Network Zones
- Click 'Settings' > 'Firewall' > 'Network Zones' > 'Network Zones'
- A 'Network Zone' can consist of an individual machine (like a home computer connected to the internet) or a network of thousands of machines. You can grant or deny access to a network zone as required.
|
Background Note:
|
- The network zones panel lets you configure trusted and untrusted networks.
Add and manage network zones
- Click 'Settings' on the CCS home screen
- Click 'Firewall' > 'Network Zones'
- Click the 'Network Zones' tab
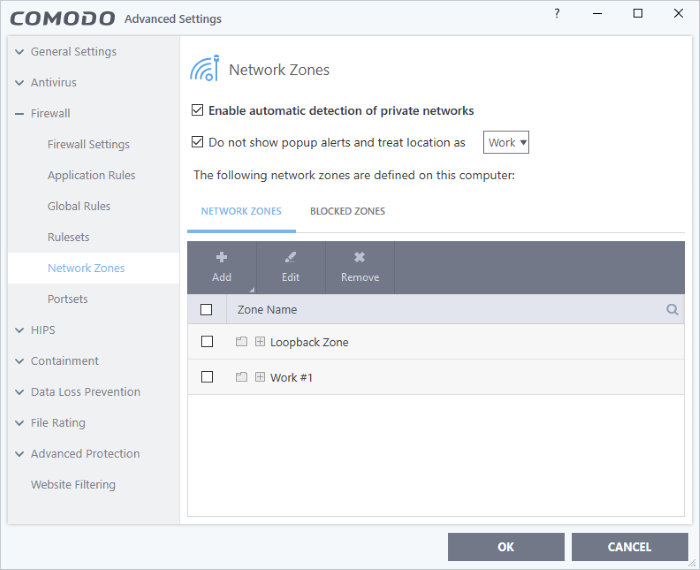
The network zones tab shows zones
that have already been added to CCS. You can
add new zones and manage existing zones.
|
Note 1: Adding a zone to this area does not, by itself, define any permissions or access rights to the zone. This area lets you define the zones so you can assign such permissions in other areas of the firewall. Note 2: A network zone can be designated as 'Trusted' and allowed access from the 'Manage Network Connections' interface. An example would be your home computer or network. Note 3: A network zone can be designated as 'Blocked' and denied access by using the 'Blocked Zones' interface. An example would be a known spyware site. Note 4: An application can be assigned specific access rights to and from a network zone when defining an Application Rule. Similarly, a custom Global Rules assigned to a zone will inspect all traffic to/from a zone. Note 5: By default, Comodo Firewall automatically detects any new networks (LAN, Wireless etc) once you connect to them. This can be disabled by deselecting the option 'Enable automatic detection of private networks' in the Firewall Settings panel. |
You can use search for a specific zone by clicking the search icon and entering the name of the zone in part or full.
Define a new Network Zone
To add a new network zone:
-
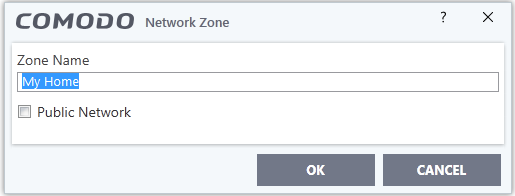
Step 1 - Define a name for the zone
Step 1 - Define a name for the zone
- Click 'Settings' on CCS home screen
- Click 'Firewall' > 'Network Zones'
- Click the 'Network Zones' tab
- Click the 'Add' button at the top of the list and choose 'New Network Zone' from the options
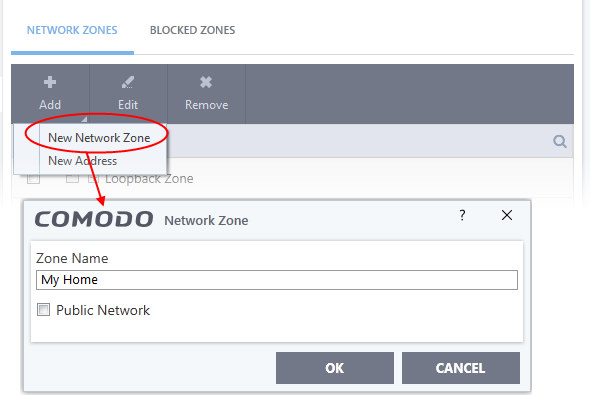
- Choose a name that accurately describes the network zone you are creating.
- Select 'Public Network' if you are defining a network zone for a network in a public place. For example, when you are connecting to a Wi-Fi network at an airport, restaurant etc. The firewall will optimize the connection accordingly.
- Click 'OK' to confirm your zone name.
This adds
your new zone to the 'Network Zones' list.
