Trusted Vendors
There are three basic methods in which an application can be treated as safe.
- It is on the Comodo safe list (a global white-list of trusted software)
- It is signed by one of the vendors in the 'Trusted Software Vendor List' (TSVL)
- The file was manually added to 'Trusted Applications' by the user
Software publishers can get their signatures added to the TSVL by contacting Comodo with their software details. Click here to read more about this.
The
'Trusted Vendors' area in the settings interface allows you to view
the list of Trusted Vendors added to CCAV by default and allows you
to add or remove Trusted Vendors.
- Note – The trusted vendor list is periodically updated by Comodo during program updates. You disable the list update in 'Settings' > 'File Rating' > 'File Rating Settings'.
To open the 'Trusted Vendors' interface
- Click 'Settings' at the top-left of the CCAV home screen
- Click
'File Rating' > 'Trusted Vendors' on the left
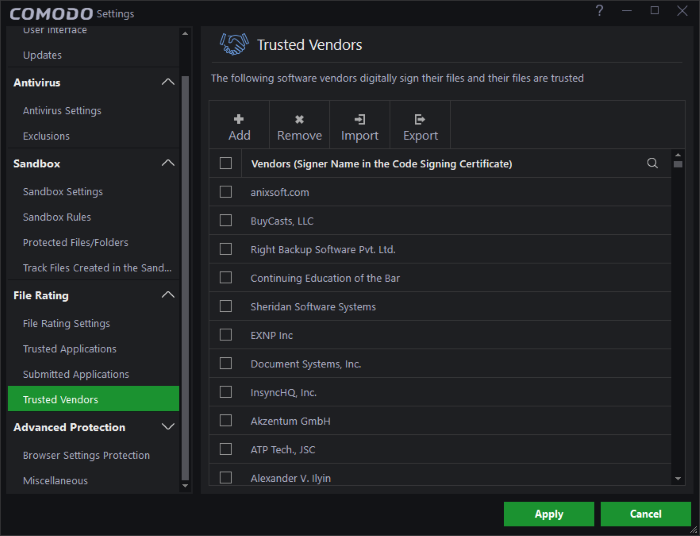
You
can search for specific vendor(s) from the list by clicking the
search icon  in the table header and entering the name of the vendor in part or
full.
in the table header and entering the name of the vendor in part or
full.
Many software vendors digitally sign their software with a code signing certificate. This practice helps end-users to verify:
-
Content Source: The software they are downloading and are about to install really comes from the publisher that signed it.
-
Content Integrity: That the software they are downloading and are about to install has not be modified or corrupted since it was signed.
In short, users benefit if software is digitally signed because they know who published the software and that the code hasn't been tampered with - that they are downloading and installing the genuine software.
The 'Vendors' that digitally sign the software to attest to it's probity are the software publishers. These are the company names you see listed in the graphic above.
However, companies can't just 'sign' their own software and expect it to be trusted. This is why each code signing certificate is counter-signed by an organization called a 'Trusted Certificate Authority'. 'Comodo CA Limited' and 'Symantec' are two examples of a Trusted CA's and are authorized to counter-sign 3rd party software. This counter-signature is critical to the trust process and a Trusted CA only counter-signs a vendor's certificate after it has conducted detailed checks that the vendor is a legitimate company.
If a file is signed by a 'Trusted Software Vendor' then it will be automatically trusted by Comodo Cloud Antivirus (if you would like to read more about code signing certificates, see http://www.instantssl.com/code-signing/).
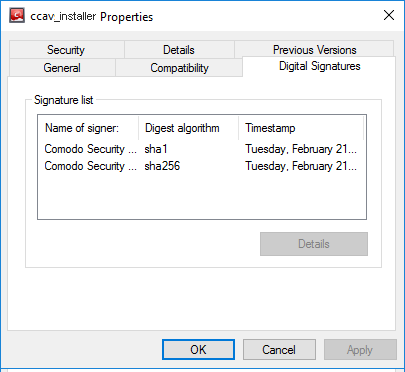
One way of telling whether an executable file has been digitally signed is checking the properties of the .exe file in question. For example, the main program executable for Comodo Cloud Antivirus is called 'ccav.exe' and has been digitally signed.
- Browse to the (default) installation directory of CCAV.
- Right click on the file 'ccav_installer.exe'.
- Select 'Properties' from the menu.
- Click the tab 'Digital Signatures (if there is no such tab then the software has not been signed).
This displays the name of the CA that signed the software as shown below:
- Select the CA and click the 'Details' button to view digital signature information.
