Scan Profiles
The Scan Profiles area allows you to view, edit, create and run custom virus scans. Each profile is a collection of scanner settings that tell CIS:
- Where to scan (which files, folders or drives should be covered by the scan)
- When to scan (you have the option to specify a schedule)
- How to scan (options that let you specify the behavior of the scan engine when running this profile)
To open the panel
-
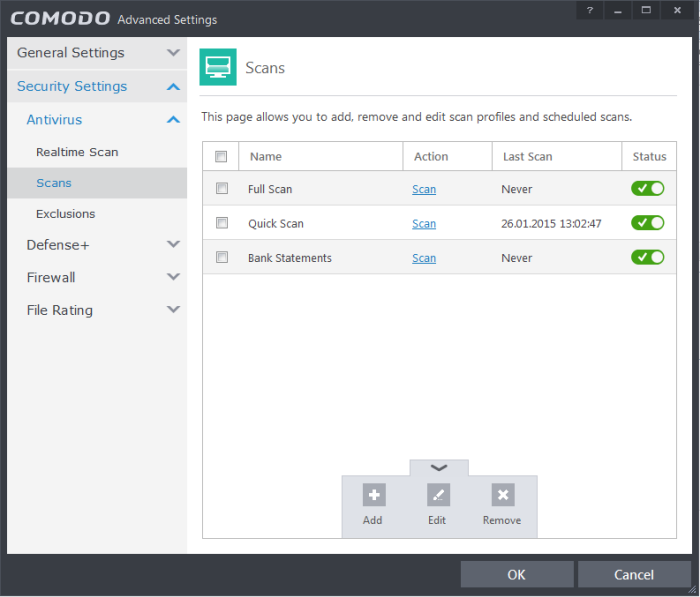
Click Security Settings > Antivirus > 'Scans' tab in the 'Advanced Settings' panel
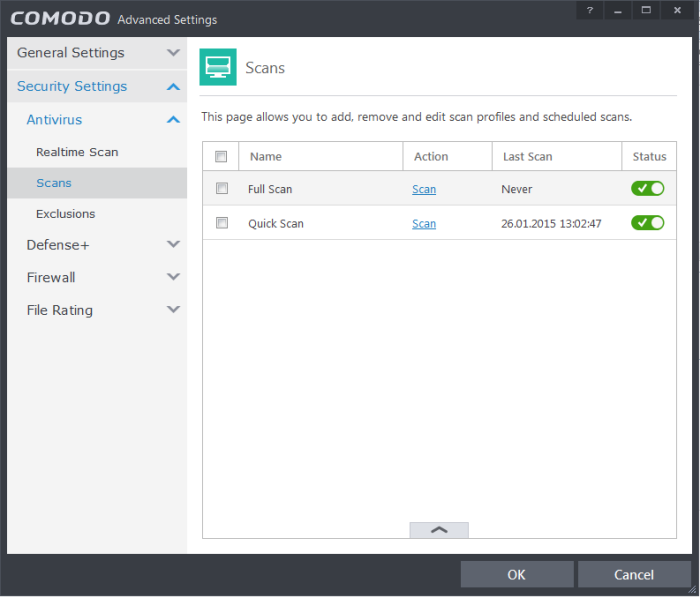
CIS ships with two predefined scan profiles:
- Full Scan - This profile covers every local drive, folder and file on your system.
- Quick Scan - Covers critical areas in your system which are highly prone to infection from viruses, rootkits and other malware. This includes system memory, auto-run entries, hidden services, boot sectors, important registry keys and system files. These areas are responsible for the stability of your computer and keeping them clean is essential.
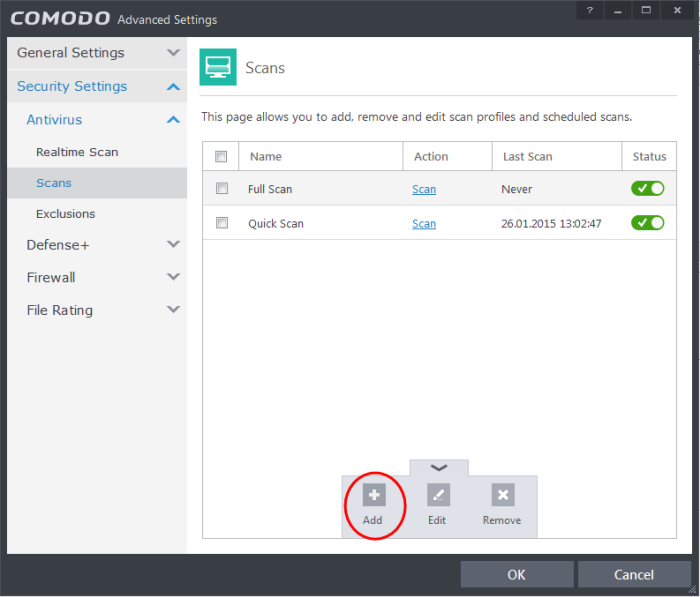
You can run a profile-scan immediately by clicking the 'Scan' link alongside it.Click the handle at the foot of the interface if you wish to edit, remove or add a profile.
