Configure Program and Virus Database Updates
The 'Updates' area allows you to
configure settings that govern CCS program and virus database
updates.
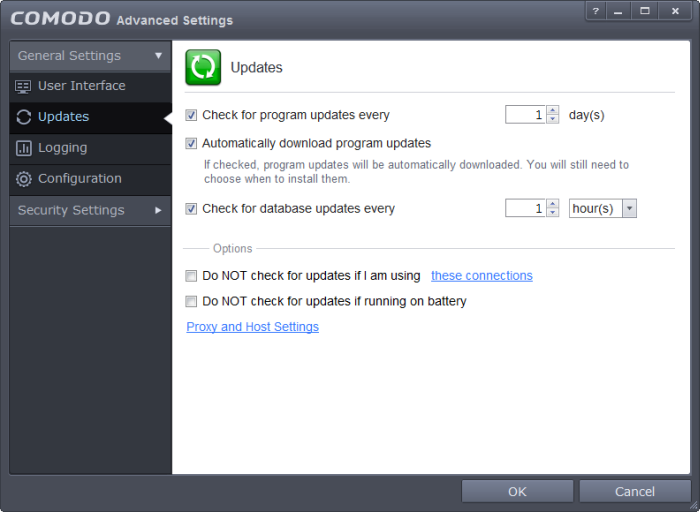
This screen can be accessed by clicking 'Updates' under the 'General Settings' section of 'Advanced Settings':
-
Check program updates every NN day(s) - Enables you to set the interval at which CCS will check for program updates. Select the interval in days from the drop-down combo box. (Default=Disabled)
- Automatically download program updates - Instructs CCS to automatically download program updates as soon as they are available. (Default=Enabled)
- Check for database updates every NN hour(s)/day(s) - Enables you to set the interval at which CCS will check for virus signature database updates. Select the interval in hours or days from the first drop-down combo box and set hours or days in the second drop-down box. (Default and recommended = 1 hours)
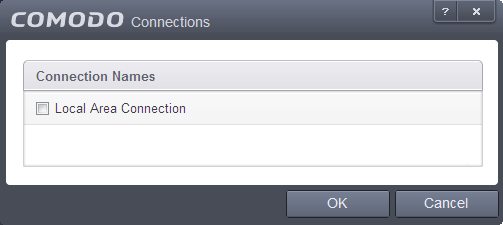
- Do NOT check updates if am using these connections - Enables you to restrict CCS from checking for updates if you use certain types of Internet connection. For example, you may not wish to check updates if using a wireless connection you know to be slow or not secure. (Default=Disabled)
To do this:
- Select the 'Do NOT check updates if am using these connections' check-box
- Then click the 'these connections'. The connections dialog will appear with the list of connections you use.
- Select the connection through which you do not want CCS to check for updates and click 'OK'.
-
Do NOT check for updates if running on battery – If enabled, CCS will not download updates if it detects your computer is running from battery power. This is intended to extend battery lifetime on laptops. (Default = Disabled)
-
Proxy and Host Settings – Allows you to select the host from which updates are downloaded. By default, CCS will directly download updates from Comodo servers. However, advanced users and network admins may wish to first download updates to a proxy/staging server and have individual CCS installations collect the updates from there. The 'Proxy and Host Settings' interface allows you to point CCS at this proxy/staging server. This helps conserve overall bandwidth consumption and accelerates the update process when large number of endpoints are involved.
|
Note: You first need to install Comodo Offline Updater in order to download updates to your proxy server. This can be downloaded from http://enterprise.comodo.com/security-solutions/endpoint-security/endpoint-security-manager/free-trial.php |
To configure updates via proxy server
-
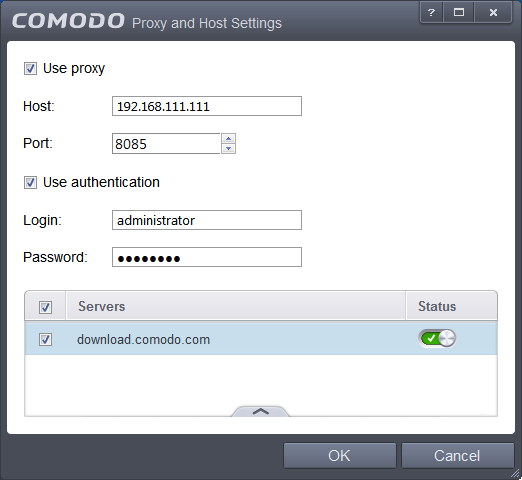
Click 'Proxy and Host Settings' at the bottom of the 'Updates' interface. The 'Proxy and Host Settings' interface will open.
-
Select the 'Use Proxy' check-box
-
Enter the host name and port numbers. If the proxy server requires access credentials, select the 'Use Authentication' check-box and enter the login / password accordingly.
-
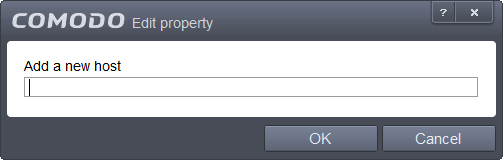
You can add multiple servers from which updates are available. To do this, click the handle at the bottom center of the 'Servers' panel, click the 'Add' button then enter the host name in the 'Edit Property' dialog.
- If you specify multiple servers:
- Activate or deactivate each update server using the 'Active' toggle switch beside it.
- Use the 'Move Up' and 'Move Down' buttons to specify the order in which each server should be consulted for updates. CCS will commence downloading from the first server that contains new updates.
- Click 'OK' for your settings to take effect.