The Home Screen
You can switch between the 'Home' screen and the 'Tasks' interface by clicking the 'Home/Tasks' button at the top left of the interface:
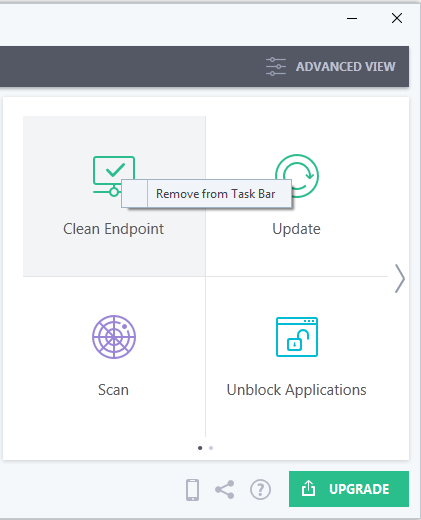
The home screen itself is available
in two formats, 'Basic'
view and 'Advanced'
view. Use the button at the top-right of the home screen to switch between them.
- Basic View presents a simple, easy to understand interface that allows users to quickly launch key tasks and gain an immediate overview of the security of their computer.
- The large 'security information' tile on the left provides an at-a-glance view of overall system security and allows you to run an appropriate CIS task if threats are found.
- The 'Manage Protection' button below the 'security information' tile allows you to turn security components on or off as well as open the component's advanced settings interface.
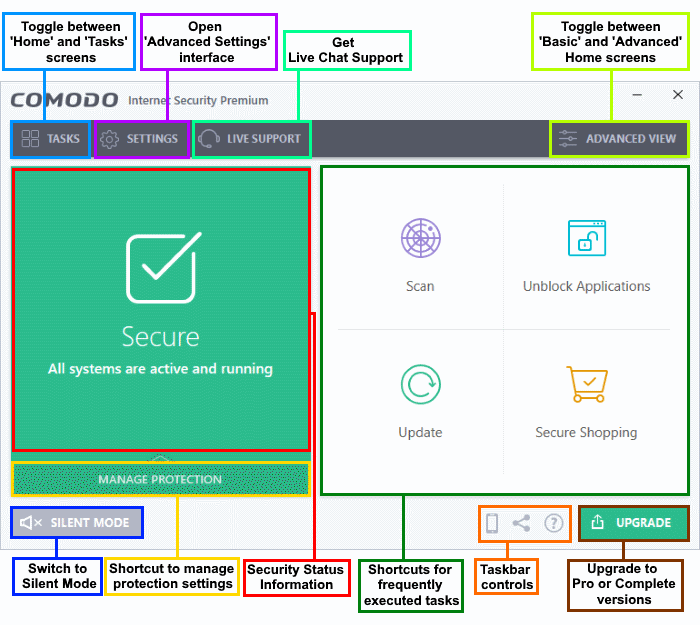
The security information tile on the left will inform you if any component is disabled or any if other problems are found:
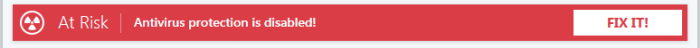
You can easily rectify the issue by clicking the 'FIX IT' button. CIS will automatically take necessary actions to resolve the problem. 'Silent Mode' and 'Help Window' are common to both home and tasks screen.
From the 'Basic View' of the home screen you can:
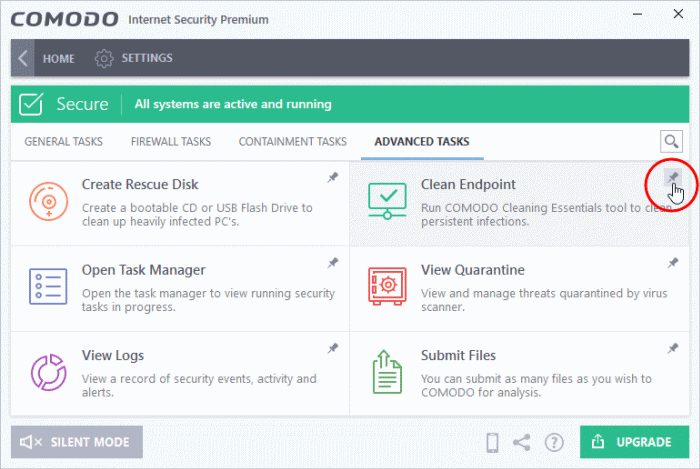
The tasks pane on the right contains a set of shortcuts which will launch common tasks with a single click. The handles at the right and left allow you to scroll through the tasks pane.
