Create, Schedule and Run a Custom Scan
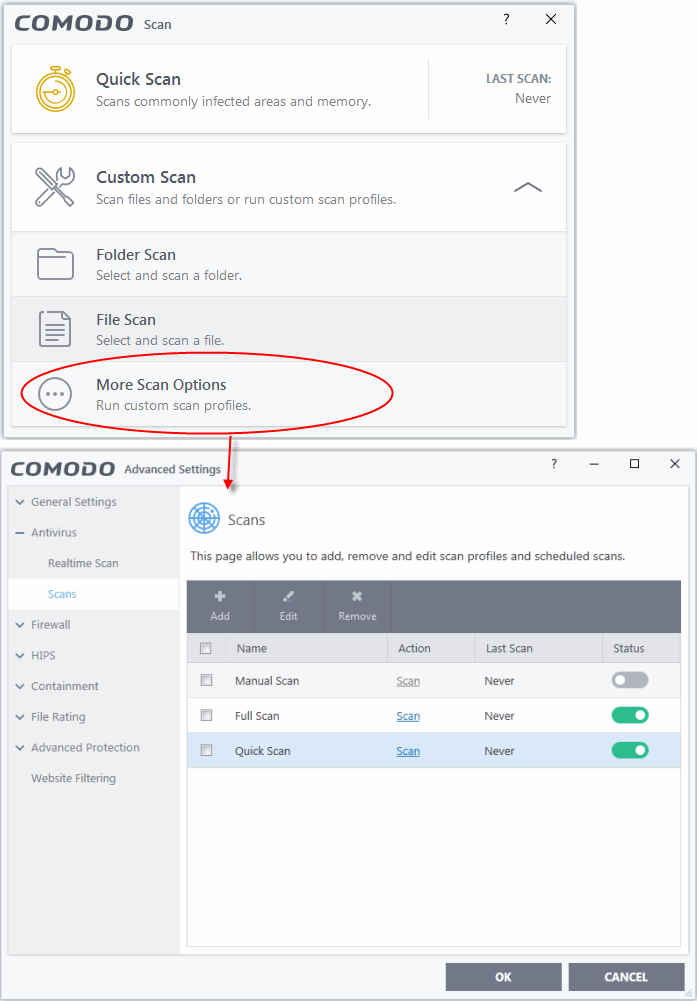
Click 'Tasks' > 'General Tasks' > 'Scan' > 'Custom Scan' > 'More Scan Options'
- A custom scan profile lets you configure your own scan with your own scan settings.
- You can define exactly which files and folders to scan, what time they should be scanned, and configure scan settings.
- Once saved, you can select and run your custom scan at any time in the scans interface.
- See the following for more help:
- Click the 'Scan' tile on the CIS home screen (click here for alternative ways to open the 'Scan' interface)
- Select 'Custom Scan' then 'More Scan Options'
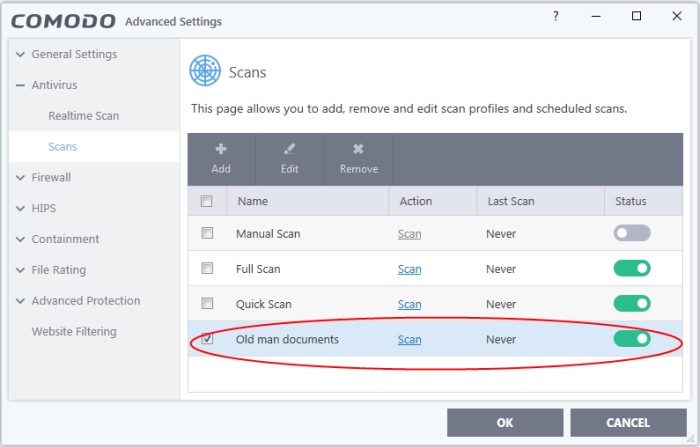
The 'Scans' page shows pre-defined and user created scan profiles. You can create and manage new profiles in this page:
|
Tip: You can also get to this screen by clicking 'Settings' > 'Antivirus' > 'Scans'. |
- Click 'Add' to create a new custom scan profile.
