Manage File Rating
The file rating system is a cloud-based file lookup service (FLS) that ascertains the reputation of files on your computer. Whenever a file is first accessed, CCS will check the file against Comodo's master white and blacklists.
The file will be awarded trusted status if:
- The application/file is in the trusted local File List;
- The application is from a vendor included in the Trusted Software Vendors list
- The application is included in the extensive and constantly updated Comodo safelist
Trusted files are excluded from monitoring by HIPS - reducing hardware and software resource consumption. On the other hand, files which are identified as malicious will be awarded 'Malicious' status and denied all access rights from other processes or users - effectively cutting them off from the rest of your system. Files which could not be recognized by the rating system are awarded 'Unrecognized' status'. You can review files on the unrecognized list and manually choose to trust/block/delete them or investigate further by sending them to Comodo for analysis/running another file lookup. Refer to the section File List for more details.
|
Important Note: In order for the software to submit unknown files to our file rating and malware analysis servers (CAMAS), please make sure the following IP addresses and ports are allowed on your network firewall:
|
The 'Manage File Rating' area allows you to view and manage the list of programs, applications and executable files discovered from your computer with their assigned file rating. You can also:
- Manually add files and executables to Trusted Files list.
- Submit unrecognized files for look-up and view the list of files you have submitted previously.
- View and manage the Trusted Software Vendor list.
Click the following links to jump to the section you need help with:
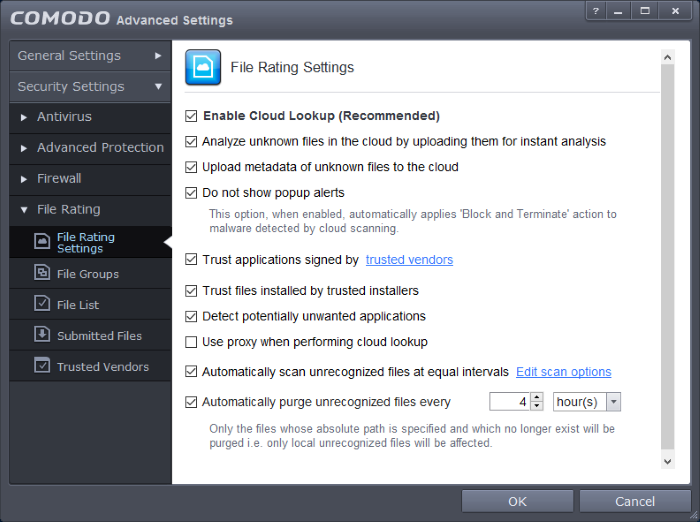
- File Rating Settings - Configure settings that govern the overall behavior of file rating.
- File Groups - Create predefined groups of one or more file types.
- File Lists - View the list of programs. Applications and executable files in your computer with their file rating and manually add files to it
- Submitted Files- View any files already submitted to Comodo for analysis.
- Trusted Vendors - View the list of trusted software vendors and manually add vendors