- Click 'View Certificate' to inspect the actual code signing certificate (see below):
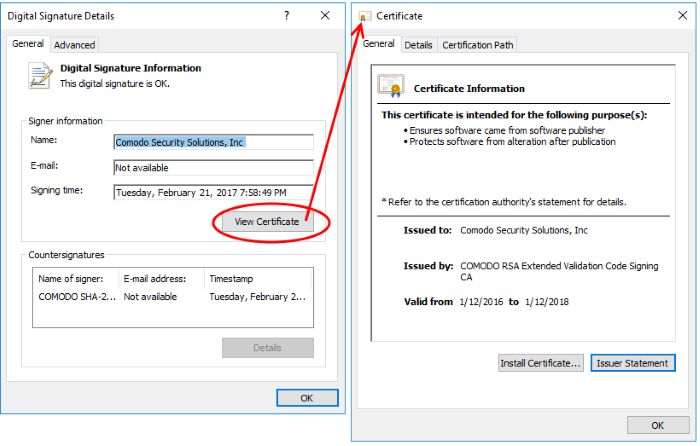
It should be noted that the example above is a special case which may need clarifying due to the similarity of the company names. 'Comodo Security Solutions' is the company that makes 'Comodo Cloud Antivirus' and is the signer of the executable. 'Comodo CA Limited' is the trusted certificate authority that counter-signed the software so that it is recognized by major operating systems (see the 'Countersignatures' box).
Adding and Defining a User-Trusted Vendor
A software vendor can be added to the local 'Trusted Software Vendors' list by reading the vendor's signature from an executable file on your local drive.
- Click the 'Add' button at the top of the interface
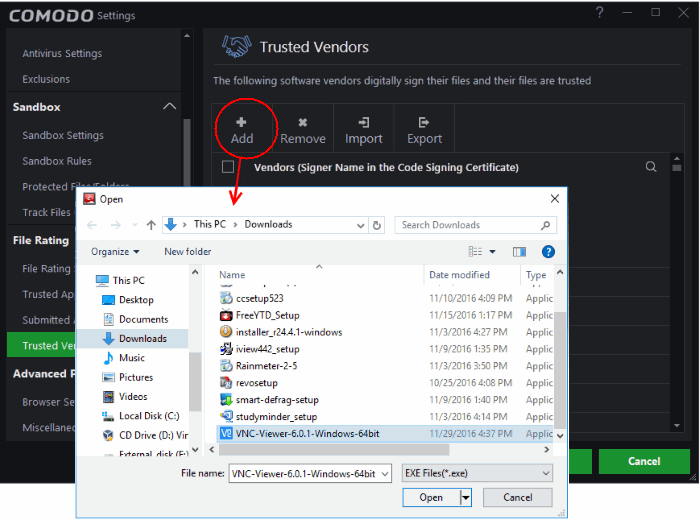
- Navigate to the location of the executable your local drive. In the example above, we are adding the executable 'VNC-Viewer-6.2.0-Windows-64bit.exe'.
- Click 'Apply' for your settings to take effect.
On clicking 'Open', CCAV checks that the .exe file is signed by the vendor and counter-signed by a Trusted CA. If so, the vendor (software signer) is added to the Trusted Vendor list (TVL):
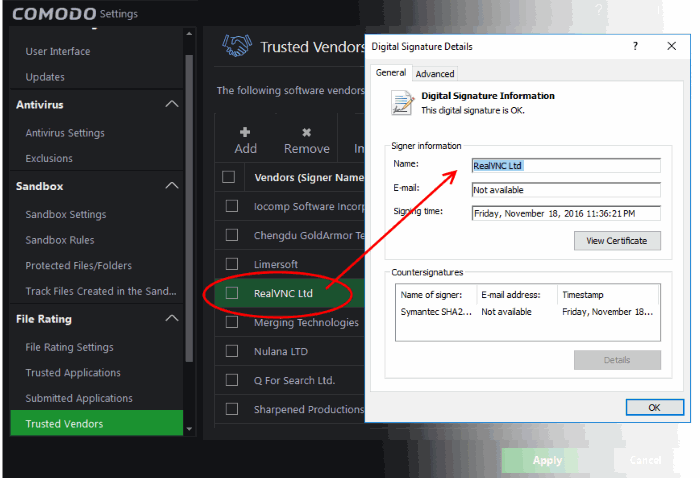
In the example above, CCAV was able to verify and trust the vendor signature on 'VNC-Viewer-6.2.0-Windows-64bit.exe' because it had been counter-signed by the trusted CA 'Symantec'. The software signer 'RealVNC LTD' is now a 'Trusted Software Vendor' and is added to the list. All future software that is signed by the vendor 'RealVNC LTD' is automatically added to the Comodo Trusted Vendor list.
If
CCAV cannot verify that the software certificate is signed by a
Trusted CA then it does not add the software vendor to the list of
'Trusted Vendors'.
