Miscellaneous Settings
-
Click 'Assets' > 'Configuration Templates' > 'Profiles'
-
Open the Windows profile you want to work on
Click the 'Miscellaneous' tab then 'Edit', if it has already been added to the profile
OR
Click 'Add Profile Section' > 'Miscellaneous' if it hasn't yet been added
The 'Miscellaneous' settings screen opens:
-
Detect shellcode injections:
A shellcode injection is an attack which exploits software vulnerabilities to give attackers control of a compromised machine.
For example, shellcode attacks are often used to create buffer-overflows on victim machines. Enable this setting to turn-on buffer overflow protection.
By default, Xcitium Client Security (XCS) monitors all applications to make sure they do not suffer shellcode attacks.
However, you may want to omit certain applications from protection for compatibility reasons. Click the 'Exclusions' link to do this.
The process to add exclusions is similar to that explained in Containment Settings.
Background: A buffer overflow is an anomalous condition where a process/executable attempts to store data beyond the boundaries of a fixed-length buffer. The result is that the extra data overwrites adjacent memory locations. The overwritten data may include other buffers, variables and program flow data, and may cause a process to crash or produce incorrect results. As such, buffer overflows cause many software vulnerabilities and are the basis of many exploits.
-
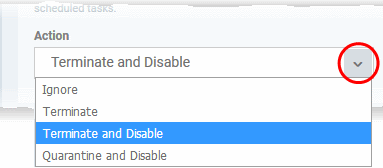
Apply the selected action to...' - XCS will monitor registry entries related to Windows services, auto-run items and scheduled tasks. If any entries are created or modified by unrecognized files/scripts, they will handled per the action chosen. (Default = Enabled)
Xcitium recommends this setting is left enabled (Default = Enabled).
-
Apply the selected signature level while.... - XCS identifies untrusted DLLs, apps, portable executables (PE) and autoruns launched before XCS starts on the endpoint. These may expose the endpoint to a danger if those items turn to be malicious. (Default = Disabled)
XCS checks whether startup items are signed by a trusted authority and marks them as trusted or untrusted. The flag is used at next restart to allow or block the item.
You can choose how strict the certificate check should be:
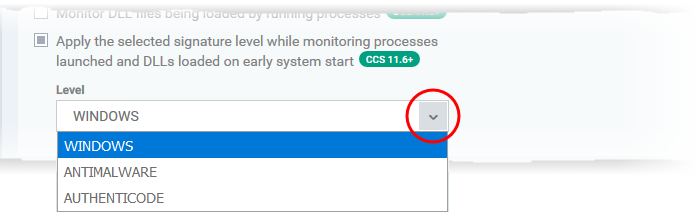
Windows- Only items signed by Microsoft certificates are marked as trusted
Antimalware - Trusts files signed by either Microsoft or Antimalware certificates
Authenticode - Flags all signed files as trusted
- Monitor DLL files being loaded by running processes - XCS monitors the DLL files loaded to system memory, by processes that are currently running on the endpoint (Default = Disabled).
If enabled, XCS runs a file rating scan on each DLL loaded to identify its trust rating.
The trust rating is reported to Xcitium. Files with an Unrecognized' rating are submitted to Valkyrie for analysis
- You can view these details at 'Security' > 'Endpoint Security' > 'Application Control'. See Manage File Trust Ratings on Windows Devices for more details.
- Self-Protection Options: Allows to protection for Xcitium Client - Security agent's own processes and assets. (Default = Enabled).
- Protect comodo files - Access to blocking protected folders (CCS folders), driver/guard dll files.
- Protect comodo Registry key – Allows you to protect system critical registry keys against modification.
- Protect comodo processes - Access blocking to processes (XCS processes) with write/terminate permissions and on win10and block loading unsigned DLLs into processes (XCS processes).
- Audit Only - The audit mode sends a notification about access to protected folders (xcs folders), drivers/guard dll files, notification about access to services in the registry, (XCS processes) with write/terminate permissions and loading unsigned DLLs into processes (CCS processes).
- Click 'OK' to save your settings.