Step 2 - Select the addresses to be included in this zone
- Select the network zone name then click the 'Add' button at the top
- Choose 'New Address' from the options
- Alternatively, right click on the network zone and choose 'Add' > 'New Address' from the context sensitive menu
The 'Address' dialog allows you to select an address from the 'Type' drop-down box shown below (Default = Any Address)
The 'Exclude' check box will become active if you select anything other than 'Any Address'
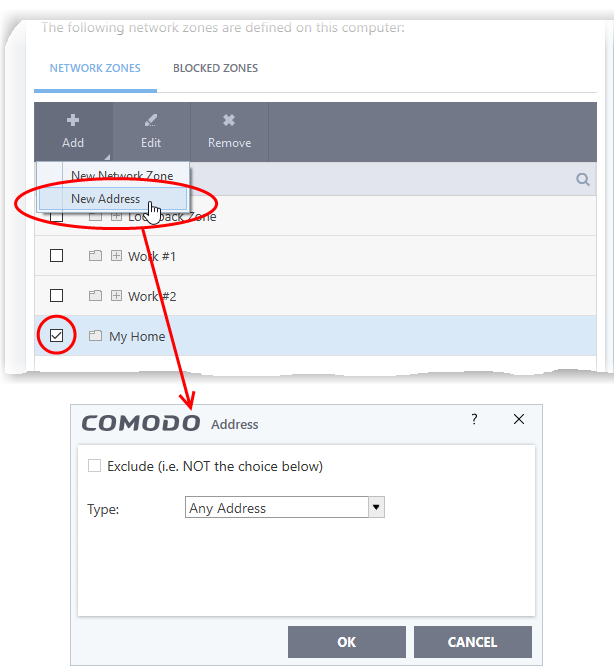
Address Types:
-
Any - Defaults to an IP range of 0.0.0.0- 255.255.255.255 to block connection from all IP addresses.
-
Host Name - Choose a named host which denotes your IP address. Enter the name in the 'Host Name' text field
-
IPv4 Address Range – Choose all IP addresses covered by a range - for example a range in your private network.
- Enter the first and last IP addresses in the 'Start IP' and 'End IP' text boxes.
-
IPv4 Single Address - Choose a single IPv4 address
- Enter the IP address in the 'IP' text box, e.g., 192.168.200.113.
-
IPv4 Subnet mask - Choose an IPv4 network. IP networks can be divided into smaller networks called sub-networks (or subnets). An IP address/ Mask is a subnet defined by IP address and mask of the network.
- Enter the IP address and Mask of the network.
-
IPv6 Address Range - Choose all IPv6 addresses covered by a range - for example a segment in your private network
- Enter the first and last IPv6 addresses in the 'Start IP' and 'End IP' text boxes.
-
Single IPv6 Address - Choose an IPv6 address
- Enter the IP address in the 'IP' text box, e.g., 3ffe:1900:4545:3:200:f8ff:fe21:67cf.
-
IPv6 Subnet Mask – Choose a IPv6 network. IP networks can be divided into smaller networks called sub-networks (or subnets). An IP address/ Mask is a subnet defined by IP address and mask of the network.
- Enter the IP address and 'Mask' of the network in the respective fields
-
MAC Address - Choose a single source/destination by specifying its physical address
- Enter the physical address in the 'MAC Address' text box.
- Exclude (i.e. NOT the choice below) - The opposite of what you specify is applicable.
2. Click 'OK' to confirm your choice.
3. Click 'OK' in the 'Network Zones' interface.
The new zone now appears in the main list along with the addresses you assigned to it.
- Quickly called as 'Zone' when creating or modifying a firewall ruleset
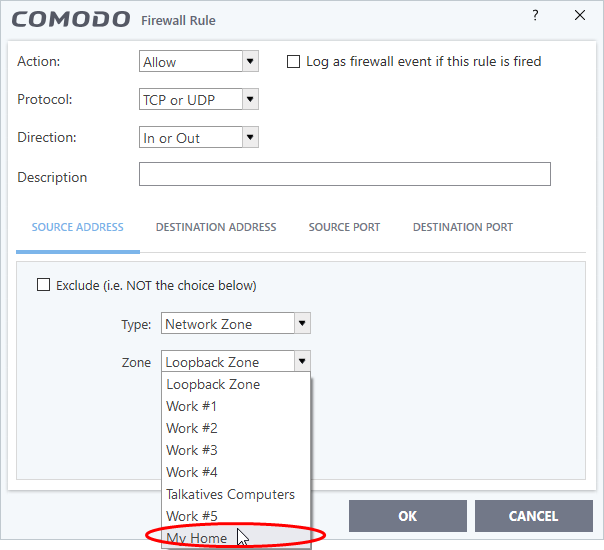
- Quickly called and designated as a blocked zone from the 'Blocked Zones' interface.
Edit the name of an existing Network Zone
- Click 'Settings' on the CCS home screen
- Click 'Firewall' > 'Network Zones'
- Click the 'Network Zones' tab
- Select the zone from the list (e.g., My Home) and click the 'Edit' button from the top or double click on the network zone name
- Edit the name of the zone.
- Select the network name, click 'Add' > 'New Address' from the top
- Add new address from the 'Address' interface
To modify or change the existing address in a zone
- Click the + button beside the network zone name to expand the addresses
- Double click on the address to be edited or select the address, click 'Edit' at the top
- Edit the address from the 'Address' interface'
To remove an existing address in a zone
- Click the '+' button beside the network zone name to expand the addresses
- Select the address and click 'Remove' from the top