|
Note: The 'Trusted Software Vendors' list displays two types of software vendors:
|
Remove vendor(s) from the list
- Select the target vendors and click 'Remove' at the top
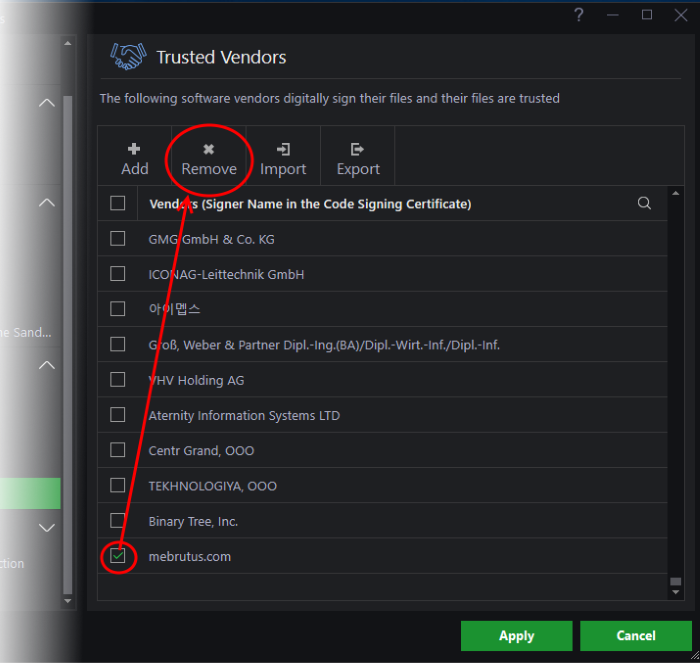
- The vendors will be removed from the list.
- Removed vendors will not be re-enabled during the next list updates from Comodo.
Import vendors from a csv file
- You can import your own trusted vendors into the list from a csv file
- Each vendor must be on a separate line
- To import from a csv file, click 'Import' at the top and select the file
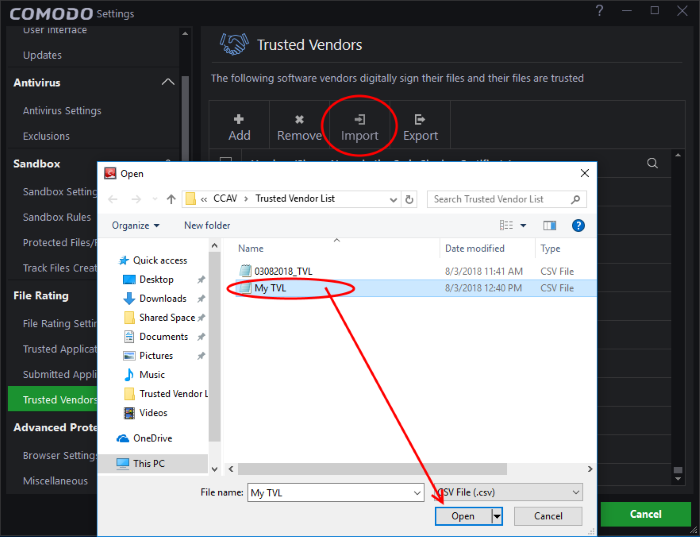
- Click 'Open'
- Click 'OK' to close the dialog.
- You can export the local trusted vendor list as a csv file for future use if required
- Click 'Export' at the top
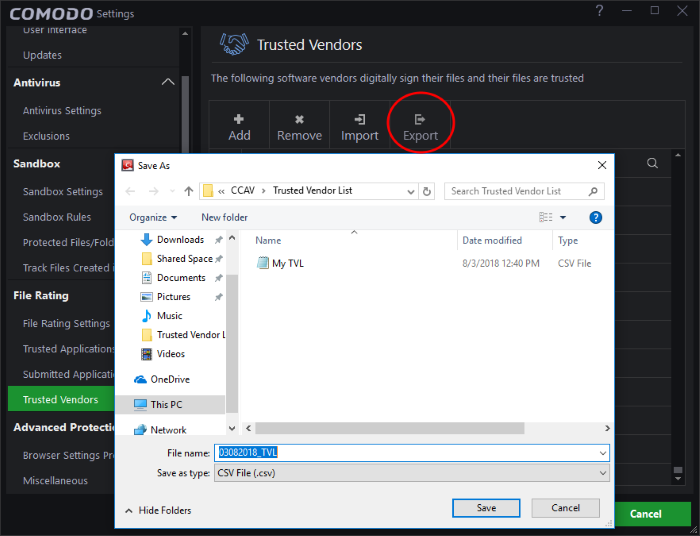
- Navigate to your preferred location and click 'Save'
A confirmation message will be shown:
- Click 'OK' to close the dialog.
The Trusted Vendor Program for Software Developers
Software vendors can have their software added to the default 'Trusted Vendor List' that is shipped with Comodo Cloud Antivirus. This service is free of cost and is also open to vendors that have used code signing certificates from any Certificate Authority. Upon adding the software to the Trusted Vendor list, CCAV automatically trusts the software and does not generate any warnings or alerts on installation or use of the software.
The vendors have to apply for inclusion in the Trusted Vendors list through the sign-up form at http://internetsecurity.comodo.com/trustedvendor/signup.php and make sure that the software can be downloaded by our technicians. Our technicians check whether:
- The software is signed with a valid code signing certificate from a trusted CA;
-
The software does not contain any threats that harm a user's PC; before adding it to the default Trusted Vendor list of the next release of CCAV.
More details are available at http://internetsecurity.comodo.com/trustedvendor/overview.php.



