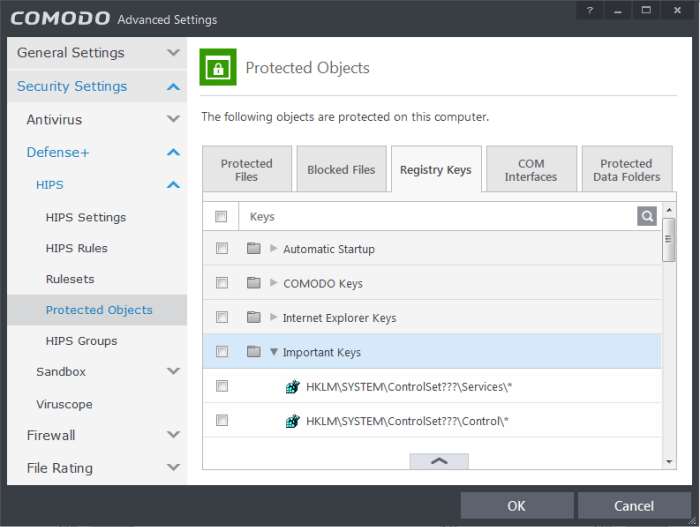
Protected Registry Keys
The 'Registry Protection' panel allows you to protect system critical registry keys against modification. Irreversible damage can be caused to your system if important registry keys are corrupted or modified in any way. It is essential that your registry keys are protected against any type of attack.
Click the 'Registry Keys' tab in the Protected Objects interface.
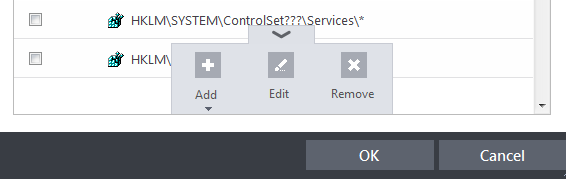
Clicking the handle at the bottom of the interface opens an options panel with the following options:
-
Add – Allows you to add Registry groups or individual registry keys/entries to Registry Protection list.
-
Edit – Allows you to edit the path of the Registry group or individual registry keys/entries of the selected item in the Registry Protection interface.
-
Remove - Deletes the currently highlighted Registry group or individual registry key from the Registry Protection list.
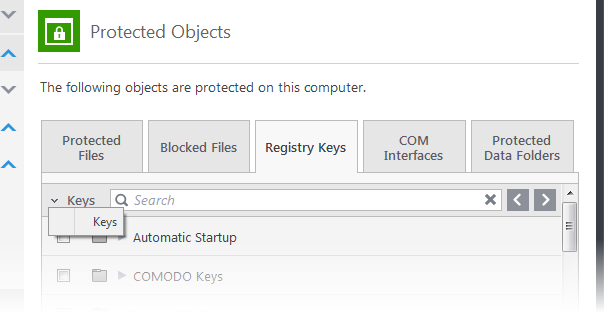
To manually add an individual Registry key or Registry Group
-
Click the handle from the bottom and select 'Add'.
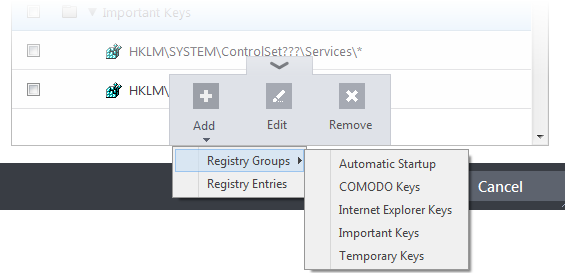
You can add the items by following methods:
-
Adding Registry Groups – Selecting Registry Groups allows you to batch select and import predefined groups of important registry keys. Comodo Internet Security provides a default selection of 'Automatic Startup' (keys), 'Comodo Keys', 'Internet Explorer Keys', 'Important Keys' and 'Temporary Keys'. For explanations on editing existing registry groups and creating new groups refer to Registry Groups in HIPS Groups section.
- Adding individual Registry Keys - Selecting 'Registry Entries' opens the 'Select Registry Keys'.
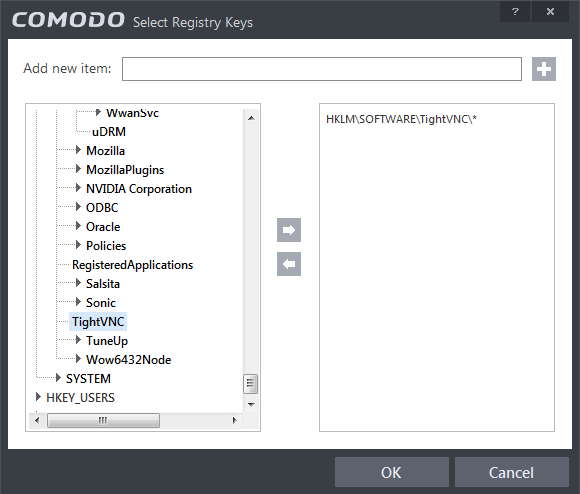
You can add items by browsing the registry tree in the left hand side pane, selecting the key and moving it to right hand side pane by clicking the right arrow button. To add item manually enter its name in the 'Add new item' field and press the '+' button.
To edit an item in the Registry Protection list
-
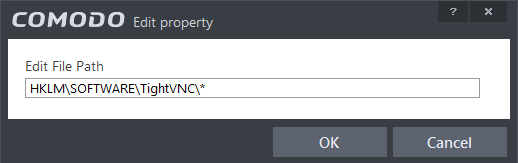
Select the key from the list, click the handle from the bottom and select Edit. The 'Edit Property' dialog will appear.
-
Edit the key path, if you have relocated the key and click OK.
|
Note: The Registry
Groups cannot be edited from this interface. You can edit Registry
Groups from the Manage Registry Groups interface. Refer toRegistry
Groups in HIPS
Groups section. |
To delete an item from Registry Protection list
-
Select the item from the list, click the handle from the bottom and select 'Remove'.
The selected item will be deleted from the Registry Protection list. CIS will not generate alerts, if the key or the group is modified by other programs.



