Personal Configurations
Click 'Settings' > 'General Settings' > 'Configuration'
- You can import, export, activate and manage your custom CIS configurations
- Exported Configuration profiles have the file extension .cfgx
- See the following sections for more information:
Export a stored configuration to a file
- Click 'Settings' on the CIS home screen
- Click 'General Settings' > 'Configuration'
- Select a configuration profile then click 'Export'
- If there are any unsaved changes to the current configuration then you can save them before exporting:
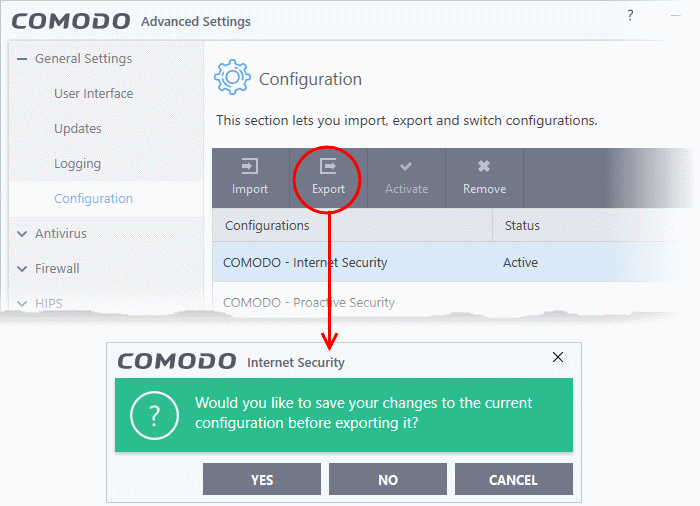
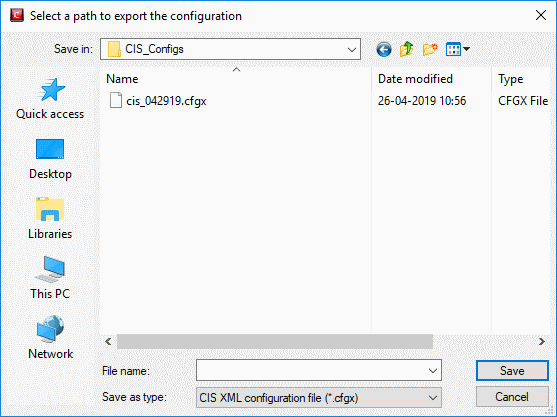
- Next, browse to the location where you want to save the configuration file
- Create a name for the profile. For example, 'My CIS Settings', or 'CIS Highest Security Settings'
- Click 'Save':
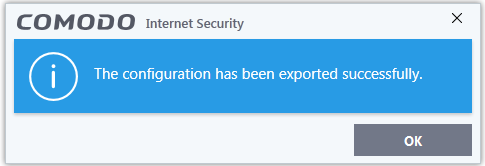
A confirmation dialog will appear if the export is successful:
Import a saved configuration from a file