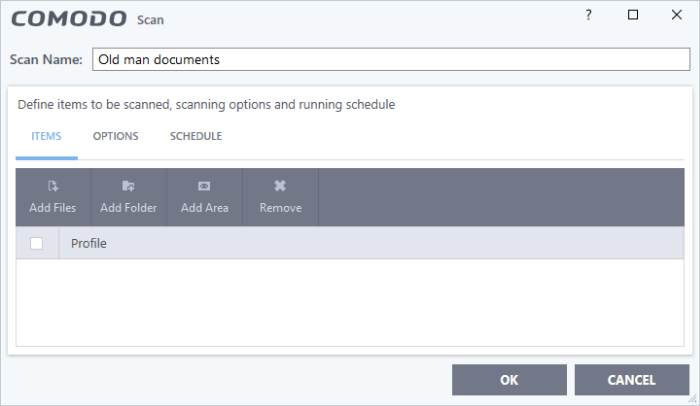
- First, create a name for the profile. The next steps are:
- Click the 'Items' button at the top of the scan interface.
- Add File - Add individual files to the profile. Click the 'Add Files' button and browse to the file you want to include.
- Add Folder - Add entire folders to the profile. Click the 'Add Folder' button and choose the folder you want to include. All files in the folder are covered by the scan.
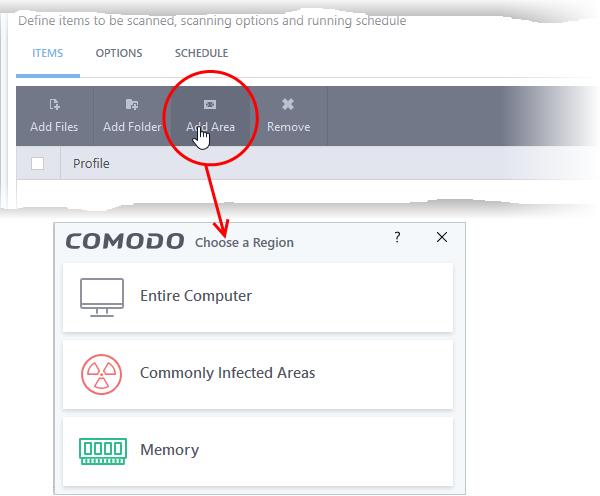
- Add Area – Scan a specific region. The choices are 'Full Computer', 'Commonly Infected Areas', 'System Memory' and 'Trusted Root Certificate Store'. See screenshot below:
- Repeat the process to add more items to the profile. You can mix-and-match files, folders and areas in your custom scan.
- Click 'Options' button at the top of the scan interface
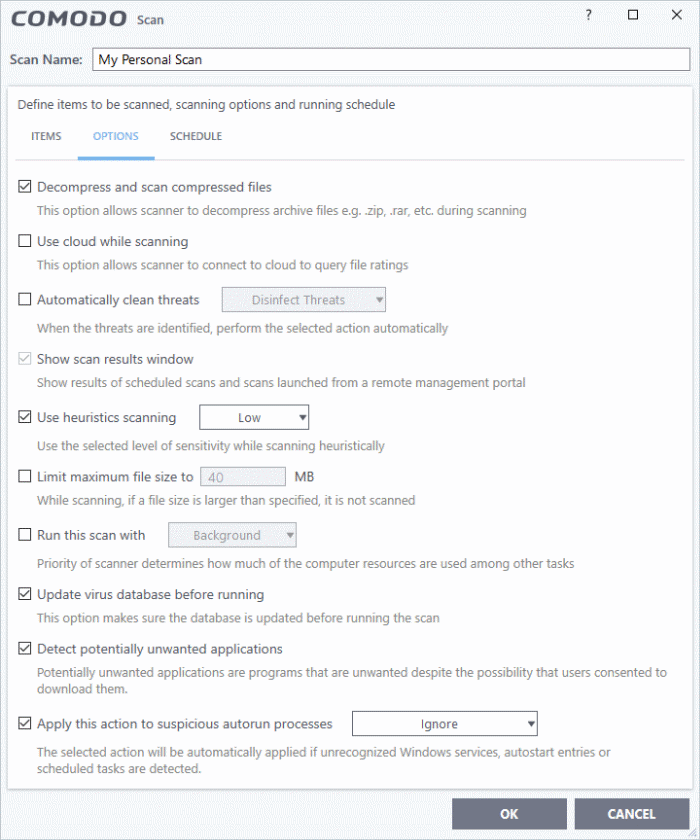
- Decompress and scan compressed files - The scan will include archive files such as .ZIP and .RAR files. Supported formats include RAR, WinRAR, ZIP, WinZIP ARJ, WinARJ and CAB archives(Default = Enabled) .
- Use cloud while scanning - Improves accuracy by augmenting the local scan with an online look-up of Comodo's latest virus database. This means CIS can detect the latest malware even if your virus database is out-dated (Default = Disabled).
