View Active Internet Connections
The 'View
Connections' interface displays an
'at-a-glance' summary of all currently
active Internet connections per-application. You
can view all individual connections that each application is
responsible for; the direction of the traffic; the
source IP/port and the destination IP/port.
You can also view the total amount of traffic that has passed in and
out of your system over each connection.
This list is updated in real time whenever an application creates a new connection or drops a connection. The 'View Connections' is extremely useful for testing firewall configuration, troubleshooting new firewall rules, monitoring individual applications and for terminating any unwanted connections.
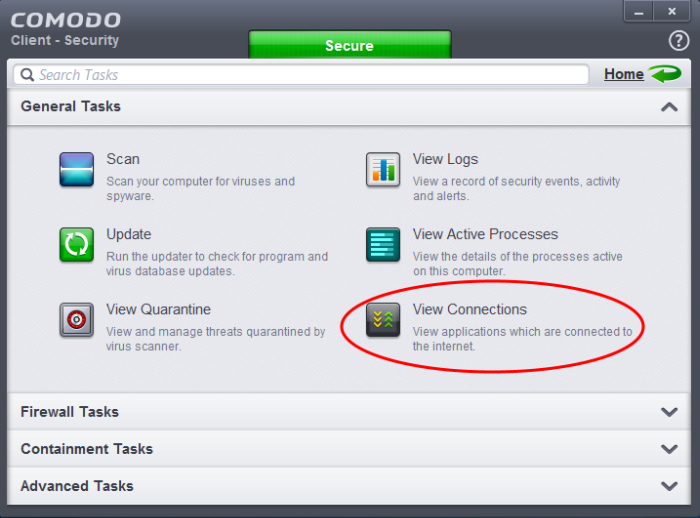
The 'View Connections' interface can be accessed by clicking 'View Connections' from the 'General Tasks' interface.
All currently active internet connections are shown in a tree structure:
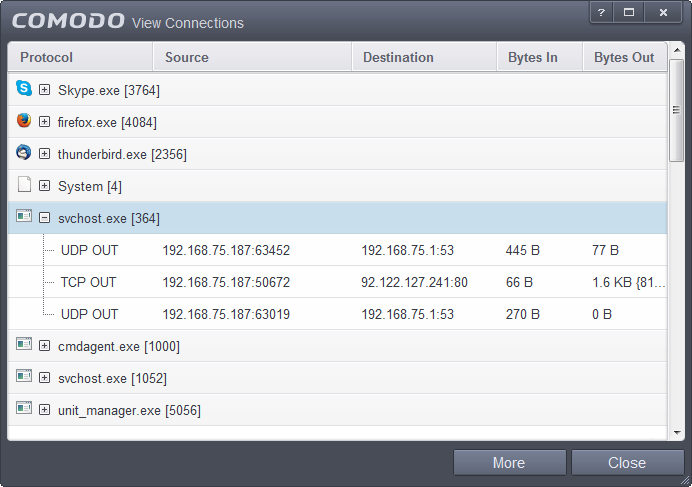
Column Descriptions
- Protocol - Shows the application that is connected, the protocol it is using and the direction of traffic. An application may have more than one connection at any time. Clicking + at the left of the application name expands the list of connections created.
- Source (IP: Port) - The IP and port that the application is connecting from. If the application is waiting for communication and the port is open, it is described as ‘Listening’.
- Destination (IP: Port) - The IP and port that the application is connecting to. This is blank if the 'Source' column is 'Listening'.
- Bytes In - Represents the total bytes of incoming data since this connection was first allowed.
- Bytes Out - Represents the total bytes of outgoing data since this connection was first allowed.
Context Sensitive Menu
-
Right click on an item in the list to see the context sensitive menu.
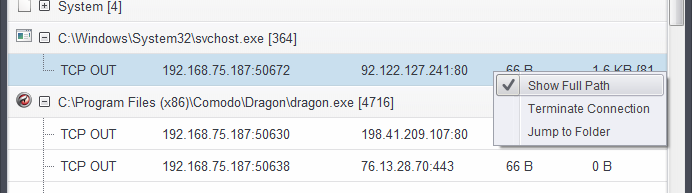
-
If you wish to view the full path of the application, right click on the application name and select 'Show Full Path'.