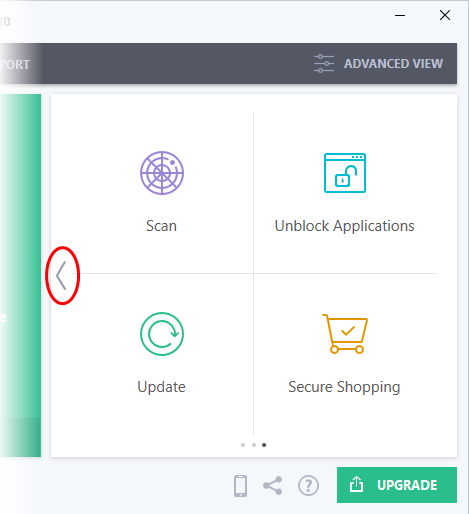
You can add tasks to this pane as follows:
- Open the 'Tasks' interface (click the button at top left to switch between the tasks and home screens).
- Click any of the 'General', 'Firewall', 'Containment' or 'Advanced' tabs
- Right-click on the task you wish to add then click 'Add to Task Bar':
-
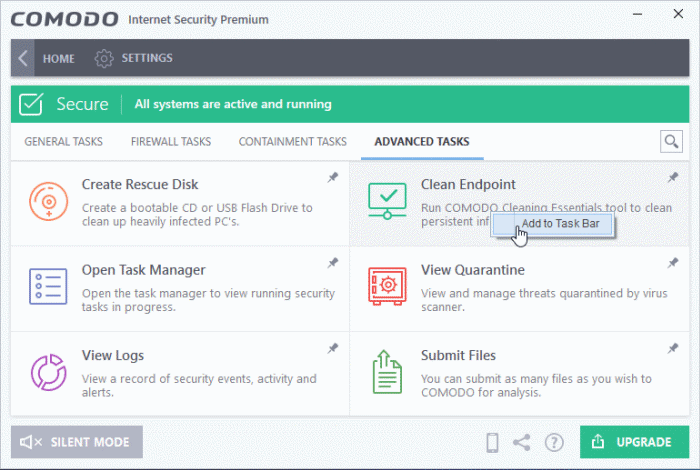
Alternatively, you can add task shortcuts to the home screen by clicking the 'pin'
 button at the top-right of any tile:
button at the top-right of any tile:
- The selected task will be added to
the tasks pane.
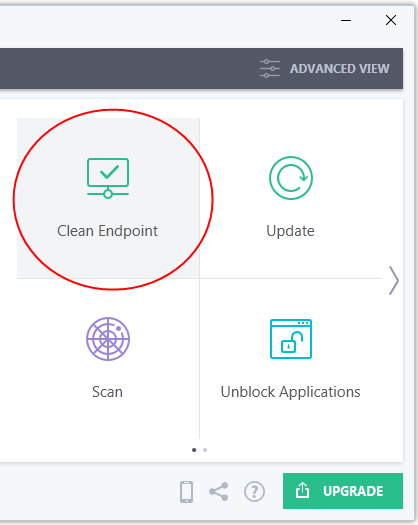
- To remove a task shortcut from the pane, right click on it and choose 'Remove from Task Bar'.
- Click the 'Manage Protection' button on the home screen to enable or disable various security components.
- Click on any component name to open its dedicated settings screen.
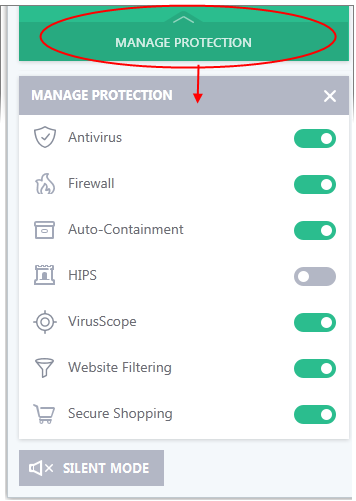
- Use the switch on the right to turn the protection on or off
- Click a component name on the left to open its 'Advanced Settings' screen
See the following sections for more details about each of the protection settings:
You can seek
the help of GeekBuddy technicians anytime if you require support
related to CIS or your computer in general.
