Log Settings
By default, Comodo Client Security maintains detailed logs of all Antivirus, HIPS, Containment, VirusScope and Firewall events. Logs are also created for 'Website Filtering', 'Device Control Events', 'Alerts Displayed', 'Tasks' 'File List Changes, Trusted Vendors List Changes 'and 'Configuration Changes'.
- The 'Logging' interface allows you to specify the locations for storing log file, maximum size of the log file in local storage and how CCS should react if the maximum file size is exceeded.
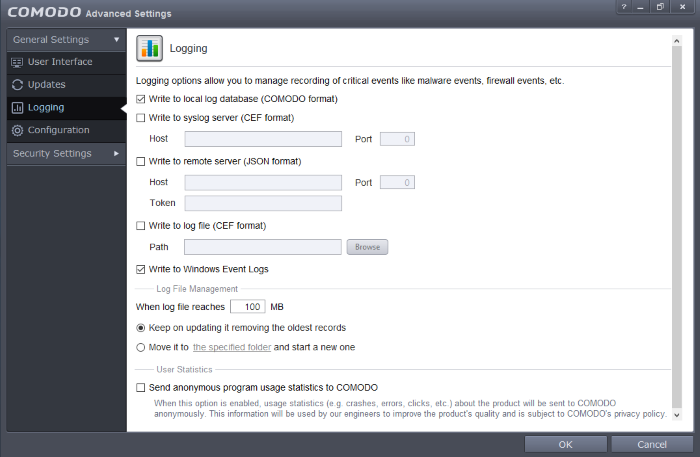
- Write to Local Log Database(Comodo format) – Instructs CCS to store the log files in the local storage of the
endpoint in Comodo format so that they can be viewed from Tasks >
General Settings > View Logs interface. Refer to the section
'View Logs'
for more details. The Log storage depends on
the log file management settings configured in the 'Log
File Management' settings area in the same interface. (Default
= Enabled)
-
Write to Syslog Server(CEF Format) – Instructs CCS to forward the log files to an external Syslog Server integrated with the ITSM server that remotely manages your CCS installation. Enter the IP address/hostname of the Syslog server in the Host text field and enter the port through which Syslog server listens to ITSM in the 'Port' field. (Default = Disabled)
- Write to remote server (JSON format) - Instructs CCS to forward the log files to HTTPS in JSON format on a remote server integrated with the ITSM server that remotely manages your CCS installation. Enter the IP address/hostname of the remote server in the Host text field and enter the port through which remote server listens to ITSM in the 'Port' field. Enter the security token to access the remote server in the Token text field. (Default = Disabled)
- Write to Log file (CEF) Format – Instructs CCS to store the log files at a specified location in the local storage or a network storage, in Common Event Format (CEF) format, also known as NCSA Common Log Format, which is standardized text file format. When selecting this option, click 'Browse', select the storage location and navigate to the log file to which the logs are to be added. (Default = Disabled)
- Write to Windows Event Logs – Instructs CCS to store the log events to the Windows Event Logs. (Default = Enabled)
Log File Management
- If the log file's size exceeds (Mb) - Enables you to specify behavior when the Local Log Database (Comodo Format) log file reaches a certain size. You can decide on whether to maintain log files of larger sizes or to discard them depending on your future reference needs and the storage capacity of your hard drive.
- Specify the maximum limit for the log file size (in MB) in the text box beside 'If the log file's size exceeds (MB)'. (Default = 100MB)
If you want to discard the log file if it reaches the maximum size, select 'Delete it and create a new one'. Once the log file reaches the specified maximum size, it will be automatically deleted from your system and a new log file will be created with the log of events occurring from that instant. (Default = Enabled)
If you want to save the log file even if it reaches the maximum size, select 'Move it to' and select a destination folder for the log file. (Default = Disabled)
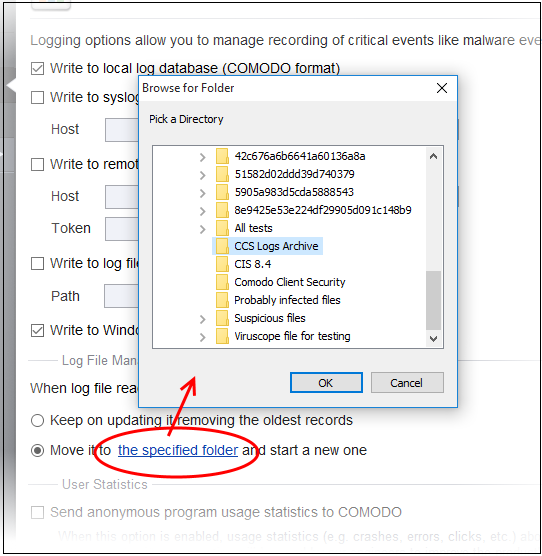
The selected folder path will appear beside 'Move it to'.
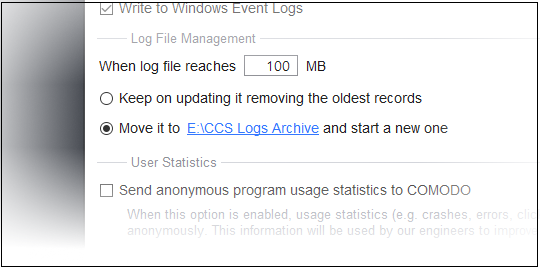
Once the log file reaches the maximum size, it will be automatically moved to the selected folder and a new log file will be created with the log of events occurring from that instant.
User Statistics
- Send
anonymous program usage statistics to Comodo - Comodo collects
the usage details from millions of CCS users to analyze their usage
statistics (e.g. clicks, crashes, errors etc) to Comdo in order to
improve the product's quality - for the continual enhancement of the
product. Your CCS installation will collect details on how you use
the application and send them periodically to Comodo servers
through a secure and encrypted channel. Also your privacy is
protected as this data is sent anonymous. This data will be useful
to the engineers and developers at Comodo to identify the areas to
be developed further for delivering the best Internet Security
product. Disable this option if you do not want your usage details
to be sent to Comodo. (Default = Disabled)