-
If you wish to terminate a connection, right click on the specific connection and click 'Terminate Connection'.
- If you wish to open the folder containing the executable file of the application, click 'Jump to Folder'.
Identify and Kill Unsafe Network Connections
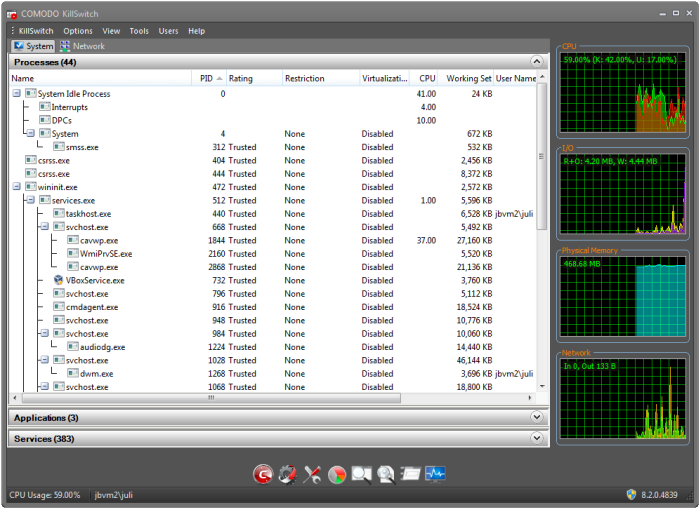
Comodo KillSwitch can show ALL running processes with their granular details– exposing even those that were invisible or very deeply hidden. It allows you to identify which of those running processes are unsafe and shut them all down with a single click. You can also use Killswitch to trace back to the malware that generated the process.
Comodo KillSwitch can be directly accessed from the 'View Connections' by clicking the 'More' button.
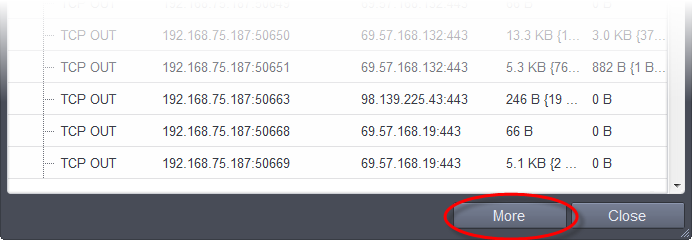
If Comodo KillSwitch is already installed in your computer, clicking 'More' will open the Kill switch interface. If not, CCS will download and install Comodo Killswitch.
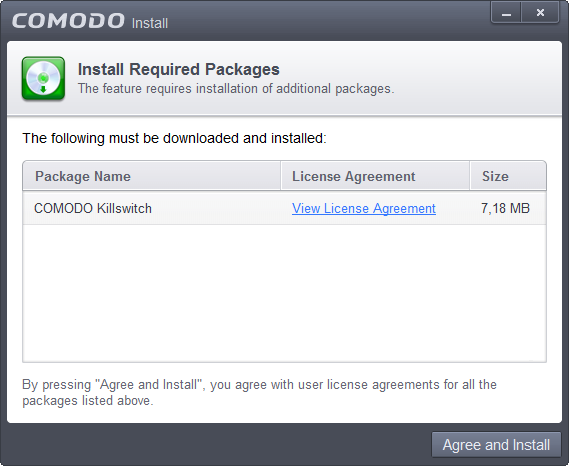
- Read the license agreement by clicking 'View License Agreement' and click 'Agree and Install'. CCS will download and install the application.
After installation, the Comodo KillSwitch main interface will open. The main interface contains three panes - Processes, Applications and Services. Clicking the 'Network' tab will display the the Network Connections and Network Utilization panes.
- Details on how to use KillSwitch to identify terminate unsafe connections can be found at http://help.comodo.com/topic-119-1-328-3577-Viewing-and-Handling-Network-Connections-and-Usage.html.
- The complete user guide for Comodo KillSwitch is available at http://help.comodo.com/topic-119-1-328-3518-Introduction-to-KillSwitch.html