- Click the 'Live Support' link to open the 'Comodo GeekBuddy' chat interface.
- Begin typing your problem. Our technician will attempt to answer any questions you have.
See 'Comodo
GeekBuddy' for more details about live help.
The 'Advanced View' of the home screen provides a more finely-detailed view of the security status of each major security component.
- Click the 'Advanced View' button at the top-right to switch to advanced view from basic view:
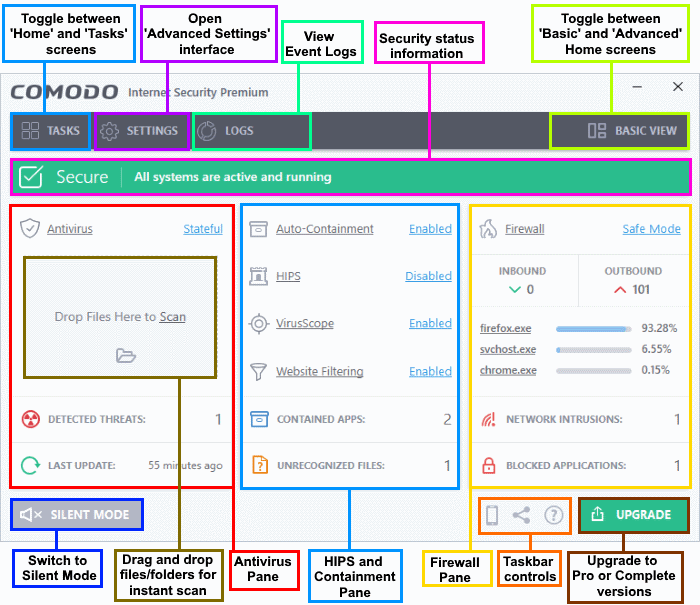
The following sections explain more about each pane:
The antivirus pane lets you configure scan mode, instantly scan files and folders, and view virus database and log information.
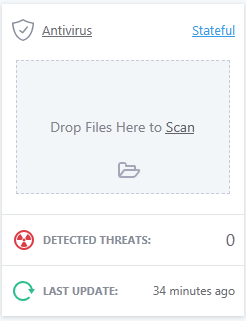
- Antivirus - The current security mode of the real-time antivirus scanner.
- Click on the mode text to view and change mode.
- Click 'Antivirus' to open the real-time scan settings interface.
- See 'Real-time Scan Settings' for more details.
- Last Update - Date of the most recent virus database update.
- Click the text link to start the updates again.
- Detected
Threats - The number of malware threats discovered so far from
the start of current session as a link.
- Click this number to open the Antivirus Logs panel.
- Drop
Files to Scan - Drag-and-drop files,
folders or drives into this box to instantly scan them. See
'Instantly
Scan Files and Folders' for more details.
This panel lets you quickly configure containment, host-intrusion, VirusScope and website filtering. The bottom of the panel shows the number of unrecognized files and contained applications.
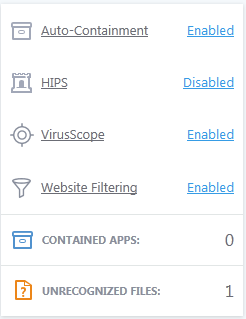
- Auto-Containment - If enabled, any files with an 'Unknown' trust rating will be automatically run in the container to prevent them from accessing other processes or your personal data. Unknown files are those that are neither 'known-malicious' nor 'known-safe'. Such files are run in the container until their true trust status can be established. Click on the security level itself to change it. Click 'Auto-Containment' to open the 'Auto-Containment Settings' interface. See 'Auto-Containment Rules' for more details.
- HIPS - Click the text of the current HIPS mode to view or modify the mode. Click the word 'HIPS' to open the 'HIPS Settings' interface. See 'HIPS Configuration' for more details.
- VirusScope - Whether VirusScope is enabled or not. Click on the security level to change it. Click the work 'VirusScope' to open the 'VirusScope' interface. See 'VirusScope Configuration' for more details.
