Run a Rating Scan
Click 'Tasks' > 'General Tasks' > 'Scan' > 'Rating Scan'
- A rating scan checks the trust-rating of files and root certificates on your computer. Root certificates are used by your internet browser to validate the SSL certificates on sites you visit.
- Trust ratings are as follows:
- Trusted - The file is safe to run. The root certificate was issued by a trusted certificate authority (CA).
- Untrusted – The root certificate is not safe. It was not issued by a trusted CA and could be linked to fraud/phishing websites.
- Unrecognized – Comodo does not currently have a trust rating for the file. Unrecognized files should be run in the container to prevent them potentially attacking your computer. You can simultaneously submit them to Comodo for a trust-rating analysis.
- Malicious - The file is malware. Depending on your settings, CIS will either quarantine the file immediately or present you with disinfection options.
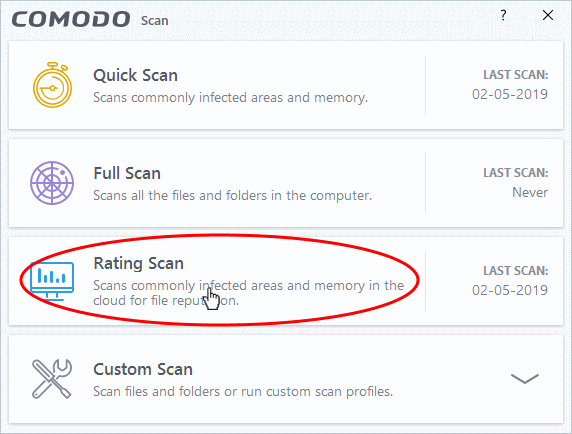
- Click the 'Scan' tile on the CIS home screen (click here for alternative ways to open the scan interface)
- Select
'Ratings Scan':
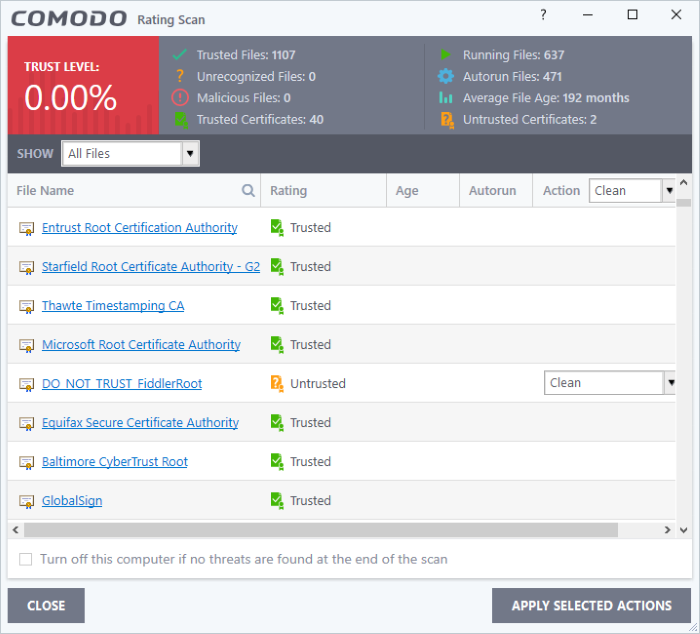
CIS will analyze all files on your computer and assign them a trust rating. File ratings are shown as follows when the scan finishes:
|
Rating Scan Results Table - Column Descriptions |
|
|---|---|
|
Column Header |
Description |
|
File Name |
The label of the scanned item. |
|
Rating |
The trust level of the file / SSL certificate as per the cloud based analysis. The possible values are:
|
|
Age |
The length of time the item has been on your computer |
|
Autorun |
Whether or not the file automatically runs without user intervention.We advise you clean or quarantine these files immediately. |
|
Action |
Select how you want to deal with the listed item. See below table: |
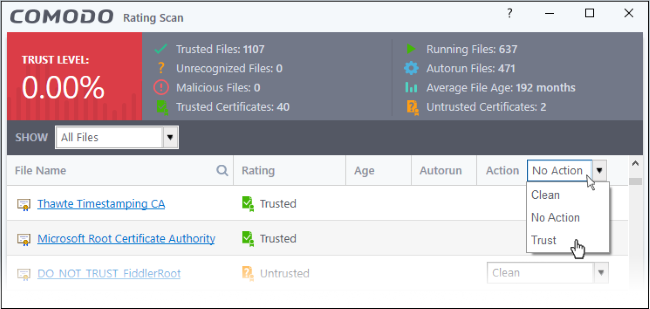
The drop-down menus on the right let you handle unrecognized and malicious items:
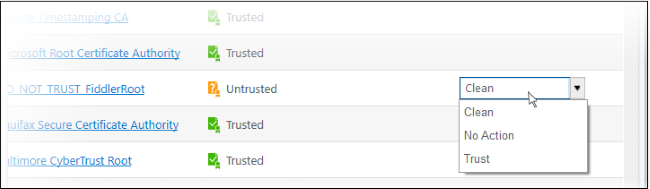
- Clean - Available only for untrusted/malicious items. The threat is placed in quarantine for your review. Click 'Tasks' > 'Advanced Tasks' > 'View Quarantine' to open this area. You can restore or permanently delete files from quarantine as required. See Manage Quarantined Items for more details.
- No Action - Ignores the warning this time only. The file or certificate is not placed in quarantine. Use this option with caution. The file/certificate will be caught again by the next rating scan you run.
- Trust - Assigns 'Trusted' rating to the item. Only select this option if you are sure the item is trustworthy.
- Files - The file is awarded trusted status in the File List ('Settings' > 'File Rating' > 'File List'). The file will be excluded from any future rating scans.
- SSL Certificates – The certificate authority (CA) who signed the certificate is awarded 'Trusted' status. CIS will allow you to connect to sites whose certificates chain to this root.
- CIS logs all actions taken in the results screen. You can view the logs at 'Tasks' > 'Advanced Tasks' > 'View Logs'.
- Files - See File List Changes Logs for more details
- SSL Certificates - See Trusted Certificate Authorities Changes Logs for more details
- Use the drop-down in the 'Action' column header to apply your choice to all listed files: