Disable Auto-Containment on a Per-application Basis
- The default auto-containment rules will run all unknown executables in the container and queue them for submission to Comodo for behavior analysis.
- Comodo recommends most users leave this setting intact to ensure the highest protection levels.
- Should you wish, you can create an 'Ignore' rule to exclude certain files or file types from containment.
- This is could be useful for developers testing new applications which, by their nature, are unknown to the Comodo safe list.
Create an auto-containment exception
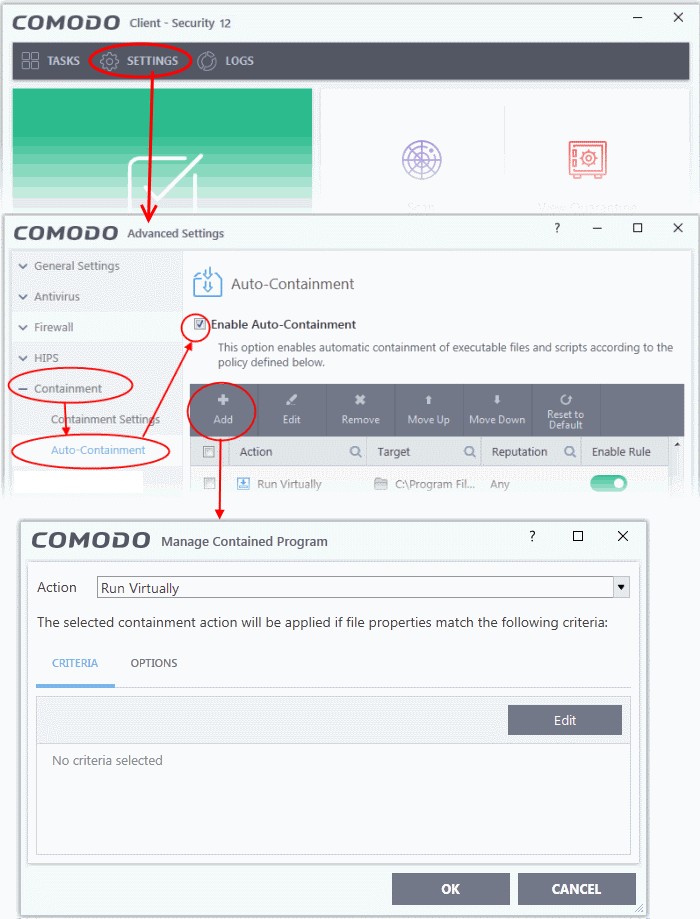
1. Click 'Settings' on the CCS home screen
2. Click 'Containment' > 'Auto-Containment' on the left
3. Ensure that 'Enable Auto-Containment' is selected
4. Click 'Add' to create a new rule:
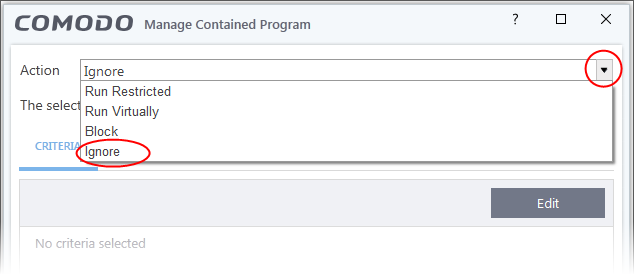
5. Select 'Ignore' from the 'Action' drop-down:
6. Click the 'Edit' button under the 'Criteria' tab
7. Click 'Browse' to specify the type of item you wish to exclude:
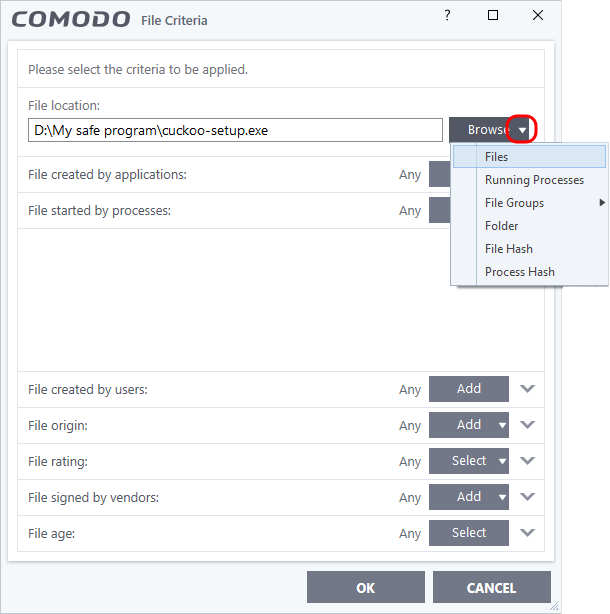
8. You can select individual files, folders, processes, file groups or hashes. Click 'Open' when you have made your selection.