- You can import a CIS configuration file by clicking the 'Import' button
- Note - any profile you import will not become active until you select them for use
Import a profile
- Click 'Settings' at the top of the CIS home screen
- Click 'General Settings' > 'Configuration' on the left
- Click the 'Import' button:
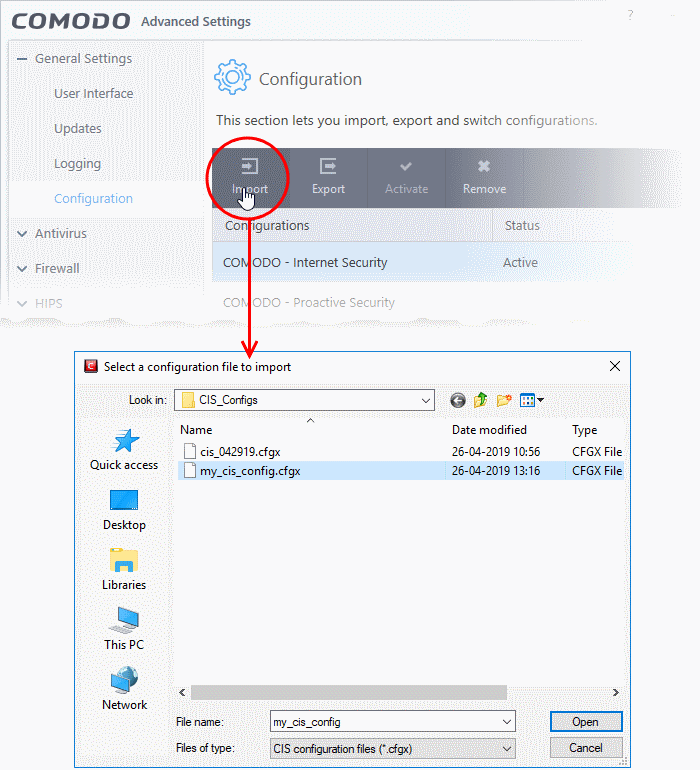
- Navigate to the location of the saved profile and click 'Open'. Configuration files have a .cfgx extension
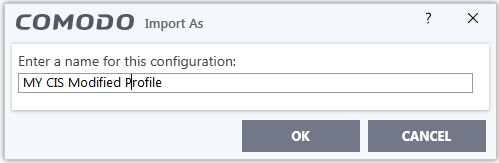
- Enter a name for the profile you wish to import and click 'OK'
A confirmation dialog will appear indicating the successful import of the profile.
Once imported, the configuration profile can be re-exported or deployed in the current installation by making it active.
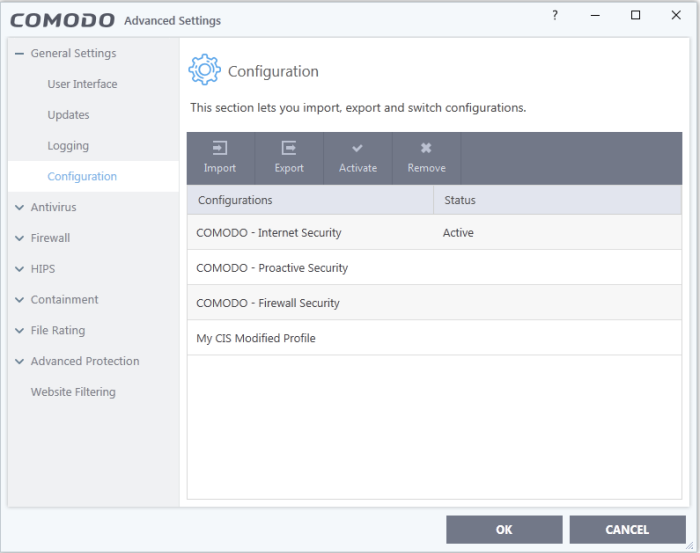
Select and Implement a different configuration profile
You can change the active configuration profile at any time from the 'Configurations' panel.
