View Active Process List
The 'Active Process List' interface displays all currently active processes that are running on your PC and the parent applications of those processes. By tracing an application's parent process, the 'Sandbox' can detect whether a non-trusted application is attempting to spawn a trusted application and thus deny access rights for that trusted application. This system provides the very highest protection against Trojans, malware and rootkits that try to use trusted software to launch an attack.
The interface also allows you to perform an online lookup on a process, submit an application to Comodo for analysis, kill unwanted processes and more.
To view Active Process list
- Open the General Tasks interface and click 'View Active Processes'.
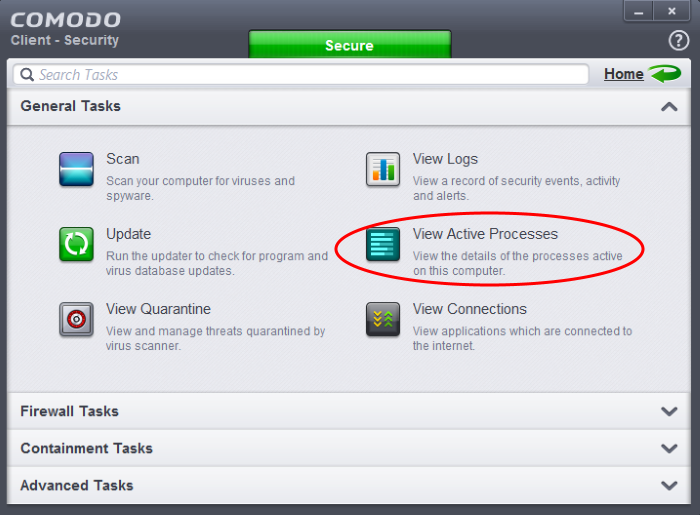
The 'Active Processes List' screen will be displayed.
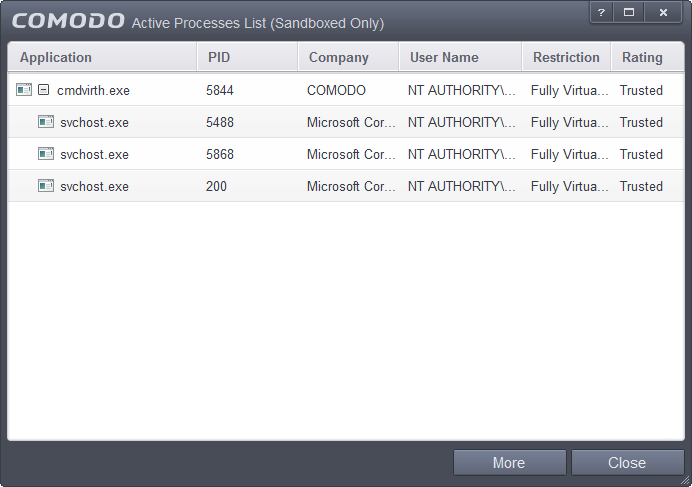
Column Descriptions
- Application – Displays the names of applications that are currently running.
- PID – Process Identification Number.
- Company – Displays the name of the software developer.
- User Name – The name of the user that started the process.
- Restriction – Displays the level of containment selected for the program.
- Rating – Displays the rating of the application, whether trusted or unknown.
Right-click on any process to:
- Show full path: Displays the location of the executable in addition to it's name.
- Show Contained Only: Will only show programs that are running inside the container.
|
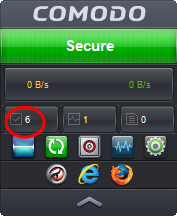
Tip: You can open the Active Process List screen that shows only the processes that are currently running inside the containment by clicking the process button from the CCS widget. Refer to the section Viewing Active Processes list of Contained Applications for more details. |
- Add to Trusted Files: The selected unknown program is added to the CCS File List and given a status of 'Trusted'. Refer to the section File List for more details.
- Online Lookup: Conducts a look-up of the program in Comodo's global blacklists and whitelists. The results will tell you whether the file is clean, malicious or unknown.
- Submit: The selected application will be sent to Comodo for analysis.
- Jump to Folder: The folder containing the executable file of the application will open.
- Show
Activities: Opens the Process
Activities List dialog. The Process Activities dialog will
display the list activities of the processes run by the application.
The 'Show Activities' option is available only if Viruscope is enabled under Advanced
Settings > Advanced Protection > Viruscope.
If KillSwitch is not yet installed, clicking this button will prompt you to download the application. Refer to the section Identify and Kill Unsafe Processes for more details.
Viewing
Active Processes list of Contained Applications
- Auto-Containment - Applications that are run inside the containment as per the rules defined for them or by default containment rules. Refer to the section 'Configuring Rules for Auto-Containment' for more details on defining auto-containment rules.
- Run Virtual - Applications that are selected and run in Containment. Refer to 'Run an Application in the Container' for more details.
- Applications that are run inside the containment using the context sensitive menu - Click here for more details.
- Running browsers inside the containment from Widget - Click here for more details.
- Drag-and-drop applications on to CCS Home Screen - Click here for more details.
-
Programs that are added manually - Refer to the section 'Configuring Rules for Auto-Containment' for more details.
To view Active Process list of contained applications
- Click the first box in the second row in the CCS Widget.
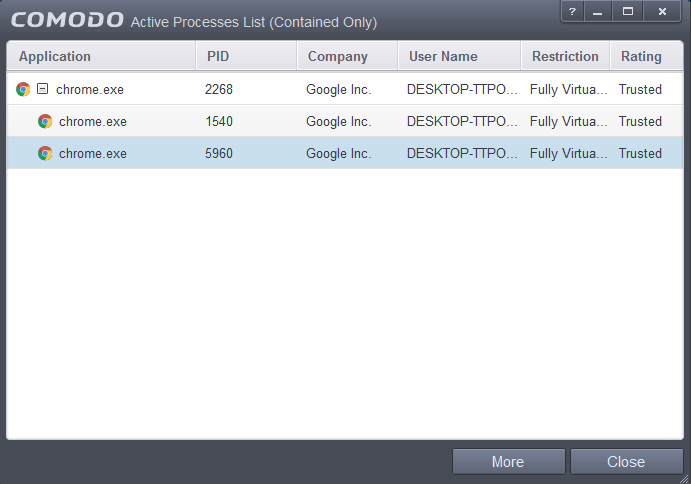
The Active Processes List (Contained Only) screen will be displayed.