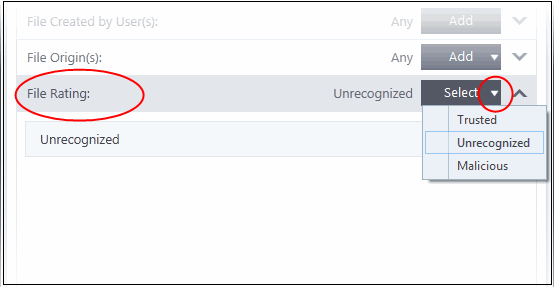
9. Click 'Select' at the end of the 'File Rating' row and select 'Unrecognized' from the drop-down:
10. Next, click the 'Options' tab.
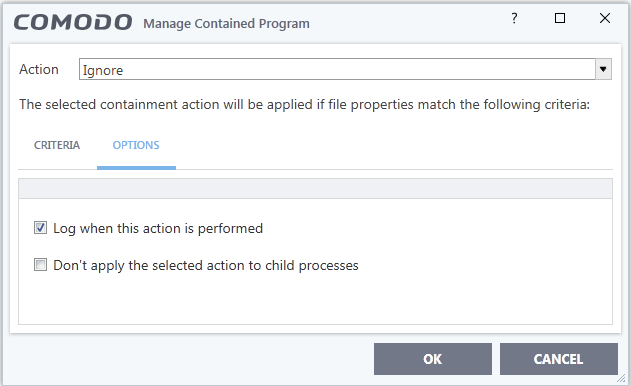
- Log when this action is performed - Optional. Whenever this rule is applied for a file, it will be added to CCS containment logs.
- Don't apply the selected action to child processes - Child processes are processes spawned by a parent application. By default, CCS treats all child processes individually.
- Disabled - The ignore rule will apply to the target application and all child processes that it spawns. All will be allowed to run outside the container.
- Enabled - The ignore rule will apply only to the target application. All child processes will be inspected and possibly contained as per their file rating.
11. Select options as required and click 'OK'.
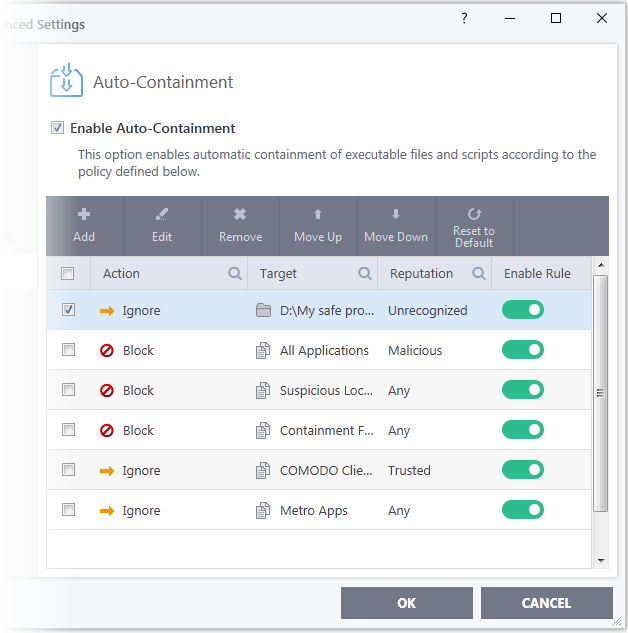
The new rule will be listed in the 'Auto-Containment' screen. Make sure to keep this rule above all other rules for unrecognized files.
Alternatively…
1. Assign
a 'Trusted' rating to the file in the File
List interface.
2. Digitally
sign your files with a code signing certificate from a trusted CA
then manually add your organization to the Vendor List as trusted.
3. Disable auto-containment by de-selecting the 'Enable Auto-Containment' check box in the 'Auto-containment' settings panel. Not recommended.
See Unknown Files: The Scanning Processes, for more details on auto-containment process.



