Containment Configuration
- If CIS encounters a file that has a trust rating of 'Unknown' then you have the option to automatically run that file in the container.
- The container is a secure, virtual environment where unknown files can run, but cannot affect the rest of your computer.
Files in the container are isolated from other processes, write to a virtual file system and registry, and cannot access your user data.
- Shared Space - Applications in the container cannot save files to your local file system. Because of this, CIS creates a special folder at 'C:/ProgramData/Shared Space' for you to save files created or downloaded in the container. You can access files in this folder from your local desktop.
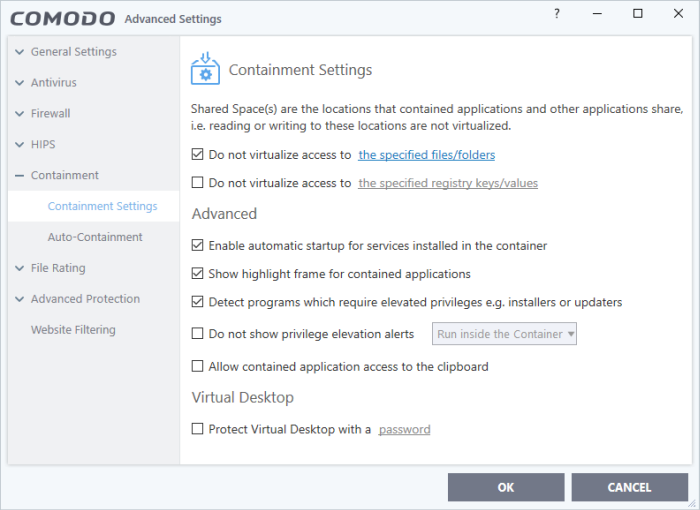
- The
containment settings area lets you configure all aspects of the container:
See the following sections for more help:
- Containment Settings - Configure exceptions to virtualization and other general settings
- Auto-Containment Rules - Create and manage rules which tell CIS how to handle unknown files
- Containment - An Overview - Background information about the containment process
- Unknown
Files: The Scanning Processes - Background information on how
CIS determines the reputation of a file
|
Note: The containment feature is not supported on the following platforms:
|



