Manage Blocked Items
- A file may be blocked by any one of the antivirus, containment, firewall or HIPS components
- The unblock applications screen lets you review all blocked files and release those you consider safe. You can also assign a new trust rating to a blocked file. CIS will handle the file based on the rating in future
- If you unblock an item, CIS will automatically make changes to allow it to run in future. The change made depends on the component which blocked the file:
- Antivirus - The item is added to the scan exclusion list. Click 'Settings' > 'Advanced Protection' > 'Scan Exclusions' to manage this list
- Firewall - An 'Allow' rule is added to application rules. Click 'Settings' > 'Firewall' > 'Application rules' to manage these rules
- Containment – An 'Ignore' rule is added to containment rules. Click 'Settings' > 'Containment' > 'Auto-containment' to manage these rules
- HIPS - An 'Allow' rule is added to HIPS Rules. Click 'Settings' > 'HIPS' > 'HIPS Rules' to manage these rules
- You can unblock from all components, or only the component that blocked it.
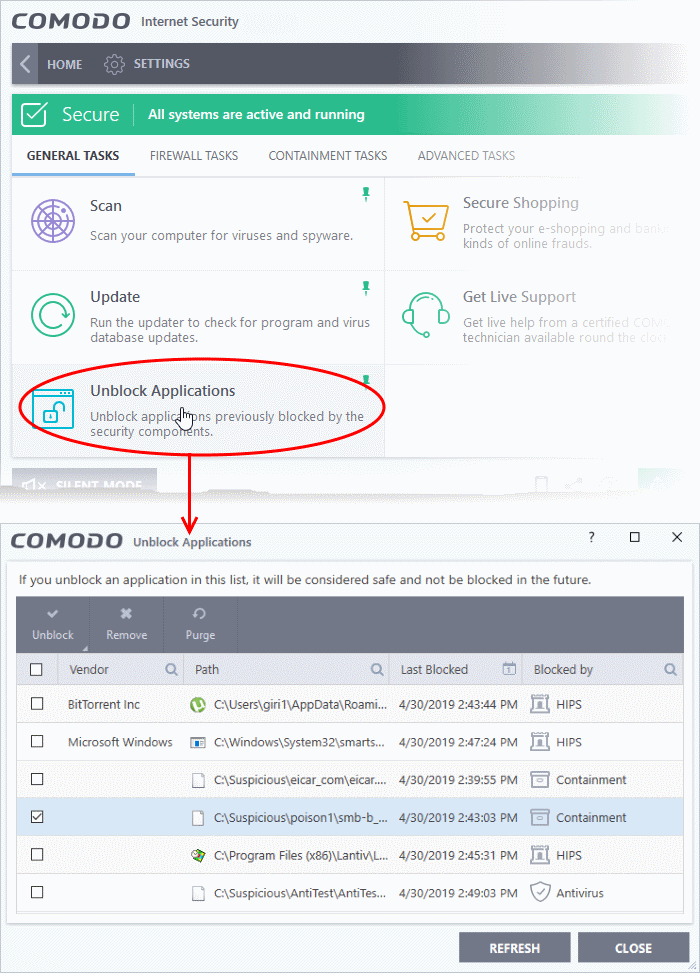
- Click 'Tasks' > 'General Tasks' tab
- Click the 'Unblock Applications' tile
|
Unblock Applications – Column Descriptions |
|
|---|---|
|
Column Header |
Description |
|
Vendor |
The publisher of the blocked application. |
|
Path |
The install location of the blocked application. |
|
Last Blocked |
Date and time the application was most recently stopped from running. |
|
Blocked by |
The security component that stopped the application from running. Can be 'Antivirus', 'HIPS', 'Firewall' or 'Containment'. |
- Click any column header to sort items in alphabetical order
The interface allows you to:
- Click 'Tasks'> 'General Tasks' tab
- Click the 'Unblock Applications' tile
- Select an item or items from the list
- Click
'Unblock' at the top-right
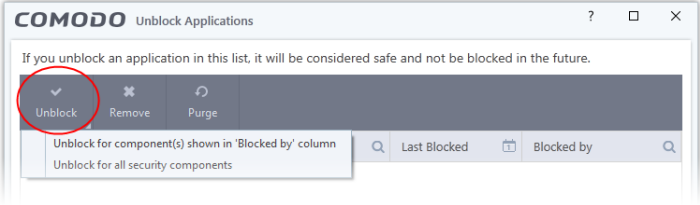
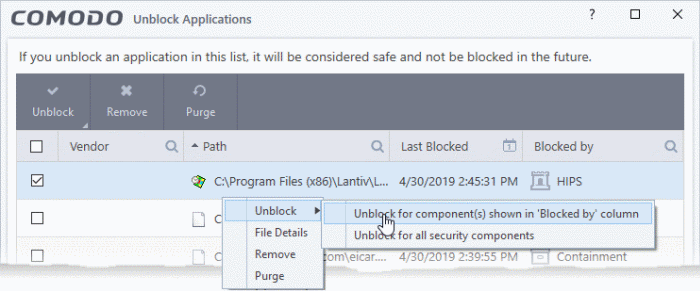
- Unblock for component(s) shown in 'Blocked by' column - Item only be released from the security component that blocked it.