- Automatically clean threats - Select whether or not CIS should automatically remove any malware found by the scan.
- Disabled = Results are shown at the end of the scan with a list of any identified threats. You can manually deal with each threat in the results screen. See Process infected files for guidance on manually handling detected threats. (Default)
- Enabled = Threats are handled automatically. Choose the action that CIS should automatically take:
- Quarantine Threats - Malicious items will be moved to quarantine. You can review quarantined items and delete them permanently or restore them. See Manage Quarantined Items for more details.
- Disinfect Threats - If a disinfection routine exists, CIS will remove the virus and keep the original file. If not, the file will be quarantined.
- Show scan results window - You will see a summary of results at the end of the scan. This includes the number of objects scanned and the number of threats found.
- Use heuristics scanning - Select whether or not heuristic techniques should be used in scans on this profile. You can also set the heuristic sensitivity level. (Default = Enabled).
- Background. Heuristics is a technology that analyzes a file to see if it contains code typical of a virus. It is about detecting 'virus-like' attributes rather than looking for a signature which exactly matches a signature on the blacklist. This means CIS can detect brand new threats that are not even in the virus database.
If enabled, please select a sensitivity level. The sensitivity level determines how likely it is that heuristics will decide a file is malware:
- Low - Least likely to decide that an unknown file is malware. Generates the fewest alerts.
Despite the name, this setting combines a very high level of protection with a low rate of false positives. Comodo recommends this setting for most users. (Default)
- Medium - Detects unknown threats with greater sensitivity than the low setting, but with a corresponding rise in possible false positives.
- High - Highest sensitivity to detecting unknown threats. This also raises the possibility of more alerts and false positives.
- Limit maximum file size to - Specify the largest file size that the antivirus should scan. CIS will not scan files bigger than the size specified here (Default = 40 MB).
- Run this scan with - If enabled, you can set the priority of scans on this profile The available options are:
- High
- Normal
- Low
- Background.
- Update virus database before running - CIS checks for and downloads the latest virus signatures before starting a scan (Default = Enabled).
- Detect potentially unwanted applications - The antivirus also scans for applications that (i) a user may or may not be aware is installed on their computer and (ii) may contain functionality and objectives that are not clear to the user. Example PUA's include adware and browser toolbars. PUA's are often bundled as an additional utility when installing another piece of software. Unlike malware, many PUA's are legitimate pieces of software with their own EULA agreements. However, the true functionality of the utility might not have been made clear to the end-user at the time of installation. For example, a browser toolbar may also contain code that tracks your activity on the internet (Default = Enabled).
- Apply this action to suspicious autorun processes - Specify how CIS should handle unrecognized auto-run items, Windows services and scheduled tasks.
- Ignore - The item is allowed to run (Default)
- Terminate - CIS stops the process / service
- Terminate and Disable - Auto-run processes are stopped and the corresponding auto-run entry removed. In the case of a service, CIS disables the service.
- Quarantine and Disable - Auto-run processes are quarantined and the corresponding auto-run entry removed. In the case of a service, CIS disables the service.
Note 1 - This setting only protects the registry during the on-demand scan itself. To monitor the registry at all times, go to 'Advanced Settings' > 'Advanced Protection' > 'Miscellaneous'.
Note 2 - CIS runs script analysis on certain applications to protect their registry records. You can manage these applications in 'Advanced Settings' > 'Advanced Protection' > 'Script Analysis' > 'Autorun Scans'.
See 'Autorun Scans' in Script Analysis Settings for more details
Schedule the scan
- Click 'Schedule' at the top of the 'Scan' interface.
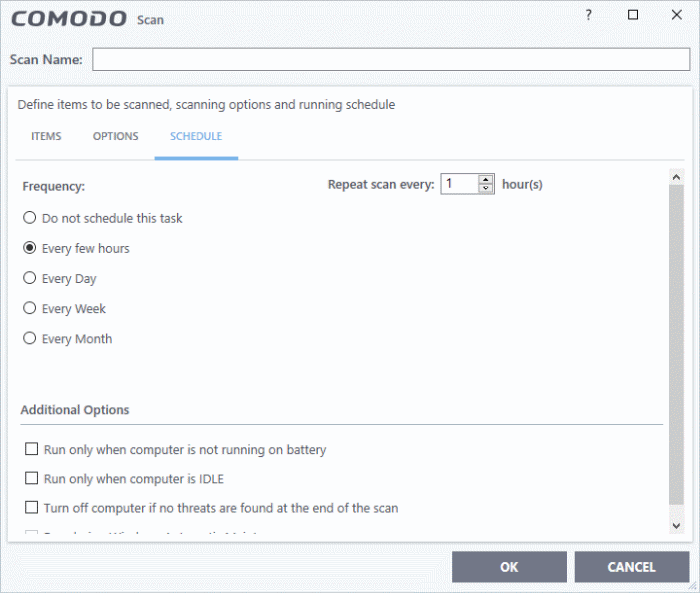
Schedule options are:
- Do not schedule this task - The scan profile will be created but will not run automatically. The profile will be available for manual, on-demand scans.
