Importing/Exporting and Managing Personal Configurations
The CCS configurations can be exported/imported, activated and managed through the Configuration panel accessible by clicking 'Configuration' tab under 'General Settings' in 'Advanced Settings' interface.
Click the area on which you would like more information:
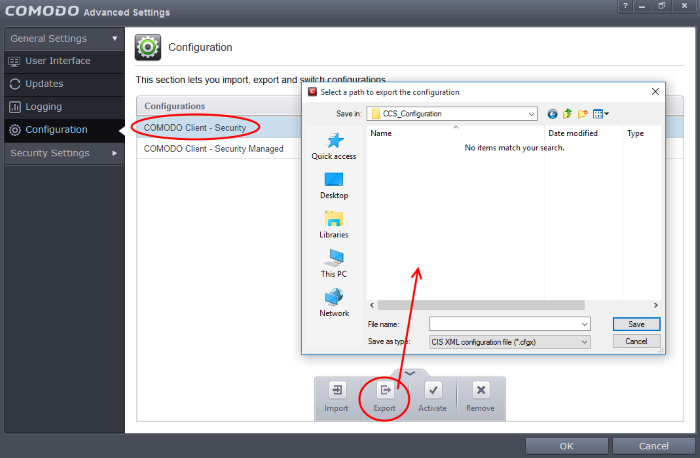
Exporting a stored configuration to a file
1. Open 'Configurations' panel by clicking 'Configuration' under General Settings in 'Advanced Tasks' interface
2. Select the configuration, click the handle from the bottom and choose 'Export'. The Select a path to export the configuration dialog will open.
-
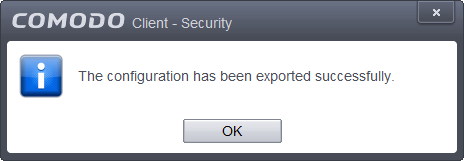
Navigate to the location where you want to save the configuration file, type a name (e.g., 'Default CES Configuration') for the file to be saved in .cfgx format and click 'Save'.
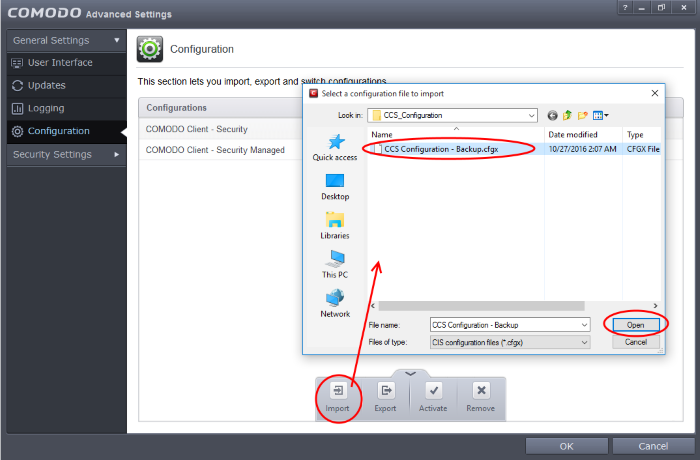
Importing a saved configuration from a file
Importing a configuration profile allows you to store any profile within Comodo Client Security. Any profiles you import do not become active until you select them for use.
To import a profile
-
Open 'Configurations' panel by clicking 'Configuration' under General Settings in 'Advanced Tasks' interface, click the handle from the bottom and choose Import from the options.
-
Navigate to the location of the saved profile and click 'Open'.
-
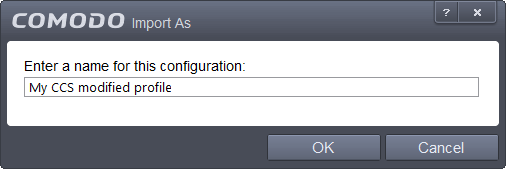
The 'Import As' dialog will appear. Enter a name for the profile you wish to import and click 'OK'.
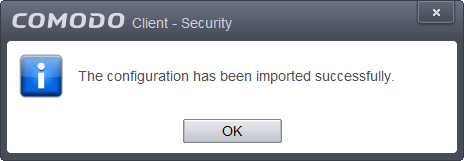
A confirmation dialog will appear indicating the successful import of the profile.
Once imported, the configuration profile is available for deployment by selecting it.
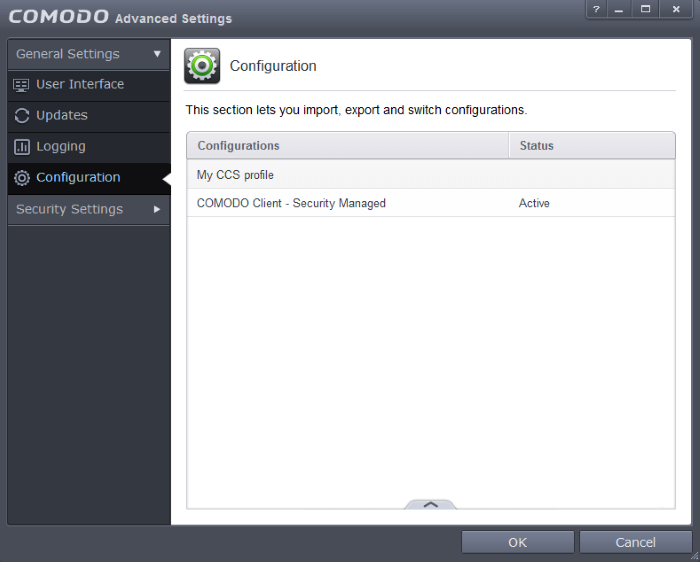
Selecting and Implementing a different configuration profile
You can change the configuration profile active in CCS at any time from the 'Configurations' panel
To change the active configuration profile
-
Open 'Configurations' panel by clicking 'Configuration' under General Settings in 'Advanced Tasks' interface.