- Unblock for all security components - Item will be released from all security components
See the intro for a list of the rules that are created per-component for unblocked items.
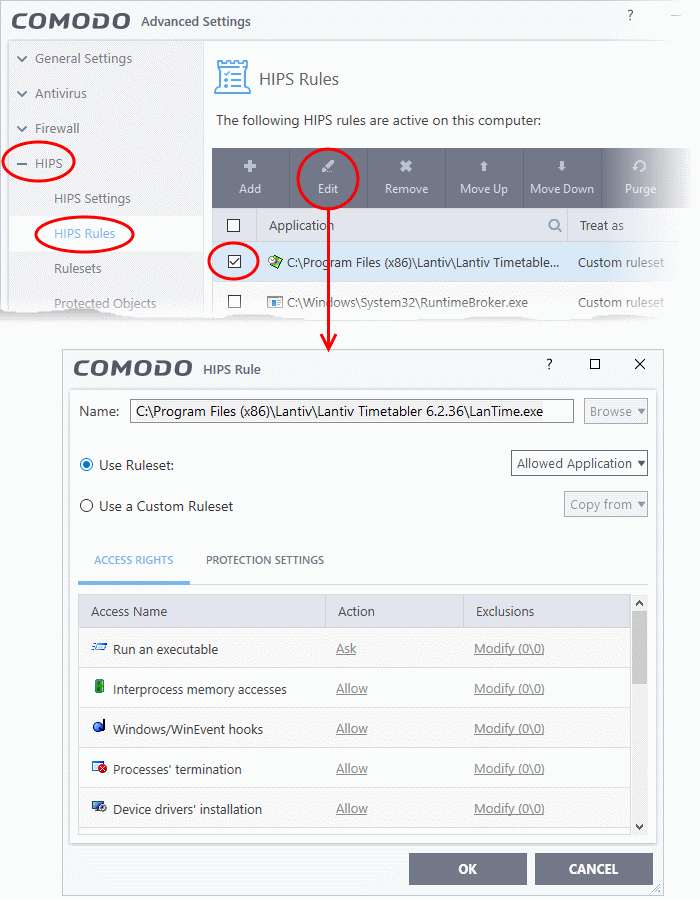
Example:
In the example shown below, 'LanTime.exe' was blocked by HIPS.
- If you unblock the file, an 'Allowed Application' rule is created in HIPS
- To view the rule:
- Click 'Settings' > 'HIPS' > 'HIPS Rules'
- Select the application and click 'Edit':
View items details and assign a trust rating
- Click 'Tasks'> 'General Tasks' tab
- Click the 'Unblock Applications' tile
- Right-click on an item and choose 'File Details' from the context sensitive menu
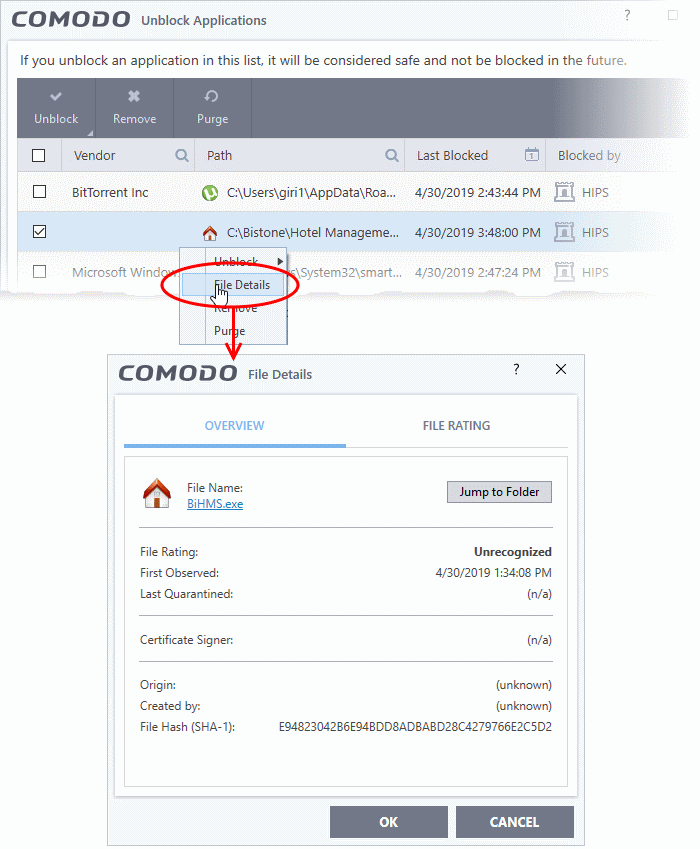
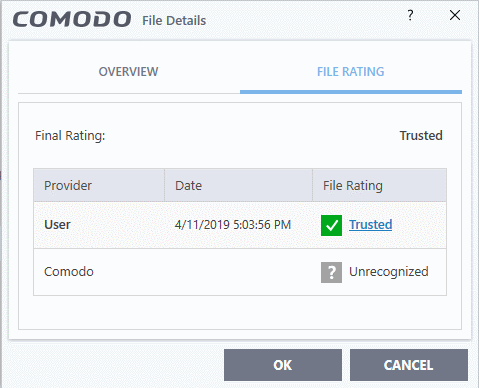
The 'File Details' dialog has two tabs:
The 'Overview' tab shows general details such as the file rating, discovery date, hash value and publisher (signer):
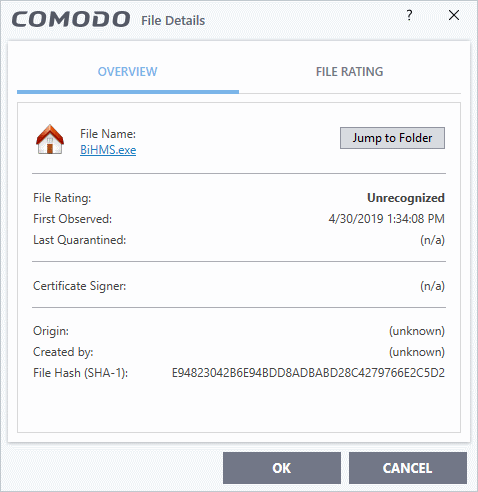
- Click the file name to open the Windows 'File Properties' dialog
- Click 'Jump to folder' to open the folder containing the file in Windows Explorer, with the respective file selected
- Shows the file's current trust rating from Comodo and lets you set your own rating:
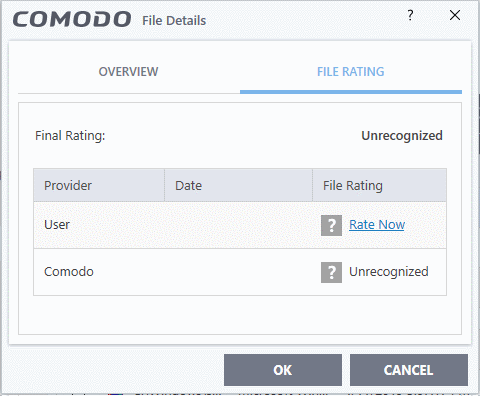