Click the following links for more details on:
- Click the handle at the bottom of the interface then click the 'Add' button
The scan profile interface will be displayed.
- Type a name for the profile in the 'Scan Name' text box
- Click the handle at the bottom of the interface to select items that should be included in the profile
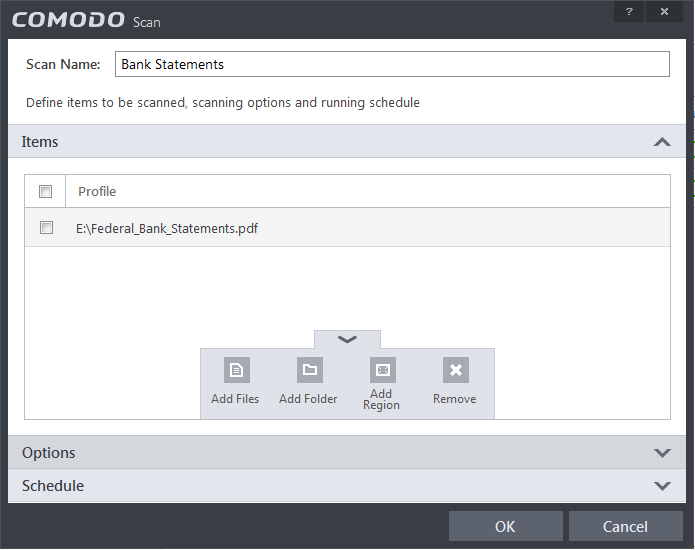
- Add Files - Allows you to navigate to specific files that you wish to add to the profile
- Add Folder - Opens the 'Browse For Folder' window and allows you to select entire folders
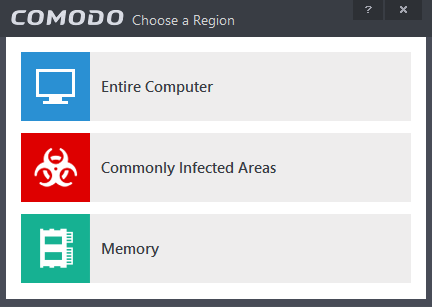
- Add Region - Allows you to add predefined regions to the profile. For example, 'Full Computer', 'Commonly Infected Areas' and 'System Memory'.
- Repeat the process to add more items into the profile
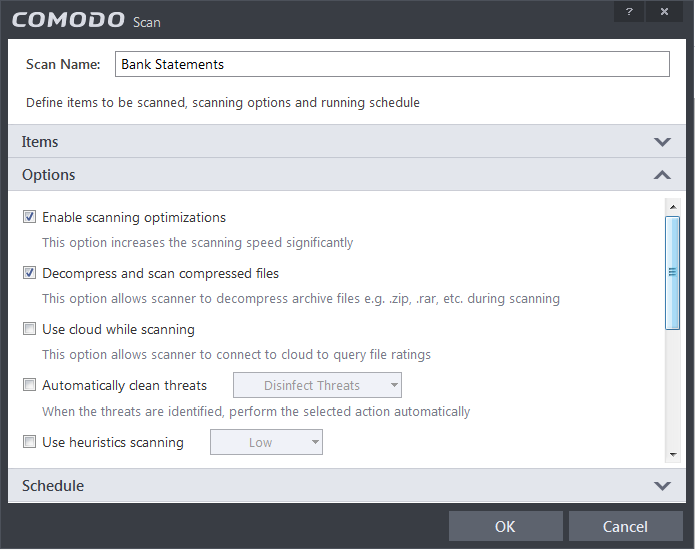
- Options:
- Enable scanning optimizations – On selecting this option, the antivirus will employ various optimization techniques like running the scan in the background in order to speed-up the scanning process (Default = Enabled).