-
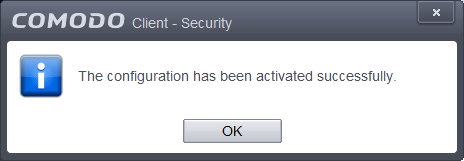
Select the configuration profile you want to activate, click the handle from the bottom and choose Activate from the options.
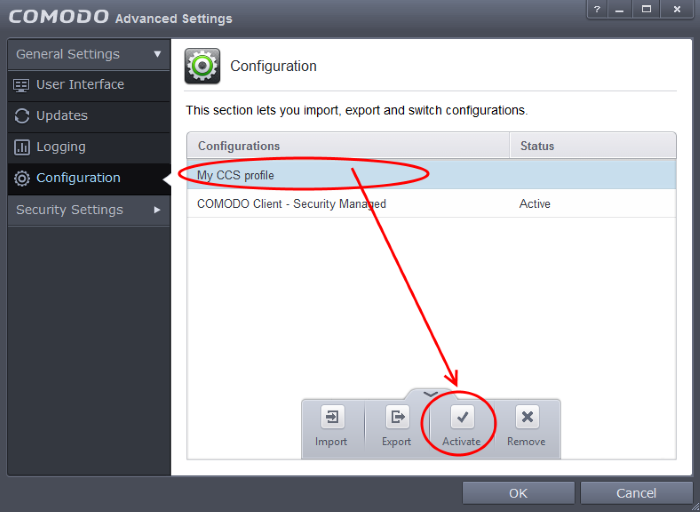
You will be prompted to save the changes to the settings in you current profile before the new profile is deployed.
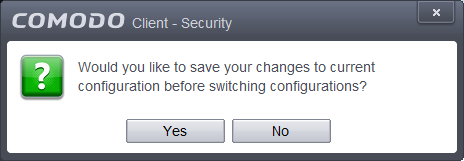
-
Click 'Yes' to save any setting changes in the current configuration, else click 'No'.
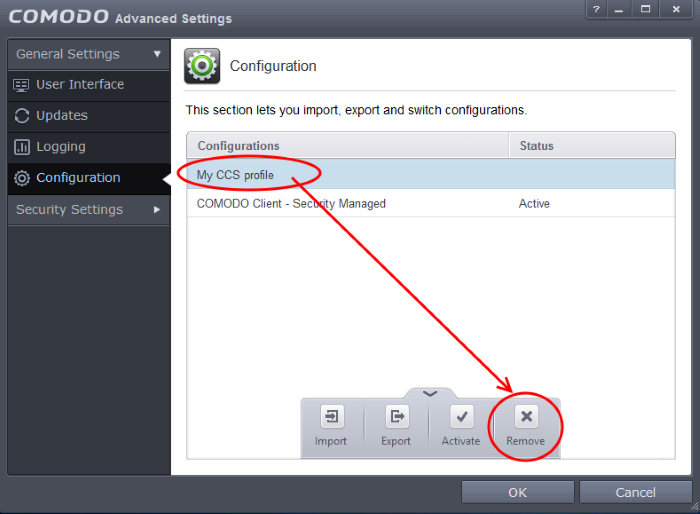
You can remove any unwanted configuration profiles from the list of stored configuration profiles. You cannot delete the profile that Comodo Client Security is currently using - only the inactive ones. For example if the COMODO One Client - Security Managed is the active profile, you can only delete the inactive profiles, 'My_CCS_Configuration and so on.
To remove an unwanted profile
-
Open 'Configurations' panel by clicking 'Configuration' under General Settings in 'Advanced Tasks' interface
-
Select the configuration profile you want to delete, click the handle from the bottom and choose 'Remove' from the options.
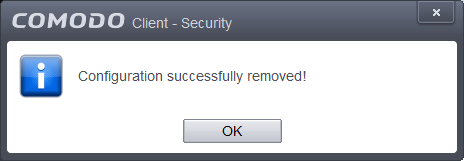
A confirmation dialog will be displayed.
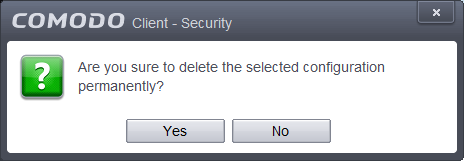
-
Click 'Yes'. The configuration profile will be deleted from your computer.