- Contained Apps - The number of applications that are currently running inside the container.
- Click the number to view a list of all processes running in the container. See 'View Active Process List' for more details.
-
Unrecognized Files - The number of files on your system that have an 'unrecognized' trust rating. Unrecognized files are those that are neither definitely safe (whitelisted) nor definitely malicious (blacklisted). Unrecognized files should be executed in the container until Comodo provides either a trusted or a malicious rating for them.
- Click the number to open the 'File List' interface. See 'File List' for more details.
The firewall pane shows the number of inbound and outbound connections, which applications are connected to the internet, and the number of intrusion attempts blocked in the current session.
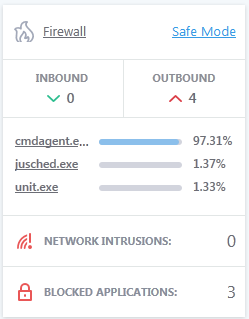
- Firewall - The current security mode of the firewall.
- Click the level itself to quickly view and modify it.
- Click on 'Firewall' to open the Firewall Settings interface. See 'Firewall Configuration' for more details.
- Inbound / Outbound Connections - A summary of currently active inbound and outbound connections to and from the system.
- Click on the numbers to see the active internet connections from your computer.
- See 'View Active Internet Connections' for more details.
- Traffic - Applications
that are currently sending or receiving data over the
network/internet.
- Click the name of any application to open the View Connections screen.
- Network Intrusions - Displays the total number of intrusion attempts blocked by firewall since the start of the current session.
- Click the number to open the Firewall Logs screen. See 'Firewall Logs' for more details.
- Blocked Applications - The number of applications that are not allowed to connect to the internet.
- Click the number to view a list of all blocked applications. See 'Configure Internet Access Rights For Applications' for more details.
- Click
the logs link to view a list of all event logs saved by CIS. See
'View
CIS Logs' for more details.
Silent mode lets use your system without interruptions or alerts from CIS. Operations that could interfere with your work are either suppressed or postponed.
In silent mode:
- HIPS/Firewall alerts are suppressed.
- AV database updates and scheduled scans are postponed until the silent mode is switched off;
- Automatic isolation of unknown applications and real-time virus detection are still functional.
Switch to Silent mode
-
Click the 'Silent Mode' bottom at the left of the 'Home' screen
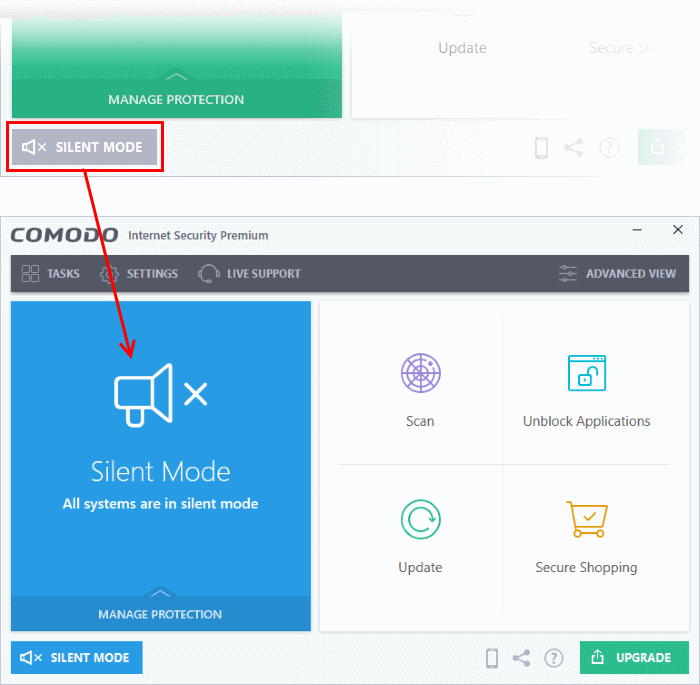
-
Deactivate 'Silent Mode' to resume alerts and notifications.
Upgrade
- Click the 'Upgrade' button to place an order for CIS Pro or CIS Complete. Pro and Complete have additional features such as cloud backup, TrustConnect, product warranty and more.