- Decompress and scan compressed files - When this check box is selected, the Antivirus scans archive files such as .ZIP and .RAR files. Supported formats include RAR, WinRAR, ZIP, WinZIP ARJ, WinARJ and CAB archives (Default = Enabled).
- Use cloud while scanning - Selecting this option enables the Antivirus to detect the very latest viruses more accurately because the local scan is augmented with a real-time look-up of Comodo's online signature database. With Cloud Scanning enabled your system is capable of detecting zero-day malware even if your local antivirus database is out-dated. (Default = Disabled).
- Automatically clean threats – Enables you to select the action to be taken against the detected threats and infected files automatically. Choices available are to disinfect the threats and moving the threats to quarantine.
- Use heuristics scanning – Enables you to select whether or not Heuristic techniques should be applied on scans in this profile. You are also given the opportunity to define the heuristics scan level (Default = Enabled).
Background Info: Comodo Internet Security employs various heuristic techniques to identify previously unknown viruses and Trojans. 'Heuristics' describes the method of analyzing the code of a file to ascertain whether it contains code patterns similar to those in known viruses. If it is found to do so then the application deletes the file or recommends it for quarantine. Heuristics is about detecting 'virus-like' traits or attributes rather than looking for a precise virus signature that matches a signature on the virus blacklist.This allows CIS to 'predict' the existence of new viruses - even if it is not contained in the current virus database.
- Low- Lowest' sensitivity to detecting unknown threats but will also generate the fewest false positives. This setting combines an extremely high level of security and protection with a low rate of false positives. Comodo recommends this setting for most users. (Default)
- Medium - Detects unknown threats with greater sensitivity than the 'Low' setting but with a corresponding rise in the possibility of false positives.
- High - Highest sensitivity to detecting unknown threats but this also raises the possibility of more false positives too.
- Limit maximum file size to – Select this option if you want to impose size restrictions on files being scanned. Files of size larger than that specified here, are not scanned, if this option is selected (Default = 40 MB).
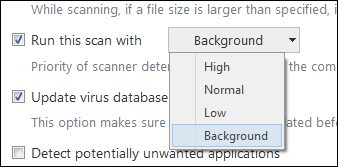
- Run Scan with – Enables you to set the priority of the scanning from High to Low and to run at background (Default = Disabled).
- Update virus database before running – Selecting this option makes CIS to check for virus database updates and if available, update the database before commencing the scan (Default = Enabled).
- Detect potentially unwanted applications -When this check box is selected, virus scans will also check for potentially unwanted applications (PUA's). This is software that (i) a user may or may not be aware is installed on their computer and (ii) may have functionality and objectives that are not clear to the user. Example PUA's include adware and browser toolbars. PUA's are often installed as an additional extra when the user is installing an unrelated piece of software. Unlike malware, many PUA's are 'legitimate' pieces of software with their own EULA agreements. However, the 'true' functionality of the software might not have been made clear to the end-user at the time of installation. For example, a browser toolbar may also contain code that tracks a user's activity on the internet (Default = Enabled).
- If you want the scan to be performed periodically, set a Schedule for the custom scan by clicking 'Schedule'.
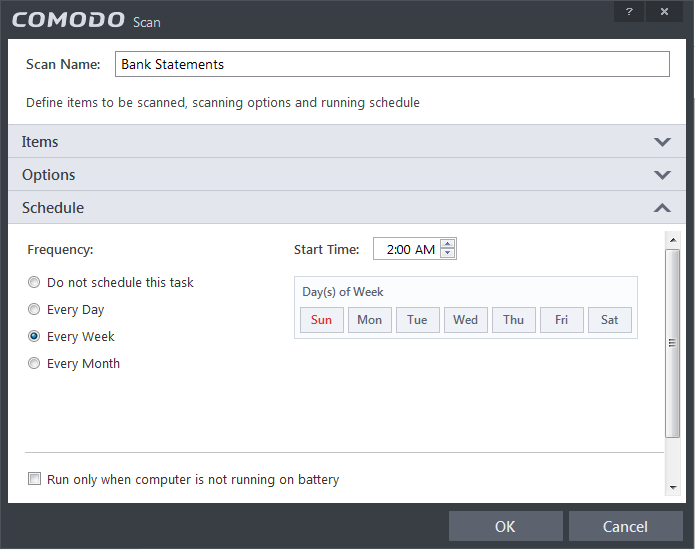
- Do not schedule this task – The scan profile will be created but will not be run automatically. The profile will be available for manual on-demand scanning.
