Blocked Zones
A computer network enables users to share information and devices between computers and other users within the network. Obviously, there are certain computer networks that you need to 'trust' and grant access to - for example your home or work network. Unfortunately, there may be other, untrustworthy networks that you want to restrict communication with - or even block entirely.
|
Note: We advise new or inexperienced users to first read 'Network Zones' , 'Stealth Ports Wizard' and 'Network Security Policy' before blocking zones using this interface. |
The 'Blocked Network Zones' area allows you to:
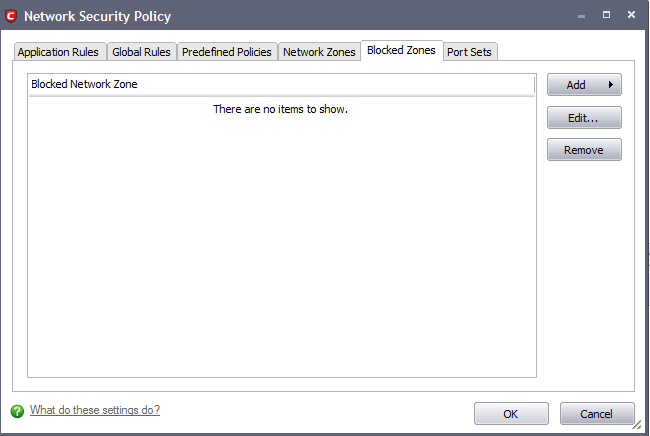
To access the Blocked Zones interface
-
Click 'Blocked Zones' tab from Firewall Tasks > Network Security Policy interface.
|
Note 1: You must create a zone before you can block it. There are two ways to do this;
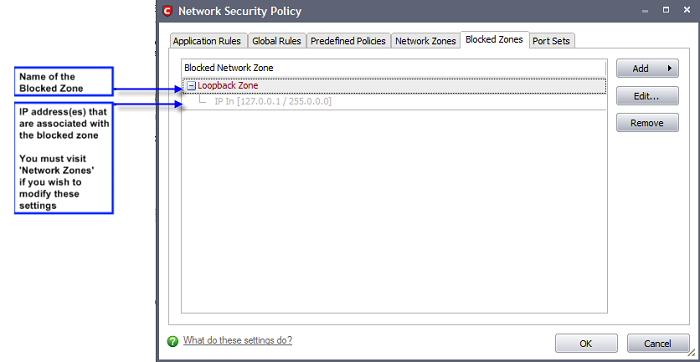
Note 2: You cannot reconfigure pre-existing network zones from this interface. (e.g., to add or modify IP addresses). You need to use 'Network Zones' if you want to change the settings of existing zones. |
To deny access to a specific network by selecting a pre-existing network zone and designating it as blocked
-
Click the 'Add' button at the top right and select 'Network Zones' then the particular zone you wish to block.
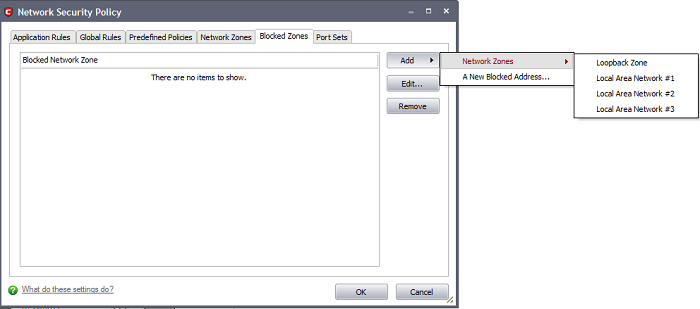
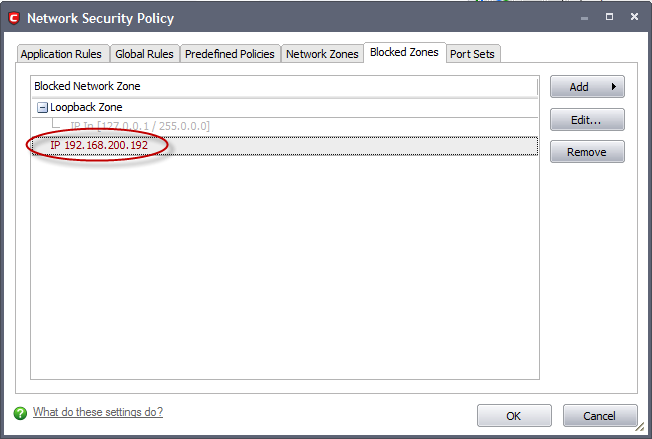
The selected zone appears in the main interface.
-
Click 'Apply' to confirm your choice. All traffic intended for and originating from computer or devices in this zone are now blocked.
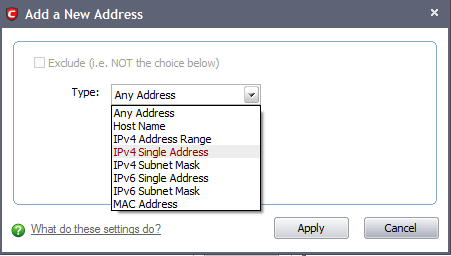
To deny access to a specific network by manually defining a new blocked zone
-
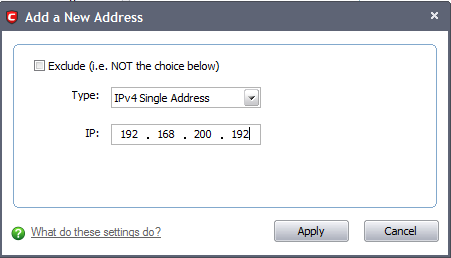
Click the 'Add' button at the top right and select 'A New Blocked Address' (Default = Any Address). The Exclude check box will be enabled only if any other choice is selected from the drop-down box. This launches the following dialog where you can select the IP address(es), IP Subnet Masks, Host Name or MAC address that you wish to block from the Type drop-down box.
-
Enter the IP address that you wish to block.
After clicking 'Apply' to confirm your choice, the address(es) you blocked appears in the main interface. You can modify these addresses at any time by selecting the entry and clicking 'Edit'.
-
Click 'OK' to confirm your choice. All traffic intended for and originating from computer or devices in this zone are now blocked.
|
Special Note: Creating a blocked network zone implements a 'block all' global rule for the zone in question. However, unlike when you create a 'Trusted Zone', this rule is not displayed or editable from the global rules tab of the Network Security Policy interface. This is because you are likely to be trusting only a few zones, there is the potential that you may have to block many. The constant addition of such block rules would make the interface unmanageable for most users. |
Comodo Internet Security User Guide | © 2012 Comodo Security Solutions Inc. | All rights reserved



