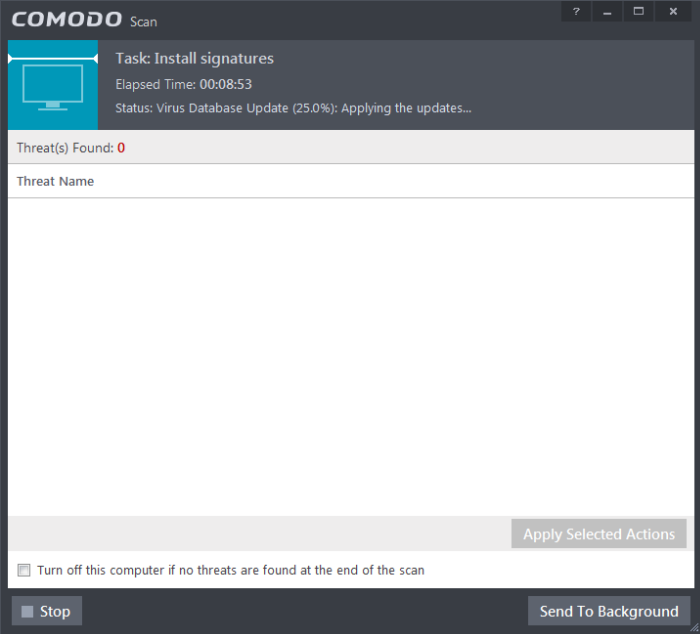
You can also send this task to the background by pressing the 'Send to Background' button and retrieve it in the 'Task Manager' interface. Refer to the section 'Manage CIS Tasks' for more details.
CIS will commence a Quick Scan of system memory, autorun entries, hidden services, boot sectors and other critical areas automatically after the virus database has been updated.
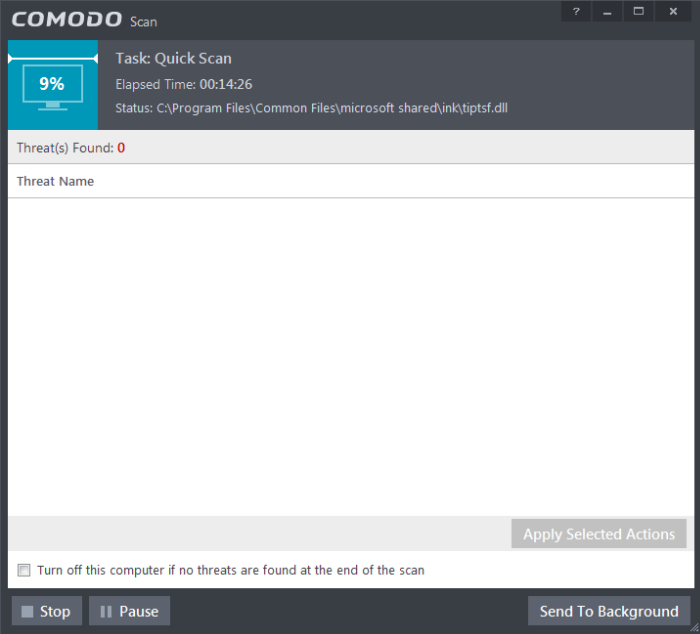
If you do not want the scan to continue at this time, click the 'Stop' button.
After the scanning is complete, and any threats are found, an alert screen will be displayed. The alert will display the number of threats/infections discovered by the scanning and provide you the options for cleaning.