- Every Day –Runs the scan every day at the time specified.
- Every Week - Scans the areas defined in the scan profile on the day(s) of the week specified in 'Days of the Week' field and the time specified in the 'Start Time' field. You can select the days of the week by directly clicking on them.
- Every Month - Scans the areas defined in the scan profile on the day(s) of the month specified in 'Days of the month' field and the time specified in the 'Start Time' field. You can select the days of the month by directly clicking on them.
- Run only when computer is not running on battery - This option is useful when you are using a laptop or any other battery driven portable computer. Selecting this option runs the scan only if the computer runs with the adapter connected to mains supply and not on battery.
- Run only when computer is IDLE - Select this option if you do not want to be disturbed when involved in computer related activities. The scheduled scan will run only if the computer is in idle state.
- Turn off computer if no threats are found at the end of the scan - Selecting this option turns your computer off, if no threats are found during the scan. This is useful when you are scheduling the scans to run at nights.
-
Click 'OK' to save the profile.
| Note: The scheduled scan will run only if it is enabled. Click the button under the 'Status' column beside the respective profile to toggle between on and off statuses. |
To run a custom scan as per scan profile
- Click Scan from the 'General Tasks' interface and Click 'Custom Scan' from the 'Scan' interface.
- Click 'More Scan Options' from the 'Custom Scan' pane.
- The 'Advanced Settings' interface will be displayed with 'Scans' panel opened.
- Click Scan beside the required scan profile.
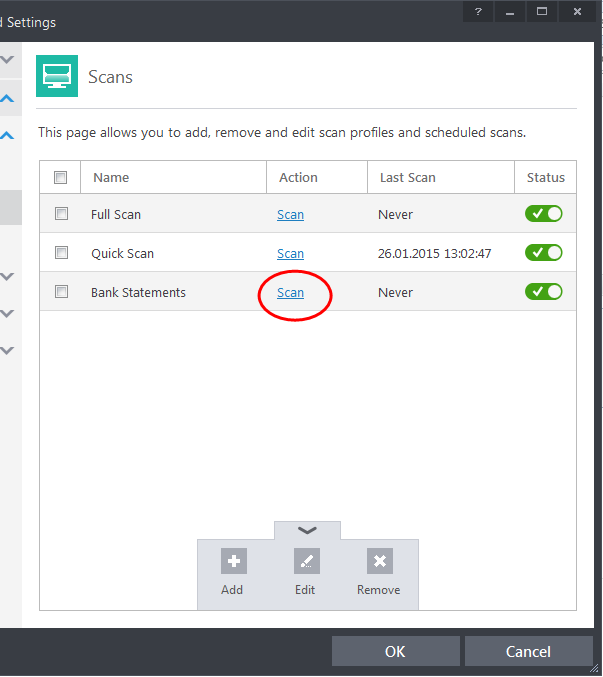
- The scan will be started and on completion the results will be displayed.
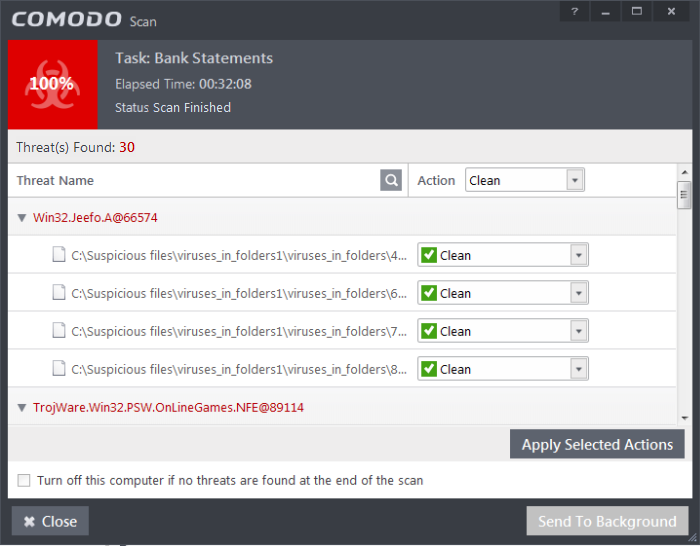
You can choose to clean, move to quarantine or ignore the threat based on your assessment. Refer to Processing the infected files for more details.



