Run an Application in the Container
Comodo Client Security allows you to run programs in containment on a 'one-off' basis. This is helpful to test the behavior of new executables that you have downloaded or for applications that you are not sure that you trust. Adding a program in this way means that it will run in the container this time only. On subsequent executions it will not run outside the container (presuming an auto-
containment
rule is not created for it).
You can also create a desktop shortcut to run the application inside the containment on future occasions. The following image shows hows a 'virtual' shortcut will appear on your desktop:
![]()
Note: If you wish to run an application in the container on a long-term/permanent basis then add the file to the containment
To run an application in the Containment
1. Open the
'Containment Tasks' interface and Click 'Run Virtual'.
2. The 'Run Virtual' dialog will be displayed.
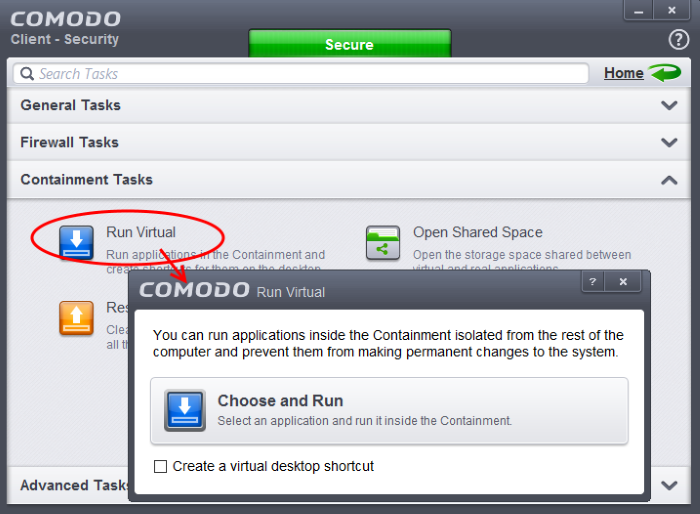
3. To run an application inside the container, click 'Choose and Run' then browse to the application. The application will run with a green border indicating that it is contained. If you wish to run the application in the container in future, then select 'Create a virtual desktop shortcut'.
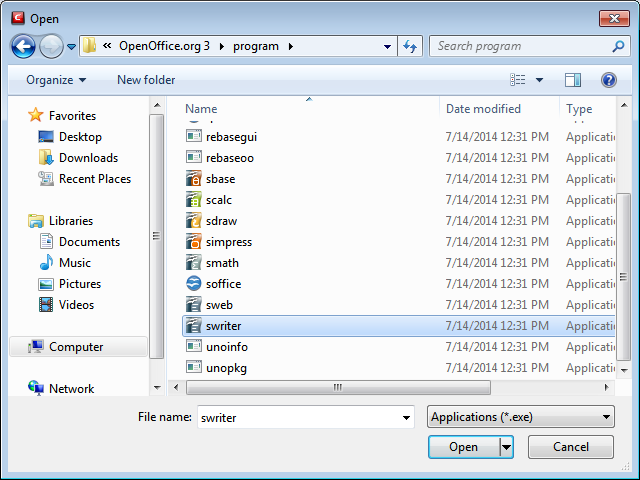
4. Browse to the application and click 'Open'. In the example above, Open Office Writer is chosen.
Alternatively, you can run an application inside the containment by the following shortcut methods:
Drag-and-drop the application on to CCS Home Screen
The Home screen of the CCS interface has a flippable pane at the left side allowing you to run instant scans or run a program in the container. To flip the pane to carry out these tasks, just click the curved arrow at the top right side of the pane.
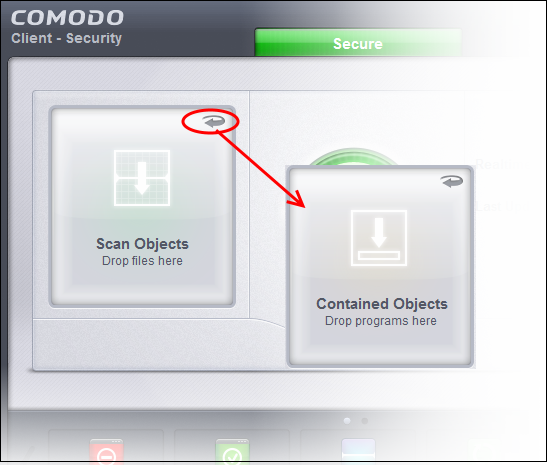
- To run a program in a contained environment, first flip the pane by clicking the curved arrow at the top right side to display 'Contained Objects'.
- Now, navigate to the program in your system that you want to run in contained environment and just drag and drop into the box.
Running
a program from the context sensitive menu
- Navigate to the program in your system that you want to run in contained environment and right click on it
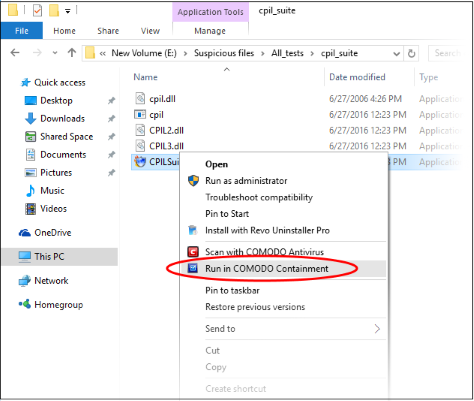
- Choose 'Run in Comodo Containment' from the context sensitive menu.
Running Browsers inside the Containment
The
CCS Desktop Widget displays shortcut icons of the browsers installed
in your computer.

- Clicking on a browser icon will start the browser inside the containment.
The browser will be started and executed inside the container at 'Contained' level. CCS displays a green border around the windows of programs to indicate that they are running inside the contained environment, if the setting 'Show
highlight frame for virtualized programs'
is enabled in Sandbox
Settings.
The application will run in the container on this occasion only. If you often want the browser to run inside the contained environment then create a 'virtual shortcut' for the application by selecting the check-box 'Create a virtual desktop shortcut' in step 3 if you wish to run an application in the container on a long-term/permanent basis then Configuring Rules for Auto-Containment.