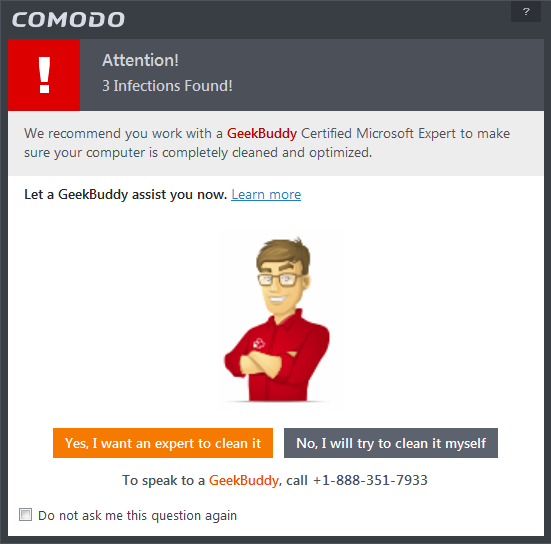
- If you wish to have a skilled professional from Comodo to access your system and perform an efficient disinfection, click 'Yes, I want an expert to clean it'. If you are a first-time user, you will be taken to Comodo GeekBuddy webpage to sign-up for a GeekBuddy subscription. If you have already signed-up for GeekBuddy services, the GeekBuddy chat session will start and a skilled technician will offer to clean your system.
For more details on GeekBuddy, refer to the section Comodo GeekBuddy.
-
If you wish to clean the infections yourself, select 'No, I will try to clean it myself'. The scan results screen will be displayed. The results will contain a list of files identified with threats or infections (Viruses, Rootkits, Malware and so on) and provide you the options for cleaning. An example results screen is shown below:
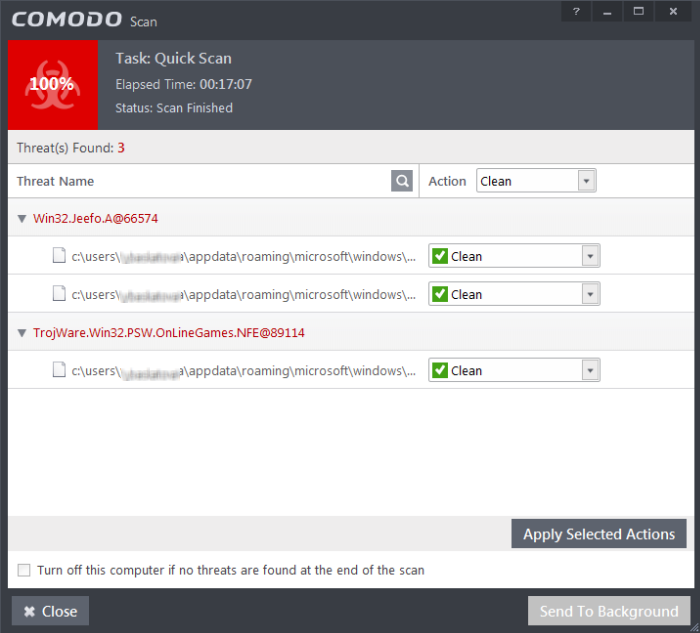
If any threats are detected, they will be displayed and you can choose to take appropriate action from any of the drop-down fields in the screen and click 'Apply Selected Actions' button. Refer to the section 'Processing Infected Files ' for more details.
Step 4 - Restarting Your System
In order for the installation to take effect, your computer needs to be restarted.
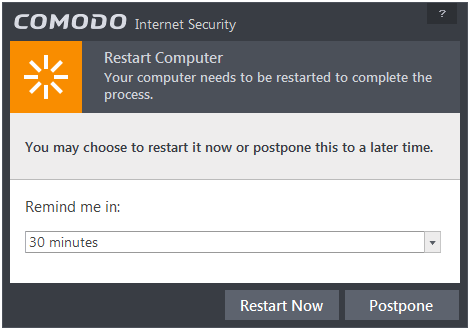
- If your want to restart the computer immediately, save all your work and click 'Restart Now'.
- If you
want to restart the computer at a later time, select when you need
to be reminded from the drop-down and click 'Postpone'.
Step 5 - After Restarting Your System
After restarting, a 'Welcome' screen will appear. This contains a summary of the components you chose to install as well as some friendly advice.

This screen will appear every time
you start your system. If you do not want the screen to be displayed
on every start up, select the check box 'Do not show this window
again' before closing the window.
The CIS Widget will be displayed: