Block / Allow Specific Websites to Specific Users
Comodo Internet Security allows you to block or allow access to specific websites, or groups of websites, to different users. This involves two steps:
2. Click 'Website Filtering' > 'Categories'
3. Click
'Add' > 'Add Category':
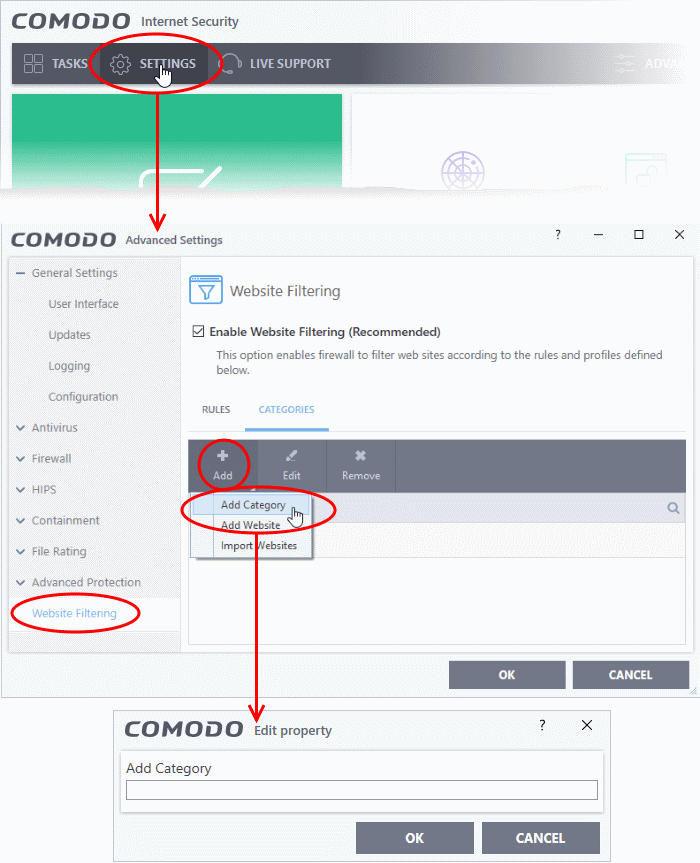
4. Enter a name for the category and click 'OK'. The new category will be listed in the categories tab.
5. Select the new category > Click 'Add' from the options at the top > Choose 'Add Website' from the drop-down. The 'Add Website' dialog will open:
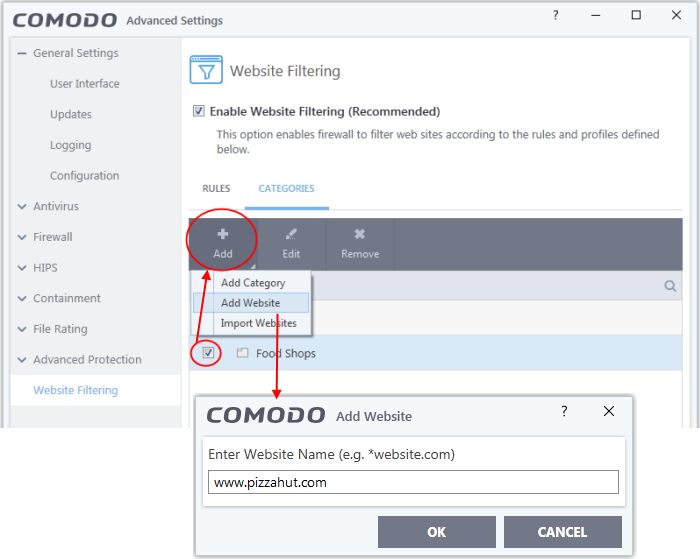
6. Type the website or text string you wish to add to the category. See the following notes for advice on this:
- Enter a FQDN to filter a specific domain. For example, www.example.com
- Place an asterisk in front of the URL to include all sub-domains of the website. For example, *.friskywenches.com will cover friskywenches.com, pictures.friskywenches.com, videos.friskywenches.com and so on. The asterisk is also known as a wildcard character
- Place an asterisk before a keyword to cover all URLs that start with a specific string. For example, "pizza*" will cover 'pizzahut.com', pizzacorner.com, and so on
- Place asterisks before and after the keyword to cover all sites that contain the string. For example, "*pizza*" will cover hotpizzanow.com, spicypizzadishes.net and so on
7. Repeat the process to add more websites to the category.
8. Repeat the process to add more website categories
9. Click 'OK' in the 'Advanced Settings' interface to save your settings
Create rules to block or allow websites to specific users
1. Click 'Settings' on the CIS home screen.2. Click 'Website Filtering' on the left.
3. Ensure that the 'Enable Website Filtering' checkbox is selected.
4. Click the 'Rules' tab and click 'Add' from the options at the top. The 'Website Filtering Rule' dialog will be opened.
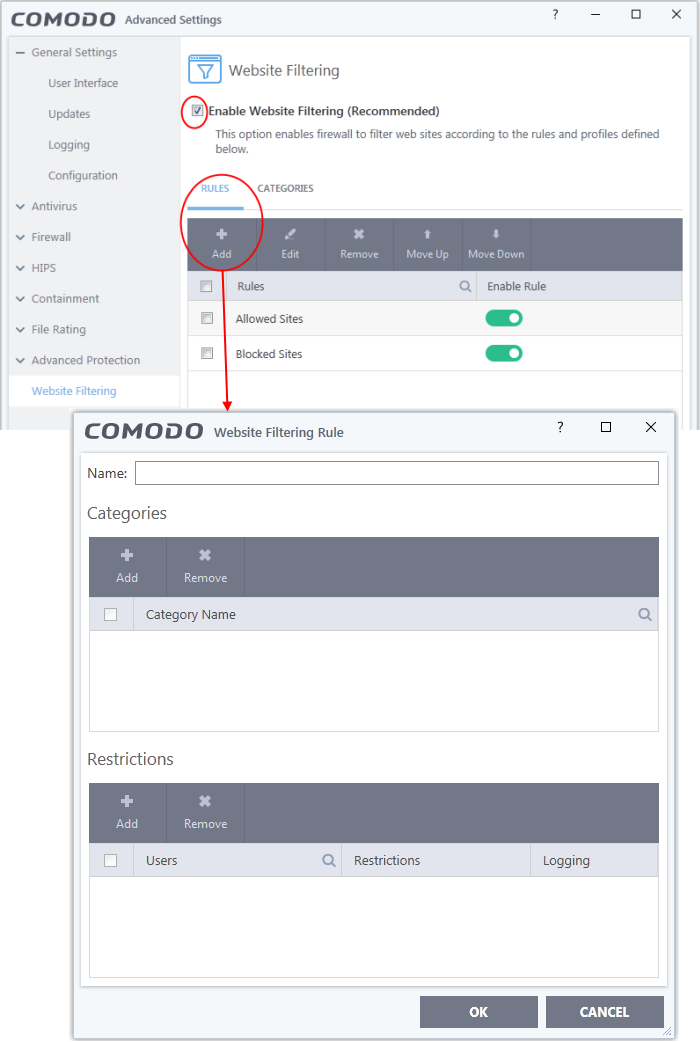
5. Enter a name for your new filter in the 'Website Filtering Rule' dialog.
6. Select the categories that should be added to the filter:
- Click 'Add' under the Categories'.
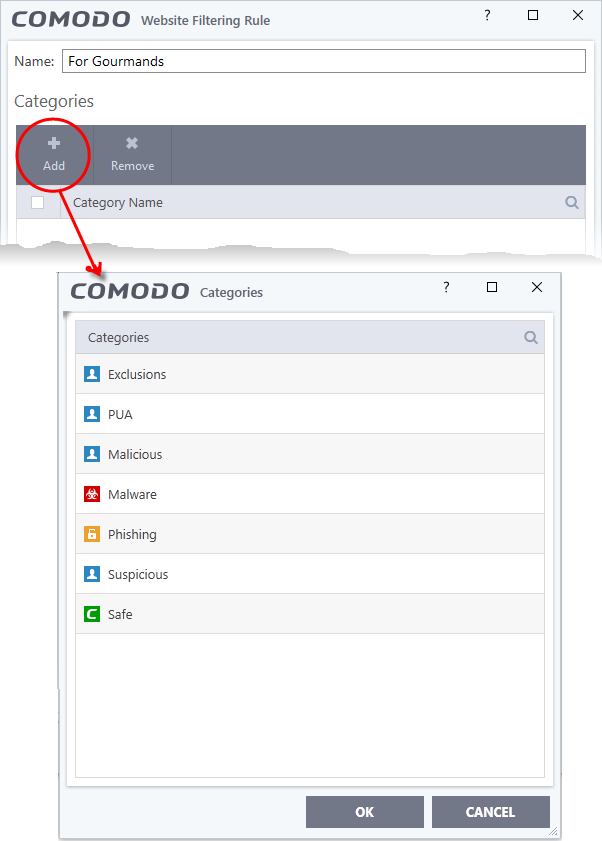
The 'categories' window contains a list pre-defined Comodo categories and any user created categories. Comodo categories cannot be modified.
- Safe Sites - Websites that are considered safe according to the global whitelist
- Phishing Sites - Fake copies of popular banking, shopping and social media websites that intend to steal customer data
- Malware Sites - The URL leads to a direct malware download. Malware is designed to damage your computer, steal sensitive information or gain unauthorized access to your system.
- Exclusions - Websites you have decided to trust and allow connections to for the current session and future sessions.
- PUA Sites - Sites that host'Potentially Unwanted Applications' (PUA). While not strictly speaking malware, a PUA is a piece of software that has functionality that may not have been made clear to a user. An example is a browser toolbar which tells you the weather forecast, but which also tracks your online activity or serves you adverts.
- Malicious Sites - Sites that are known to host or contain links to malware, malicious scripts or deceptive content. These are intended to cause damage to your computer or steal personal data.
- Suspicious Sites - Sites which have shown strong evidence of suspicious behavior but have not yet hosted content which would warrant placing them in the 'Malware' or 'Malicious' categories. Users are advised to be on high alert should they visit these sites.
- Select a category and click 'OK' to add it to your rule. Repeat the process to add more categories.
For more details on creating and modifying categories, see Website Categories.
7. Add Users or User Groups to whom the rule should be applied:
- Click 'Add' from the options at the top beneath the 'Restrictions' pane. The 'Select User or Group' dialog will appear:
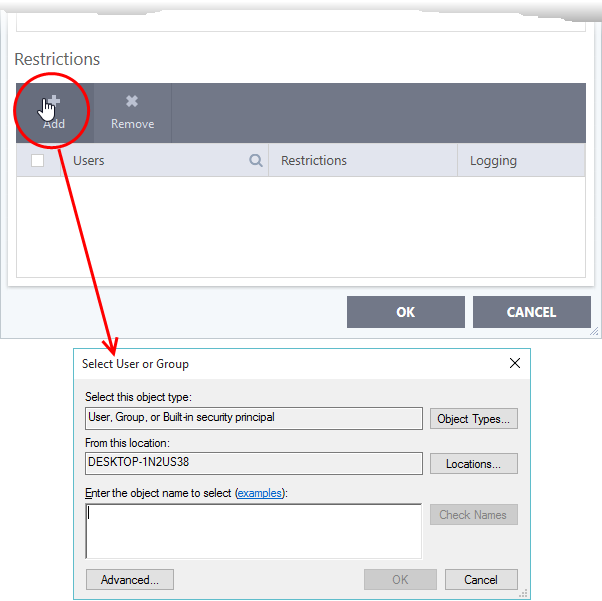
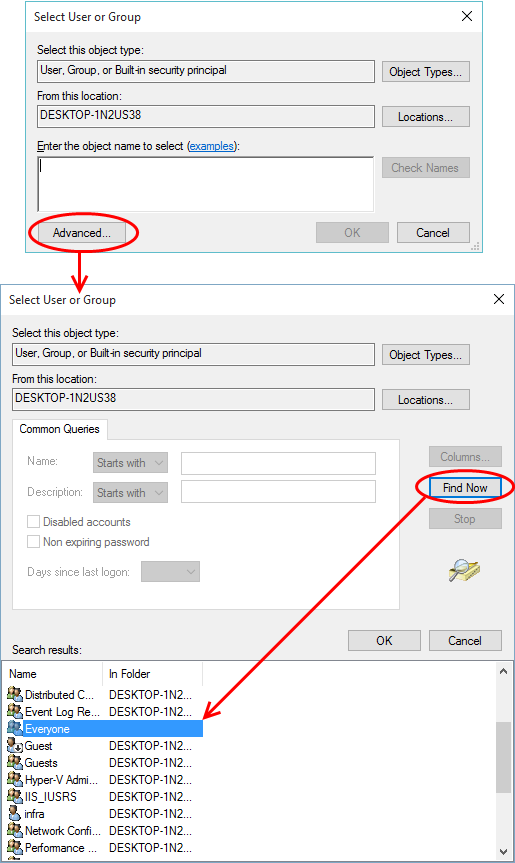
- Enter the names of users to whom the filter should apply in the 'Enter the object name to select' box. Use the format [domain name]/[user/group name] or [user/group name]@[domain name]. Alternatively, click 'Advanced' then 'Find Now' to locate specific users.
- After adding users or groups, you need to specify what restriction will apply to them. You can allow or block them from viewing the websites in the category or ask them if they want to continue. This is done by modifying the link in the 'Restrictions' column:
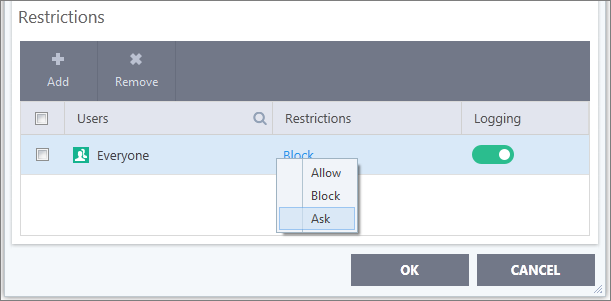
- Allow - The websites in the categories can be accessed by the user.
- Block - The websites in the categories cannot be accessed by the user.
- Ask - An alert will be displayed in the browser if the user tries to access any of the websites in the category. The user can decide whether or not to continue.
- Use the 'Logging' switch to choose whether or not attempts to access a categorized website are logged.
8. Click 'OK' to save your new rule. The new rule will be added to the list of rules under the 'Rules' tab
9. Ensure that the rule is enabled using the toggle switch under the 'Enable Rule' column for the rule to take effect.
You can disable or enable rules at any time using the switch under the 'Enable Rule' column.



