Control External
Device Accessibility
- Click 'Settings' > 'Advanced Protection' > 'Device Control'.
- XCS helps you block access to selected external devices attempting to connect to your computer.
- The
'Device Control' panel lets you specify types of external devices
that are to be blocked and define exclusions to it.
Block an external device
1. Click 'Settings' on the XCS home screen
2. Click the 'Advanced Protection' > 'Device Control'
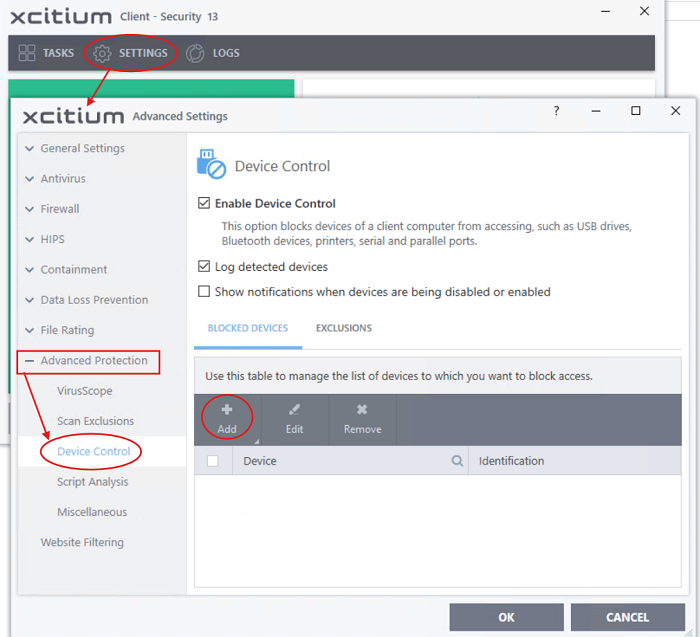
- Enable Device Control - Activate the device control functionality to selectively prohibit access to external devices. You should specify devices to be banned in the 'Blocked Devices' pane. (Default = Enabled)
- Blocked Devices - List of external device classes which are not allowed to connect to the endpoint. Example classes include 'USB Storage Devices', 'CD/DVD Drives', 'BlueTooth Devices' and 'Firewire Devices'.
- Exclusions - Add exceptions to a blocked class. For example, if you wish block the class 'USB Devices' but wish to allow access for your company's authentication tokens, then you should add those USB tokens as exceptions.