Change the active configuration profile
- Click 'Settings' at the top of the CIS home screen
- Click 'General Settings' > 'Configuration' on the left
- Choose the profile you want to enable and click the 'Activate' button:
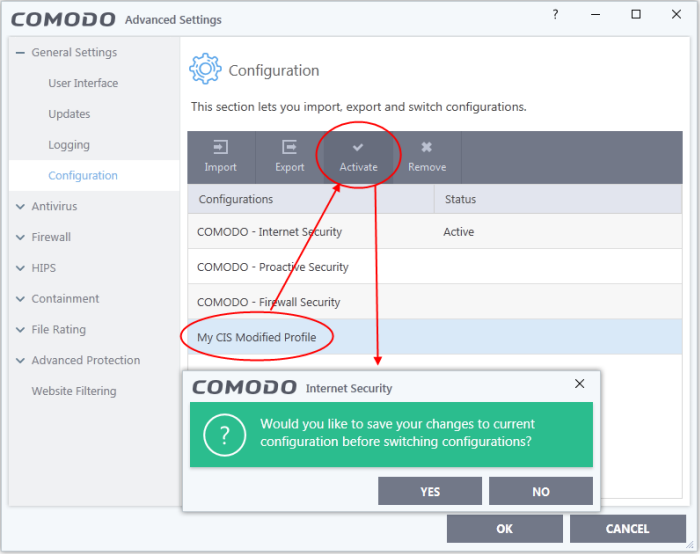
-
Click 'Yes' to save any setting changes in the current configuration, else click 'No'
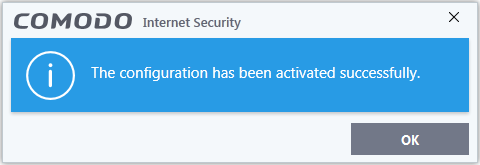
An activation confirmation dialog will be displayed.
Your new profile will be set active. If you are switching to 'Comodo Proactive Security' profile from a different profile or switching to any other profile from 'Comodo Proactive Security' profile, your computer needs to be restarted for the new profile to be activated. 'A Restart Computer' dialog will appear at the bottom right of the screen.
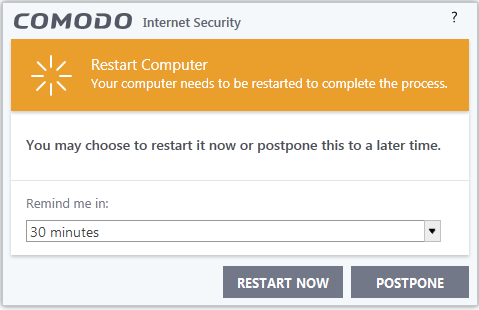
- If your want to restart the computer immediately, save all your work and click 'Restart Now'
- If you want to restart the computer at a later time, select when you need to be reminded from the drop-down and click 'Postpone'
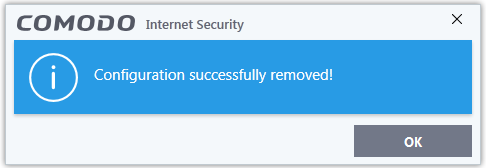
Remove an inactive configuration profile
You can remove any unwanted configuration profiles from the list. You cannot delete the currently active profile, only the inactive ones.
- Click 'Settings' on the CIS home screen
- Click 'General Settings' > 'Configuration'
- Choose the configuration profile you want to delete then click the 'Remove' button
A confirmation dialog appears:
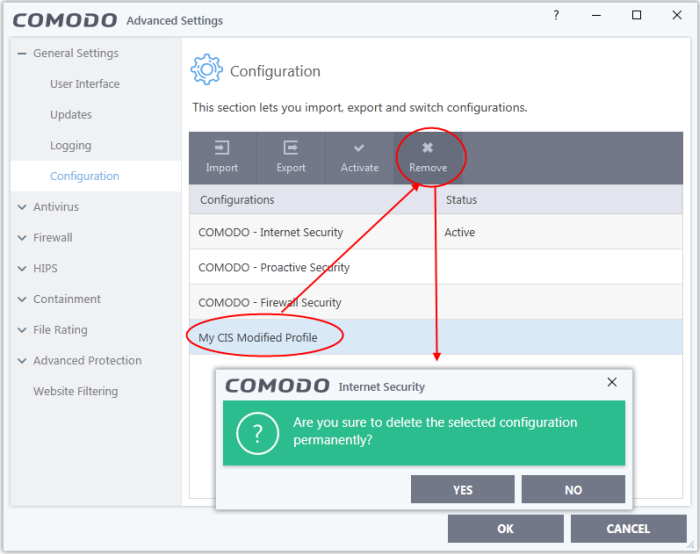
- Click
'Yes'. The configuration
profile will be deleted