- Every few hours - Run the scan at the interval you specify in 'Repeat scan every NN hour(s)'
- Every Day - Run the scan every day at the time specified in the 'Start Time' field.
- Every Week - Run the scan every day on the days and time you specify. You can select the days of the week by clicking on them.
- Every Month – Scans the areas defined in the profile on the date(s) specified in 'Days of the month' field at the time specified in the 'Start Time' field. You can select the dates of the month by clicking on them.
- Run only when computer is not running on battery – The scan only runs when the computer is plugged into the power supply. This option is useful when you are using a laptop or any other battery driven portable computer.
- Run only when computer is IDLE - The scan will run only if the computer is an idle state at the scheduled time. Select this option if you do not want the scan to disturb you while you are using your computer.
- Turn off computer if no threats are found at the end of the scan - Will turn off your computer if no threats are found during the scan. This is useful when you are scheduling scans to run at nights.
- Run during Windows Maintenance - Only available for Windows 8 and later. Select this option if you want the scan to run when Windows enters into automatic maintenance mode. The scan will run at maintenance time in addition to the configured schedule.
- The option 'Run during Windows Maintenance' will be available only if 'Automatically Clean Threats' is enabled for the scan profile under the 'Options' tab. See the explanation of Automatically Clean Threats above.
|
Note: The scheduled scan will run only if the scan profile is enabled. Use the switch in the 'Status' column to toggle a profile on or off. |
- Click 'OK' to save the profile.
The profile will be available for deployment in future.
- Click 'Tasks' > 'General Tasks' > 'Scans'
- Click 'Custom Scan' and select 'More Scan Options'
The 'Scans' pane will open with a list of existing scan profiles:
- Click the 'Scan' link in the 'Action' column of profile you wish to run:
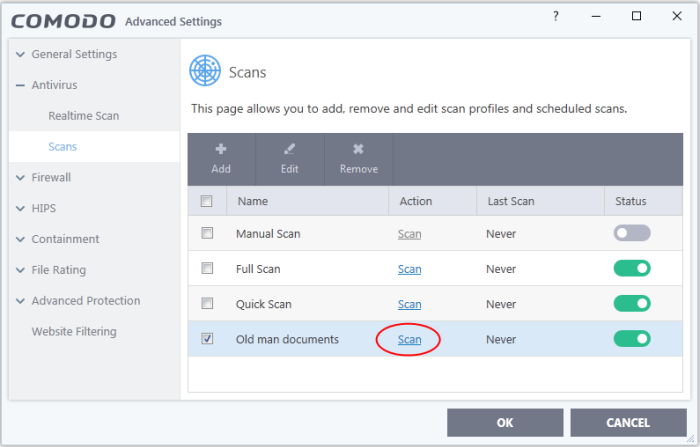
- The scan will start immediately.
Results are displayed afterwards:
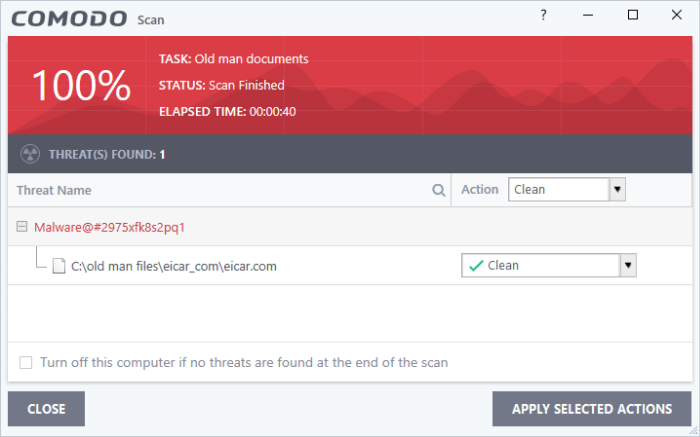
The results screen shows the number of detected threats and lets you decide what to do with them. You can clean, move to quarantine or ignore the threat. See Process the infected files if you need help to decide.



