Trusted Certificate Authority Change Logs
- Click 'Tasks' > 'Advanced Tasks' > 'View Logs'
OR
- Click ‘Logs’ in advanced view of the CIS home screen
- Select 'Trusted Certificate Authorities Changes' from the drop-down at upper-left.
Root
certificates are a critical part of online security. Your internet
browser relies on them to verify that you are connected to the site
you think you are connected to.
If a fake root certificate was to find its way into your browser's trusted certificate store (TCS), then you could be tricked into connecting to a fraudulent server instead of the site you intended.
Comodo Internet Security checks the trust rating of all root certificates in your browser's TCS to ensure they are legitimate. It runs this check during the following scans:
- Rating scan - Click 'Scan' > 'Rating Scan'
- Full scan - Click 'Scan' > 'Full Scan'
- Custom scan profiles that include the certificate store. Click 'Scan' > 'Custom Scan' > 'More Scan Options'
- Unrecognized and self-signed certificates are marked as 'Untrusted'.
- You can choose to trust the certificate or remove it. An example is shown below:
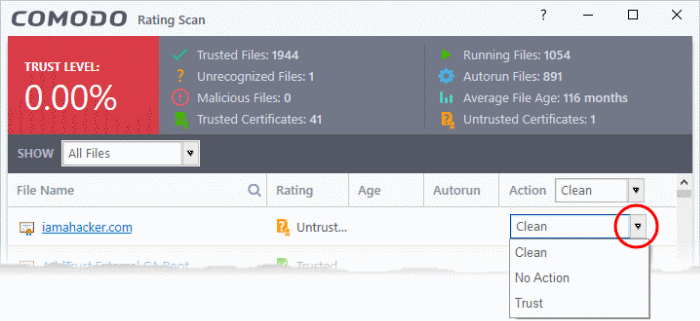
- Clean - Removes the certificate from the store
- Trust - Assigns 'Trusted' status to the certificate. The certificate is excluded from future scans.
- No Action - The certificate keeps its untrusted status, but is not deleted.
- Any changes to the certificate store are logged in 'Trusted Certificate Authorities Changes'.
|
Background: There are two types of certificate involved when you connect to a secure website:
|
View 'Trusted Root Certificate Authorities Changes' logs
- Click 'Tasks' on the CIS home screen
- Click 'Advanced Tasks' > 'View Logs'
- Select 'Trusted Root Certificate Authorities Changes' from the 'Show' drop-down
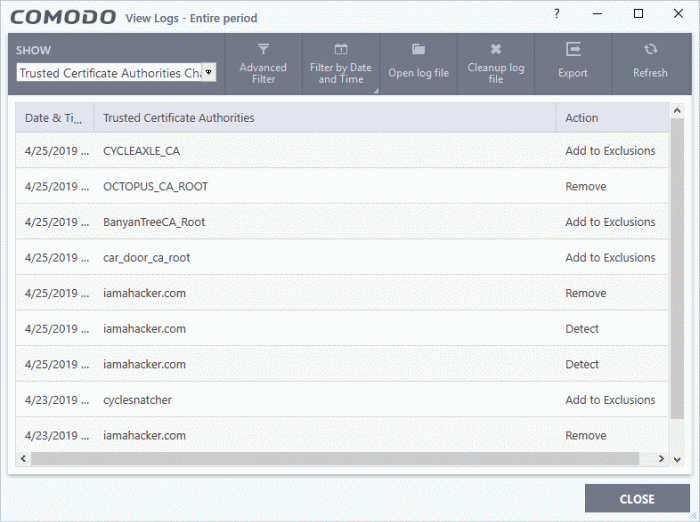
- Date & Time - When the change event occurred
- Trusted Certificate Authorities - The name of the CA who issued the untrusted certificate
- Action – Whether the user chose to trust, remove or ignore the certificate
Click any column header to sort the entries in ascending / descending order.