- Click the 'Rate Now' link beside 'User' and choose the rating from the drop-down
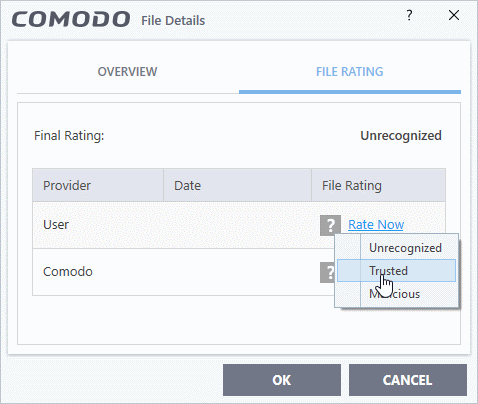
The options available are:
- Trusted - The file is considered safe and allowed to run without any alerts
- Unrecognized – The file is neither definitely safe nor definitely malicious. The files privileges are determined by your HIPS settings ('Settings' > 'HIPS')
- Malicious - The file will be deleted or placed in quarantine
- Click 'OK'
- Your new rating is applied to the file as a 'User Rating'
- Click 'Settings' > 'File Rating' > 'File List' to view the file and its rating
Remove an application from the 'Unblock Applications' list
- Click 'Tasks'> 'General Tasks' tab
- Click the 'Unblock Applications' tile
- Select an item from the list
- Click the 'Remove' button at the top
- Alternatively, right-click on an item and choose 'Remove' from the context sensitive menu.
Purge Files from the 'Unblock Applications' list
CIS checks whether the files in the list are still installed at the path stated. Files that are no longer present are removed from the list.
- Click 'Tasks'> 'General Tasks' tab
- Click the 'Unblock Applications' tile
- Click the 'Purge' button at the top-right
- Alternatively, right-click on an item and choose 'Purge' from the context sensitive menu.



